A freshly found out botnet able of staging dispersed denial-of-support (DDoS) attacks specific unpatched Ribbon Communications (previously Edgewater Networks) EdgeMarc appliances belonging to telecom services service provider AT&T by exploiting a 4-year-previous flaw in the network appliances.
Chinese tech huge Qihoo 360’s Netlab network security division, which detected the botnet very first on October 27, 2021, identified as it EwDoor, noting it observed 5,700 compromised IP addresses situated in the U.S. through a short three-hour window.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
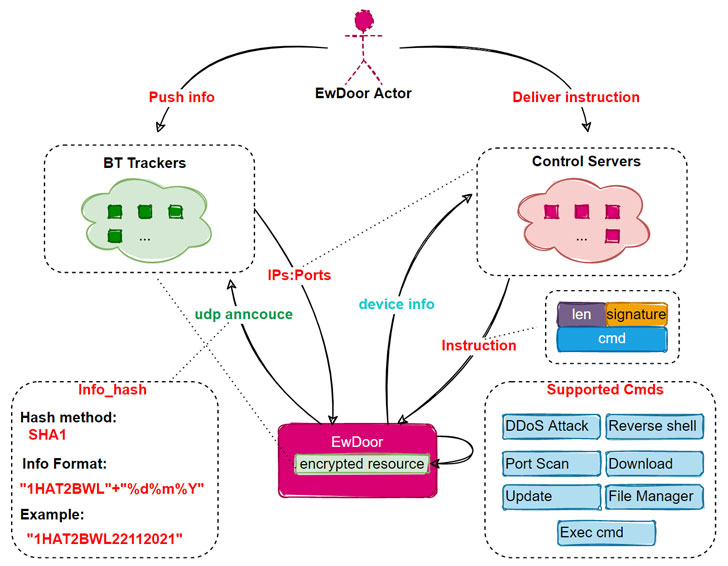
“So considerably, the EwDoor in our see has undergone 3 variations of updates, and its primary features can be summarized into two principal types of DDoS attacks and backdoor,” the scientists famous. “Primarily based on the attacked products are phone interaction relevant, we presume that its main objective is DDoS attacks, and accumulating of sensitive details, this kind of as call logs.”
Propagating through a flaw in EdgeMarc devices, EwDoor supports a variety of characteristics, which includes the capability to self-update, download information, get hold of a reverse shell on the compromised equipment, and execute arbitrary payloads. The vulnerability in query is CVE-2017-6079 (CVSS score: 9.8), a command injection flaw affecting the session border controllers that could be weaponized to execute malicious commands.

EwDoor, other than accumulating details about the infected technique, also establishes communications with a remote command-and-handle (C2) server, both specifically or indirectly utilizing BitTorrent Trackers to fetch the C2 server IP deal with, to await more instructions issued by the attackers.
We have attained out to AT&T for remark, and we will update the story when we hear back again. More indicators of compromise linked with the marketing campaign can be accessed right here.
Observed this short article intriguing? Comply with THN on Facebook, Twitter and LinkedIn to examine far more exclusive content material we publish.
Some pieces of this short article are sourced from:
thehackernews.com


 Business School Dean Guilty of Data Conspiracy
Business School Dean Guilty of Data Conspiracy