Cybersecurity scientists on Thursday disclosed facts about a new Mirai-motivated botnet called “mirai_ptea” that leverages an undisclosed vulnerability in electronic video clip recorders (DVR) delivered by KGUARD to propagate and have out dispersed denial-of-company (DDoS) attacks.
Chinese security agency Netlab 360 pinned the initially probe in opposition to the flaw on March 23, 2021, ahead of it detected lively exploitation tries by the botnet on June 22, 2021.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The Mirai botnet, given that emerging on the scene in 2016, has been linked to a string of significant-scale DDoS attacks, together with one in opposition to DNS assistance service provider Dyn in October 2016, resulting in important internet platforms and services to remain inaccessible to end users in Europe and North America.
Due to the fact then, many variants of Mirai have sprung up on the scene, in component because of to the availability of its resource code on the Internet. Mirai_ptea is no exception.
Not substantially has been disclosed about the security flaw in an try to reduce more exploitation, but the scientists said the KGUARD DVR firmware experienced vulnerable code prior to 2017 that enabled distant execution of program instructions devoid of authentication. At least around 3,000 products exposed online are prone to the vulnerability.

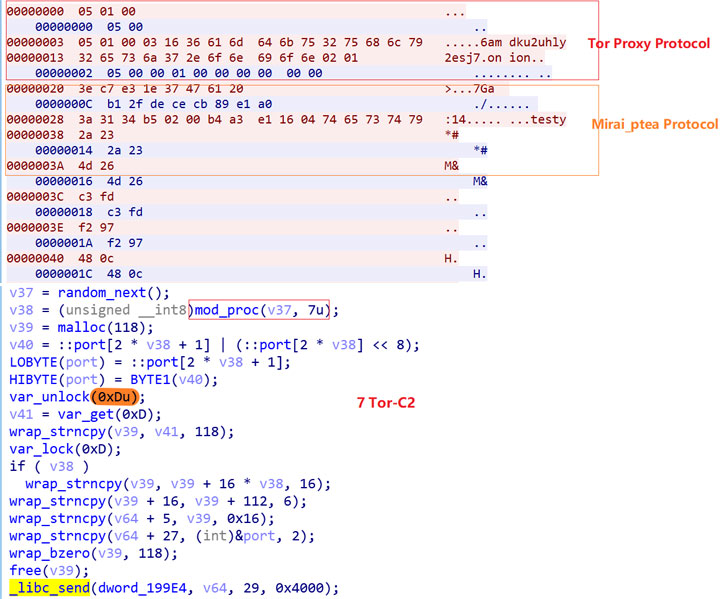
Other than using Tor Proxy to talk with the command-and-command (C2) server, an analysis of the mirai_ptea sample uncovered intensive encryption of all sensitive resource information, which is decoded to build a relationship with the C2 server and retrieve attack commands for execution, such as launching DDoS attacks.
“The geographic distribution of bot supply IPs is […] mostly concentrated in the United States, Korea and Brazil,” the scientists mentioned, with bacterial infections reported across Europe, Asia, Australia, North and South The united states, and areas of Africa.
Located this posting fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to study more distinctive information we publish.
Some parts of this article are sourced from:
thehackernews.com


 Mongolian Certificate Authority Hacked to Distribute Backdoored CA Software
Mongolian Certificate Authority Hacked to Distribute Backdoored CA Software