Scientists have disclosed security vulnerabilities in handover, a elementary system that undergirds modern mobile networks, which could be exploited by adversaries to launch denial-of-company (DoS) and guy-in-the-middle (MitM) attacks employing reduced-price tag equipment.
The “vulnerabilities in the handover technique are not restricted to one handover case only but they effects all distinct handover instances and scenarios that are centered on unverified measurement reports and signal toughness thresholds,” researchers Evangelos Bitsikas and Christina Pöpper from the New York College Abu Dhabi reported in a new paper. “The problem has an effect on all generations due to the fact 2G (GSM), remaining unsolved so significantly.”
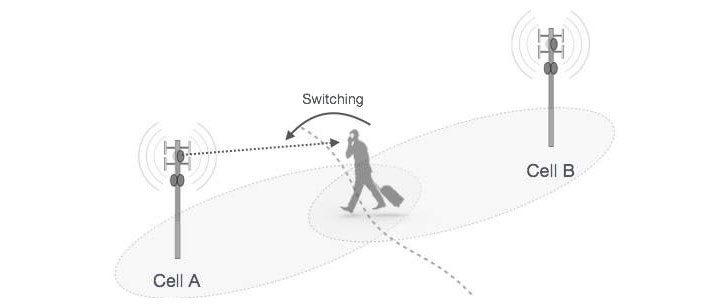
Handover, also recognized as handoff, is a method in telecommunications in which a phone get in touch with or a data session is transferred from a person cell web-site (aka foundation station) to another cell tower with no dropping connectivity for the duration of the transmission. This method is critical to establishing mobile communications, particularly in situations when the user is on the shift.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The regime usually is effective as follows: the person devices (UE) sends sign strength measurements to the network to establish if a handover is necessary and, if so, facilitates the swap when a extra suited goal station is learned.

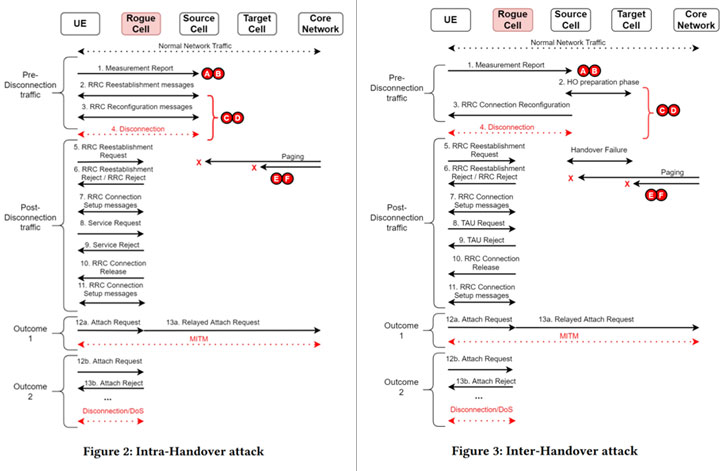
Though these sign readings are cryptographically secured, the content in these reviews is them selves not confirmed, so letting an attacker to pressure the unit to move to a cell website operated by the attacker. The crux of the attack lies in the reality that the resource foundation station is incapable of managing incorrect values in the measurement report, raising the probability of a destructive handover without becoming detected.
The new fake base station attacks, in a nutshell, render susceptible the handover techniques, which are based mostly on the aforementioned encrypted measurement studies and signal power thresholds, correctly enabling the adversary to build a MitM relay and even eavesdrop, drop, modify, and forward messages transmitted amongst the product and the network.
“If an attacker manipulates the articles of the [measurement report] by which includes his/her measurements, then the network will method the bogus measurements,” the researchers said. “This is feasible by imitating a legit base station and replaying its broadcast messages.”
“Attracting” the system to a pretend foundation station
The beginning level of the attack is an original reconnaissance stage whereby the danger actor utilizes a smartphone to obtain data pertaining to close by legit stations and then uses this facts to configure a rogue foundation station that impersonates a authentic cell station.
The attack subsequently requires forcing a victim’s device to connect to the fake station by broadcasting grasp information and facts block (MIB) and process facts block (SIB) messages — information and facts vital to assistance the phone link to the network — with a higher signal power than the emulated base station.
In tricking the UEs to join to the imposter station and forcing the products to report bogus measurements to the network, the intention is to set off a handover function and exploit security flaws in the system to end result in DoS, MitM attacks, and details disclosure impacting the consumer as very well as the operator. This not only compromises users’ privacy but also puts provider availability at risk.
“When the UE is in the protection area of the attacker, the rogue base station has significant enough signal ability to ‘attract’ the UE and cause a [measurement report], then the attacker has extremely fantastic probabilities of forcing the sufferer UE to connect to his/her rogue base station [by] abusing the handover course of action,” the scientists described.
“At the time, the UE is attached to the attacker it could both enter in a camped mode because of to a denial-of-service (DoS) attack and turn into unresponsive, or the attacker could set up a gentleman-in-the-middle (MitM) relay making the foundation for other superior exploits.”
As numerous as six security vulnerabilities have been recognized in the handover method —
- Insecure broadcast messages (MIB, SIB)
- Unverified measurement experiences
- Lacking cross-validation in the planning period
- Random-accessibility channel (RACH) initiation without the need of verification
- Missing restoration mechanism, and
- Issues of distinguishing network failures from attacks
In an experimental setup, the researchers observed all the test gadgets, such as OnePlus 6, Apple iPhone 5, Samsung S10 5G, and Huawei Pro P40 5G, to be inclined to DoS and MitM attacks. The conclusions were introduced at the Yearly Laptop Security Purposes Meeting (ACSAC) held earlier this month.
Identified this write-up fascinating? Observe THN on Facebook, Twitter and LinkedIn to examine more exclusive material we post.
Some components of this post are sourced from:
thehackernews.com



 How to see if cybersecurity of your organization is in check for the New Year
How to see if cybersecurity of your organization is in check for the New Year