A novel procedure leverages optical emanations from a device’s electrical power indicator LED to get well appears from related peripherals and spy on electronic discussions from a distance of as a great deal as 35 meters.
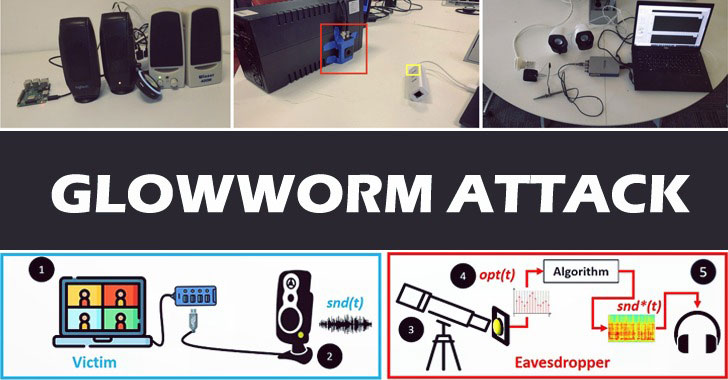
Dubbed the “Glowworm attack,” the conclusions were being posted by a team of lecturers from the Ben-Gurion University of the Negev earlier this 7 days, describing the approach as “an optical TEMPEST attack that can be utilised by eavesdroppers to get well seem by analysing optical measurements received by means of an electro-optical sensor directed at the energy indicator LED of several products.”
Accompanying the experimental setup is an optical-audio transformation (OAT) that makes it possible for for retrieving audio by isolating the speech from the optical measurements acquired by directing an electro-optical sensor at the device’s energy indicator LED.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

TEMPEST is the codename for unintentional intelligence-bearing emanations manufactured by digital and electromechanical information-processing gear.
Glowworm builds on a related attack named Lamphone that was shown by the exact scientists very last yr and allows the recovery of seem from a victim’s home that is made up of an overhead hanging bulb.
While the two methods retrieve audio from light-weight by means of an electro-optical sensor, they are also unique in that although the Lamphone attack “is a facet-channel attack that exploits a light-weight bulb’s miniscule vibrations, which are the result of seem waves hitting the bulb,” Glowworm is a “TEMPEST attack that exploits the way that electrical circuits had been built. It can recuperate audio from units like USB hub splitters that do not go in reaction to the acoustic information and facts played by the speakers.”
The attack hinges on the optical correlation among the seem that is performed by related speakers and the intensity of their ability indicator LED, which are not only linked directly to the ability line but also that the intensity of a device’s power indicator LED is motivated by the electric power use. What is actually far more, the quality of the audio recovered is proportional to the good quality of the devices used by the eavesdropper.
In a real-environment scenario, the danger design will take goal at the speech produced by participants in a digital assembly platform such as Zoom, Google Meet, and Microsoft Teams, with the malicious party situated in a space in an adjacent making, enabling the adversary to recover sound from the power indicator LED of the speakers.

In an oblique attack state of affairs in which the electricity indicator LED is just not visible from outdoors the room, the eavesdropper can recuperate seem from the electric power indicator LED of the gadget used to deliver the electrical power to the speaker.
Even though this sort of attacks can be countered on the purchaser side by positioning a black tape over a device’s electric power indicator LED, the researchers recommend product makers to combine a capacitor or an operational amplifier to eradicate the energy usage fluctuations that happen when the speakers generate sound.
“Even though the expense of our countermeasures might seem to be negligible, presented the likelihood that the gadgets are mass made, the addition of a component to prevent the attack could price a producer millions of dollars,” the scientists reported. “Specified the price-driven nature of shoppers and the profit-driven nature of suppliers, identified vulnerabilities are typically ignored as a signifies of lessening fees. This truth could leave a lot of electrical circuits vulnerable to Glowworm attack for a long time to come.”
Observed this report fascinating? Follow THN on Fb, Twitter and LinkedIn to study much more unique content material we publish.
Some parts of this article are sourced from:
thehackernews.com

 Learn Ethical Hacking From Scratch — 18 Online Courses for Just $43
Learn Ethical Hacking From Scratch — 18 Online Courses for Just $43