Commercially created FinFisher surveillanceware has been upgraded to infect Windows devices making use of a UEFI (Unified Extensible Firmware Interface) bootkit applying a trojanized Windows Boot Supervisor, marking a shift in an infection vectors that enable it to elude discovery and assessment.
Detected in the wild since 2011, FinFisher (aka FinSpy or Wingbird) is a spyware toolset for Windows, macOS, and Linux made by Anglo-German agency Gamma Worldwide and supplied exclusively to legislation enforcement and intelligence agencies. But like with NSO Group’s Pegasus, the software program has also been made use of to spy on Bahraini activists in the past allegedly and sent as section of spear-phishing campaigns in September 2017.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
FinFisher is geared up to harvest person qualifications, file listings, sensitive paperwork, report keystrokes, siphon email messages from Thunderbird, Outlook, Apple Mail, and Icedove, intercept Skype contacts, chats, phone calls and transferred data files, and seize audio and online video by getting access to a machine’s microphone and webcam.
Even though the resource was formerly deployed through tampered installers of reputable applications this kind of as TeamViewer, VLC, and WinRAR that have been backdoored with an obfuscated downloader, subsequent updates in 2014 enabled infections by using Grasp Boot Record (MBR) bootkits with the intention of injecting a destructive loader in a method which is engineered to slip past security equipment.
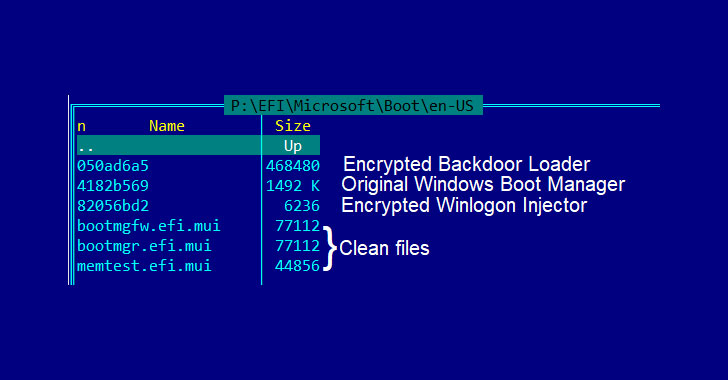
The most current element to be added is the ability to deploy a UEFI bootkit to load FinSpy, with new samples exhibiting properties that changed the Windows UEFI boot loader with a destructive variant as nicely as boasting of four layers of obfuscation and other detection-evasion methods to gradual down reverse engineering and investigation.
“This way of an infection allowed the attackers to install a bootkit with out the need to have to bypass firmware security checks,” Kaspersky’s Worldwide Exploration and Evaluation Workforce (Great) stated in a complex deep dive subsequent an 8-month-extensive investigation. “UEFI infections are incredibly rare and usually difficult to execute, they stand out owing to their evasiveness and persistence.”

UEFI is a firmware interface and an improvement about basic input/output process (BIOS) with help for Safe Boot, which assures the integrity of the running program to ensure no malware has interfered with the boot course of action. But because UEFI facilitates the loading of the working method alone, bootkit infections are not only resistant to OS reinstallation or substitute of the challenging drive but are also inconspicuous to security solutions operating within the working program.
This permits risk actors to have command above the boot approach, realize persistence, and bypass all security defences. “Though in this situation the attackers did not infect the UEFI firmware by itself, but its future boot stage, the attack was specially stealthy, as the destructive module was installed on a independent partition and could management the boot procedure of the infected equipment,” the researchers additional.
Found this post appealing? Abide by THN on Fb, Twitter and LinkedIn to browse a lot more distinctive content we publish.
Some sections of this write-up are sourced from:
thehackernews.com

 Cyber-attack Floors British Payroll Firm
Cyber-attack Floors British Payroll Firm