The risk actor driving the source chain compromise of SolarWinds has ongoing to broaden its malware arsenal with new applications and tactics that have been deployed in attacks as early as 2019, after indicative of the elusive character of the strategies and the adversary’s means to manage persistent access for a long time.
In accordance to cybersecurity company CrowdStrike, which thorough the novel ways adopted by the Nobelium hacking team past 7 days, two innovative malware people ended up positioned on victim techniques — a Linux variant of GoldMax and a new implant dubbed TrailBlazer — extensive in advance of the scale of the attacks arrived to light-weight.
Nobelium, the Microsoft-assigned moniker for the SolarWinds intrusion in December 2020, is also tracked by the broader cybersecurity community underneath the names UNC2452 (FireEye), SolarStorm (Unit 42), StellarParticle (Crowdstrike), Dark Halo (Volexity), and Iron Ritual (Secureworks).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The malicious activities have considering that been attributed to a Russian point out-sponsored actor known as APT29 (also recognised as The Dukes and Cozy Bear), a cyber espionage operation connected with the country’s International Intelligence Company since at minimum 2008.
GoldMax (aka SUNSHUTTLE), which was found by Microsoft and FireEye in March 2021, is a Golang-based malware that functions as a command-and-command backdoor, establishing a protected connection with a remote server to execute arbitrary instructions on the compromised device.
In September 2021, Kaspersky revealed specifics of a next variant of the GoldMax backdoor called Tomiris that was deployed in opposition to several federal government businesses in an unnamed CIS member condition in December 2020 and January 2021.
The most current iteration is a previously undocumented but functionally equivalent Linux implementation of the second-phase malware that was put in in target environments in mid-2019, predating all other determined samples built for the Windows platform to day.
Also shipped all around the very same timeframe was TrailBlazer, a modular backdoor that offers attackers a route to cyber espionage, whilst sharing commonalities with GoldMax in the way it masquerades its command-and-manage (C2) targeted traffic as reputable Google Notifications HTTP requests.
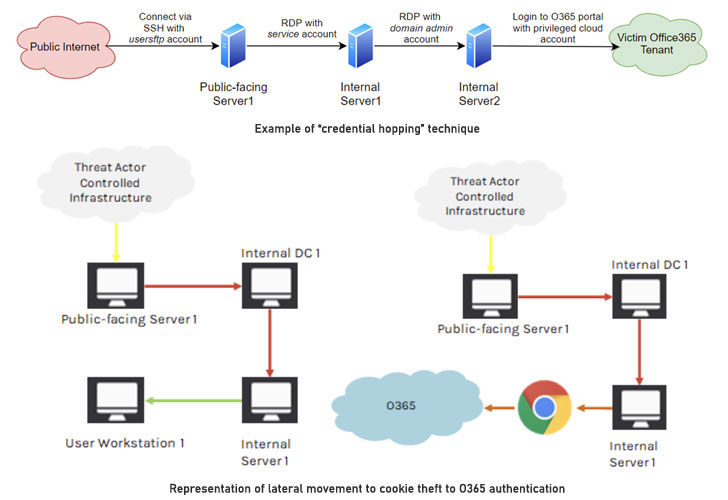
Other unheard of channels employed by the actor to facilitate the attacks contain —
- Credential hopping for obscuring lateral movement
- Place of work 365 (O365) Provider Principal and Software hijacking, impersonation, and manipulation, and
- Theft of browser cookies for bypassing multi-factor authentication
Additionally, the operators carried out numerous circumstances of domain credential theft months aside, each and every time leveraging a different system, one between them staying the use of Mimikatz password stealer in-memory, from an previously compromised host to assure entry for prolonged durations of time.
“The StellarParticle marketing campaign, affiliated with the Cozy Bear adversary group, demonstrates this danger actor’s comprehensive information of Windows and Linux working devices, Microsoft Azure, O365, and Lively Listing, and their patience and covert talent set to stay undetected for months — and in some scenarios, years,” the scientists explained.
Uncovered this post interesting? Observe THN on Facebook, Twitter and LinkedIn to read through a lot more exclusive articles we submit.
Some components of this report are sourced from:
thehackernews.com



 Cynet’s Keys to Extend Threat Visibility
Cynet’s Keys to Extend Threat Visibility