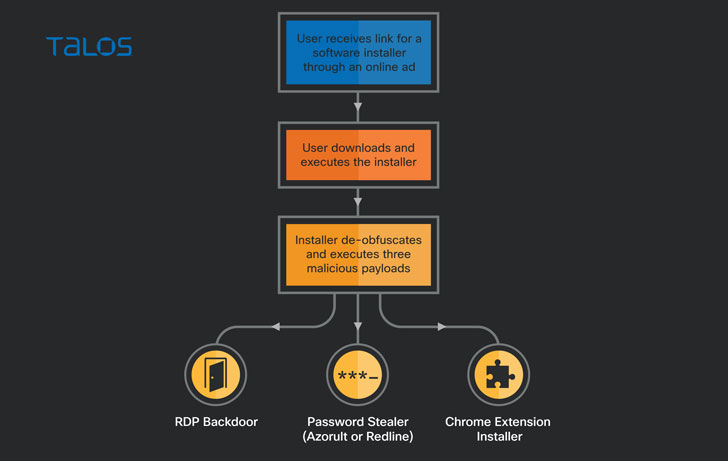
A series of destructive strategies have been leveraging fake installers of preferred apps and game titles these types of as Viber, WeChat, NoxPlayer, and Battlefield as a lure to trick buyers into downloading a new backdoor and an undocumented destructive Google Chrome extension with the intention of stealing credentials and information saved in the compromised units as perfectly as keeping persistent remote obtain.
Cisco Talos attributed the malware payloads to an unidentified actor that goes by the alias “magnat,” noting that “these two family members have been subject matter to regular growth and improvement by their authors.”
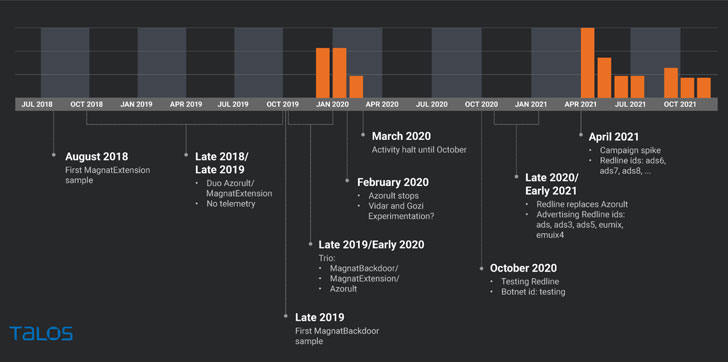
The attacks are considered to have commenced in late 2018, with intermittent activity noticed toward the finish of 2019 and by early 2020, followed by clean spikes due to the fact April 2021, though largely singling out buyers in Canada, followed by the U.S., Australia, Italy, Spain, and Norway.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

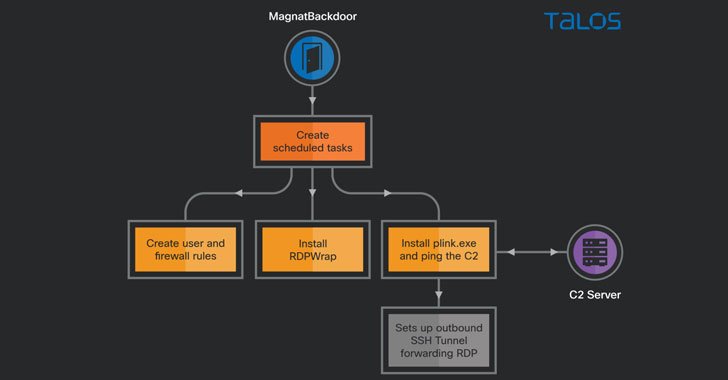
A noteworthy part of the intrusions is the use of malvertising as a signifies to strike men and women who are on the lookout for well known application on look for engines to current them links to download faux installers that fall a password stealer known as RedLine Stealer, a Chrome extension dubbed “MagnatExtension” that is programmed to file keystrokes and capture screenshots, and an AutoIt-dependent backdoor that establishes distant entry to the machine.
MagnatExtension, which masquerades as Google’s Safe and sound searching, also packs other capabilities that are of use to the attackers, like the means to steal variety data, harvest cookies, and execute arbitrary JavaScript code. Telemetry facts analyzed by Talos has exposed that the very first-at any time sample of the browser insert-on was detected in August 2018.
The extension’s command-and-regulate (C2) communications stand out as perfectly. While the C2 address is tough-coded, it can also be up to date by the present C2 with a listing of more C2 domains. But in the party of failure, it falls again to an alternate process that involves obtaining a new C2 deal with from a Twitter search for hashtags like “#aquamamba2019” or “#ololo2019.”

The area title is then built from the accompanying tweet text by concatenating the to start with letter of each word, that means “Squishy turbulent places terminate energetic round engines following dank yrs. Industrial creepy units” becomes “stataready[.]icu.” After an lively C2 server is obtainable, the vacuumed facts is exfiltrated in the form of an encrypted JSON string in the entire body of an HTTP Put up request, the encryption crucial to which is tough-coded in the decryption functionality.
“Centered on the use of password stealers and a Chrome extension that is very similar to a banking trojan, we assess that the attacker’s targets are to get user qualifications, possibly for sale or for his personal use in additional exploitation,” Cisco Talos researcher Tiago Pereira mentioned.
“The motive for the deployment of an RDP backdoor is unclear. The most most likely are the sale of RDP entry, the use of RDP to perform about on the web services security options based mostly on IP address or other endpoint installed instruments or the use of RDP for further exploitation on systems that surface exciting to the attacker.”
Found this post fascinating? Stick to THN on Facebook, Twitter and LinkedIn to study a lot more distinctive articles we article.
Some elements of this write-up are sourced from:
thehackernews.com

 Misconfigured Database Leaks Info on 150K E-commerce Buyers
Misconfigured Database Leaks Info on 150K E-commerce Buyers