Weaknesses in e-commerce portals are being exploited to deploy a Linux backdoor as effectively as a credit score card skimmer that is able of stealing payment data from compromised web sites.
“The attacker started out with automated e-commerce attack probes, tests for dozens of weaknesses in popular on the web retail outlet platforms,” scientists from Sansec Menace Investigation mentioned in an investigation. “Soon after a working day and a 50 percent, the attacker discovered a file add vulnerability in a single of the store’s plugins.” The identify of the influenced vendor was not discovered.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
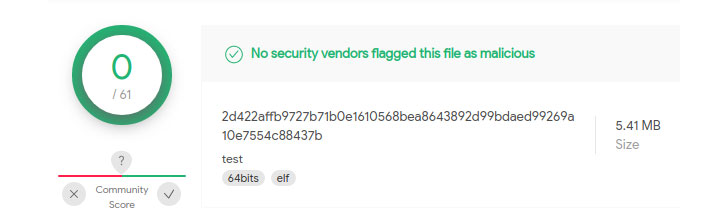
The initial foothold was then leveraged to upload a malicious web shell and alter the server code to siphon purchaser details. Also, the attacker delivered a Golang-centered malware termed “linux_avp” that serves as a backdoor to execute commands remotely despatched from a command-and-manage server hosted in Beijing.
On execution, the method is developed to remove itself from the disk and camouflage as a “ps -ef” course of action, which is a utility for exhibiting currently-working procedures in Unix and Unix-like operating units.

The Dutch cybersecurity company explained it also learned a PHP-coded web skimmer that is disguised as a favicon impression (“favicon_absolute_major.jpg”) and extra to the e-commerce platform’s code with the intention of injecting fraudulent payment kinds and stealing credit history card facts entered by customers in authentic-time, right before transmitting them to a distant server.
On top of that, Sansec scientists said the PHP code was hosted on a server situated in Hong Kong and that it was previously utilised as a “skimming exfiltration endpoint in July and August of this calendar year.”
Uncovered this report appealing? Follow THN on Fb, Twitter and LinkedIn to study extra special content we submit.
Some pieces of this write-up are sourced from:
thehackernews.com


 Wind turbine maker Vestas hit by cyber attack
Wind turbine maker Vestas hit by cyber attack