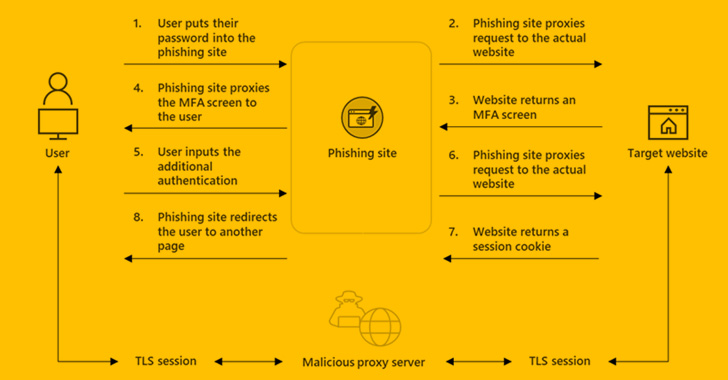
A new phishing-as-a-services (PhaaS) toolkit dubbed EvilProxy is staying advertised on the legal underground as a indicates for threat actors to bypass two-factor authentication (2FA) protections utilized towards on the web services.
“EvilProxy actors are using reverse proxy and cookie injection solutions to bypass 2FA authentication – proxifying victim’s session,” Resecurity scientists mentioned in a Monday create-up.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The platform generates phishing inbound links that are nothing but cloned web pages made to compromise consumer accounts affiliated with Apple iCloud, Facebook, GoDaddy, GitHub, Google, Dropbox, Instagram, Microsoft, NPM, PyPI, RubyGems, Twitter, Yahoo, and Yandex, amid some others.
EvilProxy is equivalent to adversary-in-the-middle (AiTM) attacks in that customers interact with a malicious proxy server that functions as a go-among consumers and the goal website, covertly harvesting the credentials and 2FA passcodes entered in the login internet pages.
It is available on a membership basis for each company for a time time period of 10, 20, or 31 times, with the kit obtainable for $400 a month and accessed about the TOR anonymity network after the payment is arranged manually with an operator on Telegram. Attacks versus Google accounts, in contrast, cost up to $600 for every thirty day period.
EvilProxy (Phishing-as-a-Support) – Google 2FA from Resecurity on Vimeo.
“Immediately after activation, the operator will be asked to provide SSH credentials to more deploy a Docker container and a established of scripts,” Resecurity explained, incorporating the method mirrors that of another PhaaS service termed Frappo that came to mild earlier this 12 months.

Though the sale of EvilProxy to prospective clients is matter to vetting by the actors, it goes without the need of saying that the service features a “cost-effective and scalable alternative” to have out social engineering attacks.
The growth is more an indication that adversaries are upgrading their attack arsenal to orchestrate sophisticated phishing campaigns targeting consumers in a manner that can defeat existing security safeguards.
To add to the issues, the focusing on of community-struggling with code and deal repositories such as GitHub, NPM, PyPI, and RubyGems suggests that the operators are also aiming to facilitate provide chain attacks by way of these kinds of functions.
Getting unauthorized access to accounts and injecting destructive code into extensively utilised jobs by trusted developers can be a goldmine for danger actors, substantially widening the affect of the strategies.
“It can be remarkably most likely the actors intention to goal software program developers and IT engineers to get obtain to their repositories with the conclusion target to hack ‘downstream’ targets,” the scientists mentioned.
Discovered this short article fascinating? Adhere to THN on Fb, Twitter and LinkedIn to go through a lot more distinctive written content we publish.
Some components of this post are sourced from:
thehackernews.com

 Researchers Find New Android Spyware Campaign Targeting Uyghur Community
Researchers Find New Android Spyware Campaign Targeting Uyghur Community