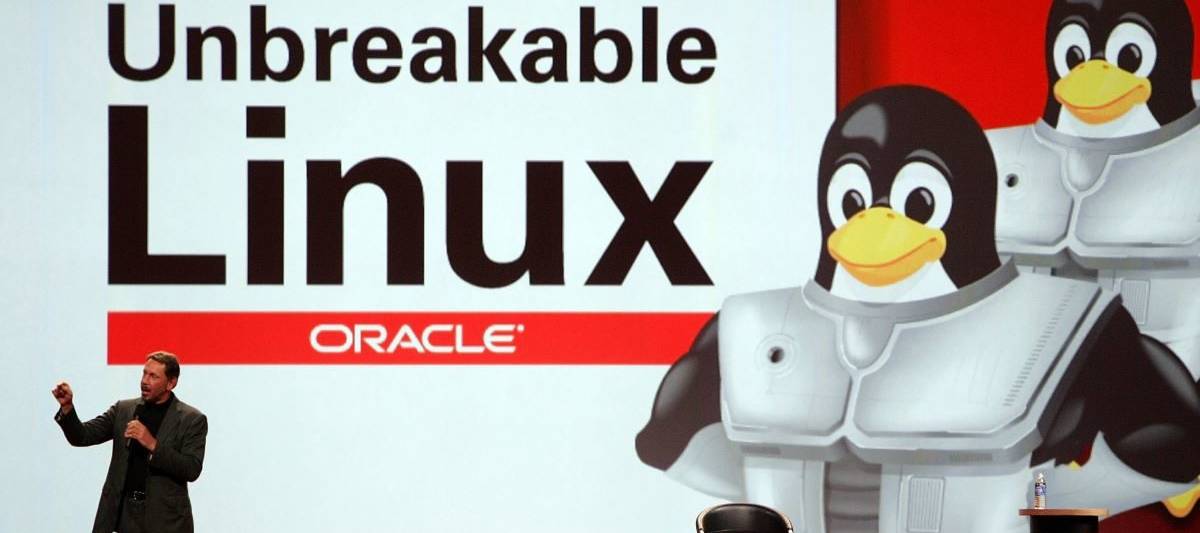
Oracle Co-Founder Larry Ellison delivers a keynote deal with at the Oracle OpenWorld meeting in 2006. A freshly identified worm turns Windows and Linux servers into cryptocurrency miners. (Justin Sullivan/Getty Visuals)
A new worm published in Golang turns Windows and Linux servers into miners of the cryptocurrency monero.
In a Wednesday website article, scientists from Intezer mentioned the worm spreads throughout the network to operate XMRig Miner – a monero cryptocurrency miner – on a large scale. The malware then targets both of those Windows and Linux servers and can easily maneuver from a person platform to the other. It targets community-experiencing providers this sort of as MySQL, Tomcat admin panel and Jenkins that have weak passwords. In an more mature version, the worm has also attempted to exploit WebLogic’s most current vulnerability: CVE-2020-14882.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
All through their analysis, the researchers identified that the attacker kept updating the worm on the command and handle server, which implies that it’s energetic and could be targeting additional weak configured solutions in upcoming updates.
The attack makes use of 3 data files: a dropper script (bash or powershell), a Golang binary worm, and an XMRig Miner—all of which are hosted on the same command and command server.
Security teams have been advised to use advanced passwords, restrict login makes an attempt and use two-factor authentication. Intezer also claims to minimize the use of general public- dealing with companies and continue to keep computer software updated with the newest security patches. Ultimately, they advocate utilizing a cloud workload safety platform to obtain full runtime visibility above the code in the company’s method and for obtaining alerted on any destructive or unauthorized code.
Dirk Schrader, international vice president at New Net Technologies, explained that miners on servers are frequently viewed as a nuisance, a little something that security execs have to handle. Nevertheless, for the attackers, specially in this circumstance, Schrader explained the probable variety of devices is staggering: In accordance to Shodan, there are 5.5 million MySQL, Tomcat, Jenkins, and WebLogic equipment related to the internet.
“It’s simple math, if only .1 percent of the programs are inclined to the attack, there’s a good deal of server energy to use for mining and funds era, afterwards to be utilized for other nefarious perform by the cyber criminals,” Schrader explained. “Protection against that sort of attack is accomplished in the identical way as with other types of attacks. Organizations need to observe their methods for vulnerabilities to patch them in time, regulate any modifications going on to a server like a file getting dropped and have a robust password plan in put.”
Some sections of this short article are sourced from:
www.scmagazine.com

 Cerberus Cyber Sentinel buys Alpine Security
Cerberus Cyber Sentinel buys Alpine Security