Researchers have determined purposeful similarities between a malicious element used in the Raspberry Robin infection chain and a Dridex malware loader, further strengthening the operators’ connections to the Russia-based Evil Corp team.
The findings suggest that “Evil Corp is very likely using Raspberry Robin infrastructure to have out its attacks,” IBM Security X-Force researcher Kevin Henson stated in a Thursday examination.
Raspberry Robin (aka QNAP Worm), initial identified by cybersecurity business Pink Canary in September 2021, has remained one thing of a secret for almost a yr, partly owing to the recognizable deficiency of article-exploitation activities in the wild.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

That altered in July 2022 when Microsoft disclosed that it observed the FakeUpdates (aka SocGholish) malware remaining sent via current Raspberry Robin infections, with opportunity connections recognized concerning DEV-0206 and DEV-0243 (aka Evil Corp).
The malware is regarded to be shipped from a compromised program by means of contaminated USB equipment made up of a destructive .LNK file to other gadgets in the concentrate on network. The Windows Shortcut information are made to retrieve a destructive DLL from a distant server.
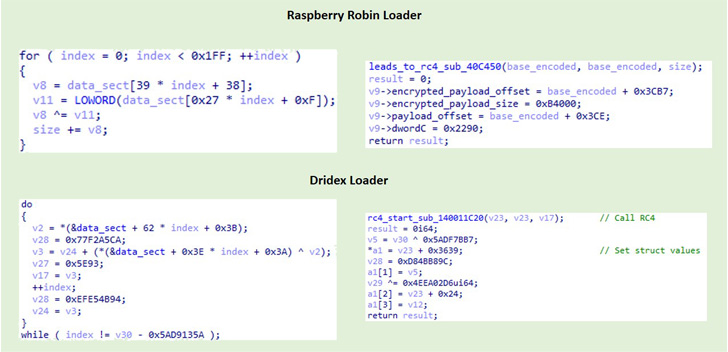
“The Raspberry Robin loaders are DLLs that decode and execute an intermediate loader,” Henson explained. “The intermediate loader performs hook detection as an anti-investigation technique, decodes its strings at runtime and then decodes a extremely obfuscated DLL whose intent has not been established.”
Also, IBM Security X-Force’s comparative assessment of a 32-bit Raspberry Robin loader and a 64-little bit Dridex loader uncovered overlaps in performance and construction, with equally parts incorporating similar anti-investigation code and decoding the remaining payload in an analogous fashion.

Dridex (aka Bugat or Cridex) is the handiwork of Evil Corp and refers to a banking trojan with capabilities to steal information, deploy more malware these as ransomware, and enslave compromised Windows devices into a botnet.
To mitigate Raspberry Robin bacterial infections, it really is suggested that corporations keep an eye on USB gadget connections and disable the AutoRun attribute in the Windows working program options.
Located this report intriguing? Abide by THN on Facebook, Twitter and LinkedIn to go through more unique content material we write-up.
Some elements of this write-up are sourced from:
thehackernews.com

 Podcast transcript: What did we learn from WannaCry?
Podcast transcript: What did we learn from WannaCry?