Google has launched an up to date model of Scorecards, its automatic security device that makes a “risk rating” for open up source initiatives, with improved checks and abilities to make the details generated by the utility accessible for evaluation.
“With so substantially software package nowadays relying on open up-supply initiatives, people want an quick way to decide whether or not their dependencies are risk-free,” Google’s Open up Resource Security Team mentioned Thursday. “Scorecards aids decrease the toil and guide effort and hard work expected to frequently appraise switching offers when maintaining a project’s provide chain.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Scorecards aims to automate examination of the security posture of open source assignments as perfectly as use the security wellbeing metrics to proactively enhance the security posture of other critical projects. To date, the software has been scaled up to consider security requirements for about 50,000 open source initiatives.
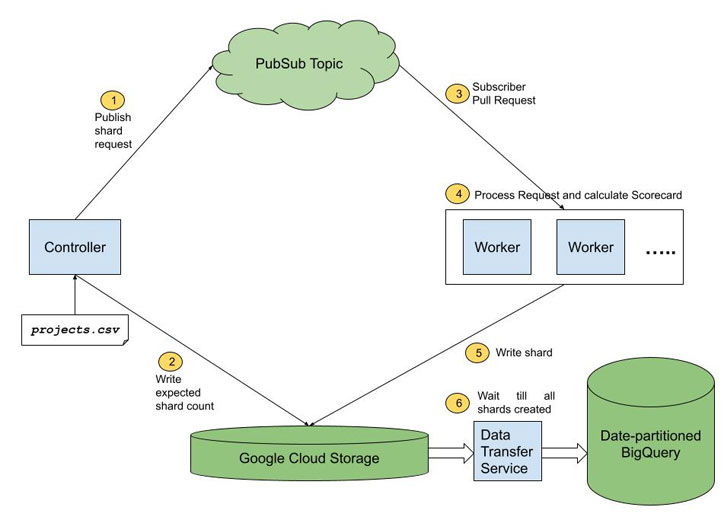
Some of the new additions incorporate checks for contributions from malicious authors or compromised accounts that can introduce probable backdoors into code, use of fuzzing (e.g., OSS-Fuzz), and static code assessment applications (e.g., CodeQL), symptoms of CI/CD compromise, and undesirable dependencies.
“Pinning dependencies is helpful all over the place we have dependencies: not just all through compilation, but also in Dockerfiles, CI/CD workflows, and so forth,” the staff reported. “Scorecards checks for these anti-styles with the Frozen-Deps check. This check out is valuable for mitigating from destructive dependency attacks this kind of as the modern CodeCov attack.”

Google also pointed out that a significant variety of analyzed tasks are not consistently fuzzed, and that neither do they outline a security plan for reporting vulnerabilities nor do they pin dependencies, while also underscoring the will need to boost the security of these critical jobs and travel consciousness of the widespread security dangers.
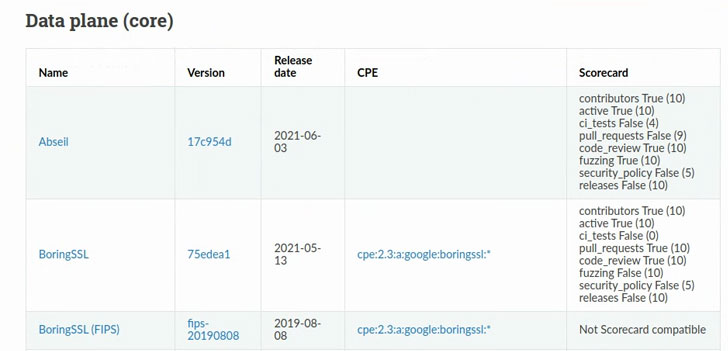 Sample Scorecard Final results
Sample Scorecard Final results
The launch of Scorecards v2 arrives months following the enterprise previewed an stop-to-stop framework known as “Source chain Degrees for Program Artifacts” (or SLSA) to ensure the integrity of software artifacts and stop unauthorized modifications in excess of the program of the enhancement and deployment pipeline.
Uncovered this report interesting? Comply with THN on Fb, Twitter and LinkedIn to read through additional distinctive articles we write-up.
Some areas of this write-up are sourced from:
thehackernews.com

 Instructions on how to exploit Windows Print Spooler accidentally leaked after research blunder
Instructions on how to exploit Windows Print Spooler accidentally leaked after research blunder