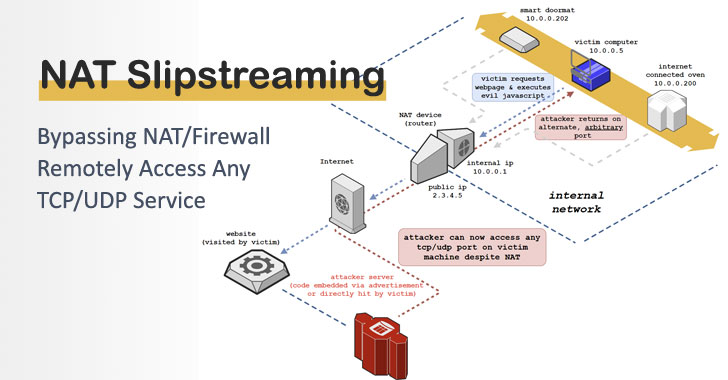
A new investigation has demonstrated a approach that allows an attacker to bypass firewall safety and remotely entry any TCP/UDP provider on a victim device.
Referred to as NAT Slipstreaming, the technique includes sending the focus on a url to a malicious web-site (or a legitimate internet site loaded with destructive ads) that, when frequented, finally triggers the gateway to open up any TCP/UDP port on the victim, therefore circumventing browser-primarily based port limits.
The results had been revealed by privacy and security researcher Samy Kamkar above the weekend.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
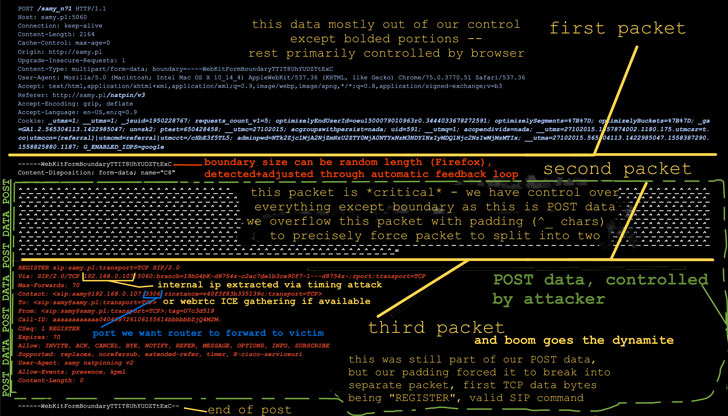
“NAT Slipstreaming exploits the user’s browser in conjunction with the Software Stage Gateway (ALG) relationship tracking mechanism designed into NATs, routers, and firewalls by chaining internal IP extraction by using timing attack or WebRTC, automated distant MTU and IP fragmentation discovery, TCP packet dimensions massaging, Convert authentication misuse, specific packet boundary handle, and protocol confusion by browser abuse,” Kamkar reported in an investigation.
The method was carried out using a NetGear Nighthawk R7000 router jogging Linux kernel variation 2.6.36.4.
Identifying Packet Boundaries
Network tackle translation (NAT) is the method where by a network unit, this sort of as a firewall, remaps an IP address room into a further by modifying network tackle facts in the IP header of packets even though they are in transit.
The primary advantage is that it limitations the variety of public IP addresses utilized in an organization’s internal network and enhances security by letting a single general public IP address to be shared among various techniques.
NAT Slipstreaming functions by using gain of TCP and IP packet segmentation to remotely regulate the packet boundaries and applying it to generate a TCP/UDP packet setting up with a SIP technique these as Sign up or INVITE.
SIP (shorter for Session Initiation Protocol) is a communications protocol made use of for initiating, maintaining, and terminating actual-time multimedia classes for voice, video clip, and messaging purposes.
In other words, a blend of packet segmentation and smuggling SIP requests in HTTP can be employed to trick the NAT ALG into opening arbitrary ports for inbound connections to the consumer.
To attain this, a large HTTP Article request is sent with an ID and a hidden web variety that details to an attack server working a packet sniffer, which is employed to seize the MTU dimensions, facts packet dimension, TCP and IP header measurements, between many others, and subsequently transmitting the dimensions information again to the victim customer around a separate Put up message.
What’s additional, it also abuses an authentication functionality in Convert (Traversal Working with Relays all-around NAT) — a protocol that is utilised in conjunction with NATs to relay media from any peer to a further customer in the network — to have out a packet overflow and lead to IP packets to fragment.
The concept, in a nutshell, is to overflow a TCP or UDP packet by padding (with “^” people) and power it to split into two so that the SIP data packet is at the extremely start out of the second packet boundary.
Hook up to TCP/UDP by means of Packet Alteration
In the following phase, the victim’s inside IP deal with is extracted applying WebRTC ICE on modern browsers these kinds of as Chrome or Firefox or by executing a timing attack on prevalent gateways (192.168.*.1, 10…1, and nearby networks).
“Once the customer gets the packet sizes and internal IP address, it constructs a specifically crafted web type that pads the Submit information up until we believe that the packet will grow to be fragmented, at which place our SIP Sign-up containing internal IP deal with is appended,” Kamkar mentioned. “The kind is submitted by means of Javascript with no consent from the target.”
Just as the packets achieve the attack server and it really is determined that the SIP packet isn’t rewritten with the general public IP handle, an automatic message is despatched back again to the customer, asking it to change its packet measurement to a new boundary primarily based on the info formerly gleaned from the sniffer.
Armed with the proper packet boundary, the NAT is deceived into thinking, “this is a legit SIP registration and from a SIP consumer on the victim’s device,” finally resulting in the NAT to open up up the port in the authentic packet despatched by the victim.
“The router will now ahead any port the attacker chooses again to the inner sufferer, all from basically searching to a website,” Kamkar said.
The total proof-of-thought code for NAT Slipstreaming can be identified below.
Found this report intriguing? Observe THN on Fb, Twitter and LinkedIn to read far more special written content we submit.
Some pieces of this post are sourced from:
thehackernews.com

 Maze ransomware gang retires from cyber crime
Maze ransomware gang retires from cyber crime