A 7 days following the US federal government issued an advisory about a “global intelligence collecting mission” operated by North Korean condition-sponsored hackers, new results have emerged about the menace group’s spy ware abilities.
The APT — dubbed “Kimsuky” (aka Black Banshee or Thallium) and believed to be energetic as early as 2012 — has been now connected to as several as a few hitherto undocumented malware, such as an information stealer, a tool outfitted with malware anti-investigation features, and a new server infrastructure with important overlaps to its more mature espionage framework.
“The team has a prosperous and notorious record of offensive cyber functions all-around the environment, like operations targeting South Korean believe tanks, but about the past couple of a long time they have expanded their targeting to international locations including the United States, Russia and many nations in Europe,” Cybereason scientists mentioned in an evaluation yesterday.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Very last 7 days, the FBI and departments of Defense and Homeland Security jointly released a memo detailing Kimsuky’s techniques, procedures, and treatments (TTPs).
Leveraging spear-phishing and social engineering methods to get the original entry into target networks, the APT has been identified to specifically target folks determined as industry experts in different fields, believe tanks, the cryptocurrency business, and South Korean authorities entities, in addition to posing as journalists from South Korea to send out e-mails embedded with BabyShark malware.
In recent months, Kimsuky has been attributed to a variety of campaigns employing coronavirus-themed email lures that contains weaponized Phrase documents as their an infection vector to attain a foothold on victim devices and launch malware attacks.
“Kimsuky focuses its intelligence collection actions on overseas coverage and countrywide security issues linked to the Korean peninsula, nuclear plan, and sanctions,” the Cybersecurity and Infrastructure Security Company (CISA) explained.
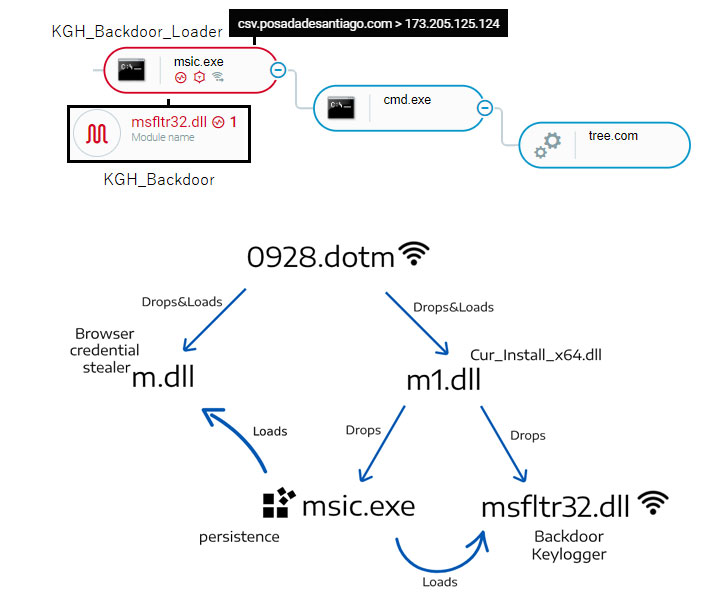
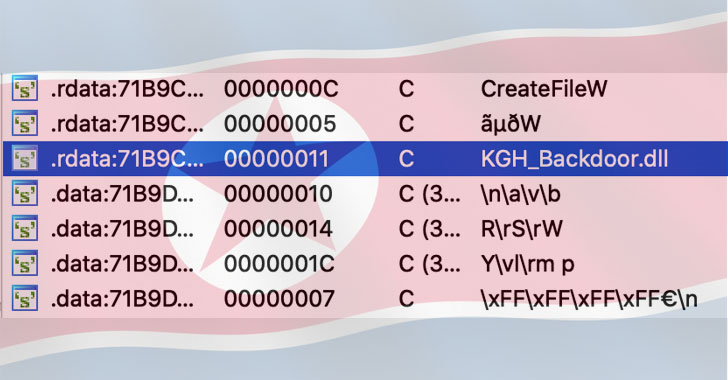
Now according to Cybereason, the risk actor has obtained new capabilities by way of a modular spyware suite termed “KGH_SPY,” allowing it to have out reconnaissance of focus on networks, capture keystrokes, and steal delicate information.
In addition to this, the KGH_SPY backdoor can download secondary payloads from a command-and-manage (C2) server, execute arbitrary instructions via cmd.exe or PowerShell, and even harvest credentials from web browsers, Windows Credential Supervisor, WINSCP and mail shoppers.
Also of notice is the discovery of a new malware named “CSPY Downloader” that is built to thwart assessment and down load further payloads.
Finally, Cybereason researchers unearthed a new toolset infrastructure registered amongst 2019-2020 that overlaps with the group’s BabyShark malware utilised to formerly concentrate on US-centered believe tanks.
“The threat actors invested initiatives in order to continue to be under the radar, by employing a variety of anti-forensics and anti-assessment strategies which integrated backdating the development/compilation time of the malware samples to 2016, code obfuscation, anti-VM and anti-debugging strategies,” the scientists stated.
“Even though the identity of the victims of this marketing campaign remains unclear, there are clues that can suggest that the infrastructure specific organizations working with human rights violations.”
Uncovered this post exciting? Adhere to THN on Facebook, Twitter and LinkedIn to browse additional distinctive material we write-up.
Some pieces of this posting are sourced from:
thehackernews.com

 Industrial IoT connections will reach 37 billion by 2025
Industrial IoT connections will reach 37 billion by 2025