A risk group that pursues crypto mining and dispersed denial-of-support (DDoS) attacks has been connected to a new botnet called Enemybot, which has been identified enslaving routers and Internet of Points (IoT) units considering the fact that previous month.
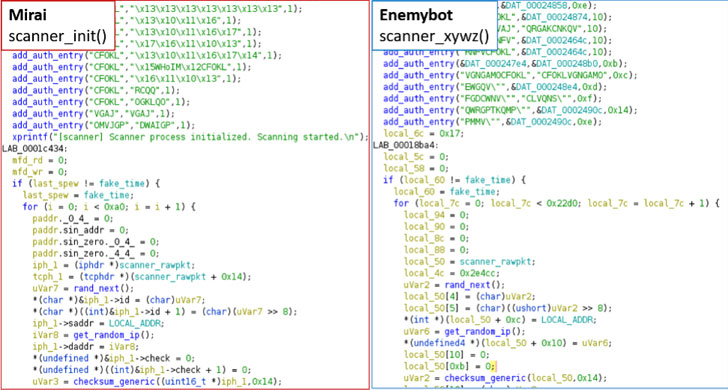
“This botnet is mostly derived from Gafgyt’s source code but has been observed to borrow numerous modules from Mirai’s unique resource code,” Fortinet FortiGuard Labs explained in a report this week.
The botnet has been attributed to an actor named Keksec (aka Kek Security, Necro, and FreakOut), which has been connected to various botnets such as Simps, Ryuk (not to be confused with the ransomware of the very same title), and Samael, and has a heritage of targeting cloud infrastructure to carry out crypto mining and DDoS operations.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Generally concentrating on routers from Seowon Intech, D-Link, and iRZ to propagate its infections and improve in quantity, an examination of the malware specimen has highlighted Enemybot’s obfuscation attempts to hinder evaluation and hook up to a distant server that is hosted in the Tor anonymity network to fetch attack commands.
Enemybot, like the other botnet malware, is the final result of combining and modifying the source code of Mirai and Gafgyt, with the most current version working with the former’s scanner and bot killer modules that are used to scan and terminate competitor procedures functioning on the exact units.
Some of the n-working day vulnerabilities utilized by the botnet to infect a lot more units are as follows –
- CVE-2020-17456 (CVSS score: 9.8) – A remote code execution flaw in Seowon Intech SLC-130 And SLR-120S equipment.
- CVE-2018-10823 (CVSS rating: 8.8) – An arbitrary code execution vulnerability in D-Url routers
- CVE-2022-27226 (CVSS rating: 8.8) – A cross-web page ask for forgery issue impacting iRZ Mobile Routers top to remote code execution
Fortinet also pointed out its overlaps with Gafgyt_tor, suggesting that “Enemybot is very likely an up to date and ‘rebranded’ variant of Gafgyt_tor.”
The disclosure comes as scientists from Qihoo 360’s Network Security Study Lab (360 Netlab) thorough a quickly spreading DDoS botnet termed Fodcha that has ensnared additional than 10,000 day by day active bots, cumulatively infecting in excess of 62,000 exclusive bots from March 29 to April 10, 2022.
Fodcha has been noticed spreading via acknowledged vulnerabilities in Android, GitLab (CVE-2021-22205), Realtek Jungle SDK (CVE-2021-35394), digital video recorders from MVPower, LILIN, and routers from TOTOLINK and ZHONE.
Uncovered this article intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to read more exclusive articles we put up.
Some pieces of this write-up are sourced from:
thehackernews.com



 Critical security flaw discovered in NFT marketplace Rarible
Critical security flaw discovered in NFT marketplace Rarible