Cybersecurity scientists have found an fully new attack vector that allows adversaries to exploit the Log4Shell vulnerability on servers regionally by using a JavaScript WebSocket link.
“This newly-discovered attack vector usually means that any person with a vulnerable Log4j variation on their device or neighborhood non-public network can look through a website and perhaps induce the vulnerability,” Matthew Warner, CTO of Blumira, claimed. “At this issue, there is no evidence of lively exploitation. This vector considerably expands the attack area and can affect services even operating as localhost which ended up not exposed to any network.”
WebSockets allow for for two-way communications concerning a web browser (or other customer application) and a server, contrary to HTTP, which is unidirectional in which the client sends the ask for and the server sends the response.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Whilst the issue can be settled by updating all regional enhancement and internet-experiencing environments to Log4j 2.16., Apache on Friday rolled out version 2.17., which remediates a denial-of-assistance (DoS) vulnerability tracked as CVE-2021-45105 (CVSS rating: 7.5), building it the third Log 4j2 flaw to appear to light-weight after CVE-2021-45046 and CVE-2021-44228.

The total record of flaws found out to day in the logging framework after the unique distant code execution bug was disclosed is as follows —
- CVE-2021-44228 (CVSS rating: 10.) – A remote code execution vulnerability affecting Log4j versions from 2.-beta9 to 2.14.1 (Set in variation 2.15.)
- CVE-2021-45046 (CVSS rating: 9.) – An facts leak and distant code execution vulnerability influencing Log4j versions from 2.-beta9 to 2.15., excluding 2.12.2 (Mounted in model 2.16.)
- CVE-2021-45105 (CVSS rating: 7.5) – A denial-of-support vulnerability affecting Log4j versions from 2.-beta9 to 2.16. (Set in model 2.17.)
- CVE-2021-4104 (CVSS rating: 8.1) – An untrusted deserialization flaw impacting Log4j version 1.2 (No correct obtainable Enhance to edition 2.17.)
“We should not be amazed that added vulnerabilities had been found in Log4j presented the more precise concentrate on the library,” Jake Williams, CTO and co-founder of incident reaction business BreachQuest, stated. “Related to Log4j, this summer time the primary PrintNightmare vulnerability disclosure led to the discovery of many supplemental distinctive vulnerabilities. The discovery of more vulnerabilities in Log4j should not bring about worry about the security of log4j alone. If something, Log4j is extra secure simply because of the further focus paid by researchers.”
The latest improvement comes as a quantity of danger actors have piled on the Log4j flaws to mount a wide variety of attacks, which includes ransomware bacterial infections involving the Russia-based Conti team and a new ransomware pressure named Khonsari. What is actually extra, the Log4j distant code execution flaw has also opened the doorway to a third ransomware strain acknowledged as TellYouThePass that is currently being made use of in attacks towards Windows and Linux devices, in accordance to researchers from Sangfor and Curated Intel.
Bitdefender Honeypots Sign Active Log4Shell -Working day Attacks Underway
The quickly exploited, ubiquitous vulnerability, aside from spawning as quite a few as 60 variants, has offered a great window of opportunity for adversaries, with Romanian cybersecurity agency Bitdefender noting that a lot more than 50% of the attacks are leveraging the Tor anonymity company to mask their real origins.
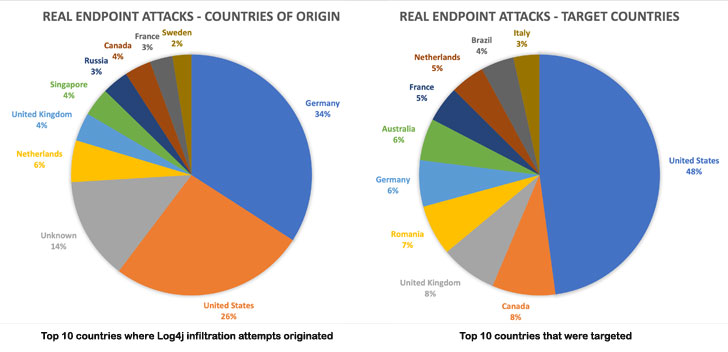
“In other phrases, threat actors exploiting Log4j are routing their attacks as a result of devices that are nearer to their intended targets and just due to the fact we don’t see nations around the world typically associated with cybersecurity threats at the top of the list does not signify that attacks did not originate there,” Martin Zugec, technical options director at Bitdefender, stated.
According to telemetry details collected among December 11 and December 15, Germany and the U.S. on your own accounted for 60% of all the exploitation tries. The most widespread attack targets in the course of the observation time period ended up the U.S., Canada, the U.K., Romania, Germany, Australia, France, the Netherlands, Brazil, and Italy.
Google: Over 35,000 Java Deals Affected by the Log4j Flaw
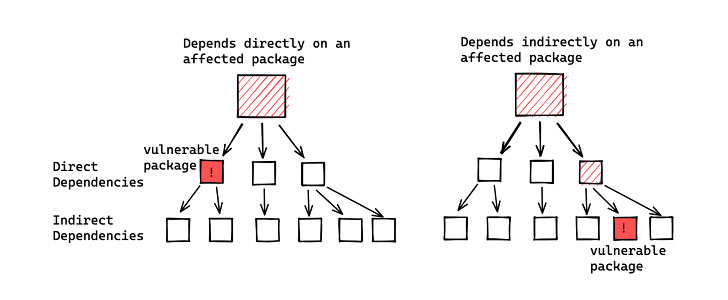
The improvement also coincides with analysis from Google’s Open Source Insights Staff, which discovered that approximately 35,863 Java offers — accounting for over 8% of the Maven Central repository — use vulnerable versions of the Apache Log4j library. Of the afflicted artifacts, only all around 7,000 packages have a immediate dependency on Log4j.
“User’s deficiency of visibility into their dependencies and transitive dependencies has manufactured patching tough it has also produced it difficult to figure out the full blast radius of this vulnerability,” Google’s James Wetter and Nicky Ringland claimed. But on the positive facet of factors, 2,620 of the impacted packages have presently been fixed a lot less than a 7 days following disclosure.
“There will very likely be some time just before we understand the total fallout of the log4j vulnerability, but only simply because it is embedded in so significantly program,” Williams reported. “This has nothing to do with danger actor malware. It has to do with the difficulty in locating the myriad places the library is embedded. The vulnerability by itself will supply initial accessibility for menace actors who will afterwards execute privilege escalation and lateral movement – that’s exactly where the authentic risk is.”
Observed this report exciting? Comply with THN on Fb, Twitter and LinkedIn to study more distinctive articles we submit.
Some areas of this write-up are sourced from:
thehackernews.com



 Apache Issues 3rd Patch to Fix New High-Severity Log4j Vulnerability
Apache Issues 3rd Patch to Fix New High-Severity Log4j Vulnerability