Cybercriminals are continuing to prey on people browsing for cracked software by directing them to fraudulent internet websites hosting weaponized installers that deploy malware referred to as NullMixer on compromised programs.
“When a consumer extracts and executes NullMixer, it drops a range of malware documents to the compromised machine,” cybersecurity agency Kaspersky claimed in a Monday report. “It drops a vast range of malicious binaries to infect the machine with, such as backdoors, bankers, downloaders, spyware, and a lot of many others.”
Other than siphoning users’ qualifications, tackle, credit card data, cryptocurrencies, and even Fb and Amazon account session cookies, what will make NullMixer insidious is its capability to down load dozens of trojans at the moment, significantly widening the scale of the infections.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

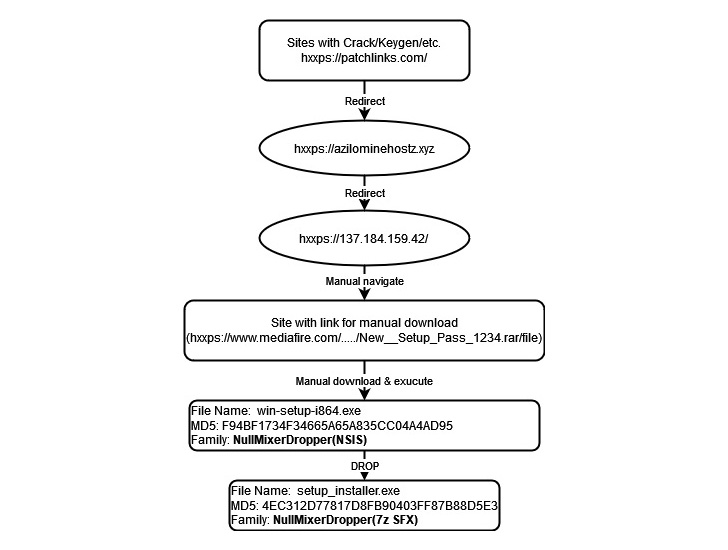
Attack chains typically get started when a consumer tries to down load cracked software program from a single of the websites, which sales opportunities to a password-secured archive that consists of an executable file that, for its section, drops and launches a next setup binary built to produce an array of destructive information.
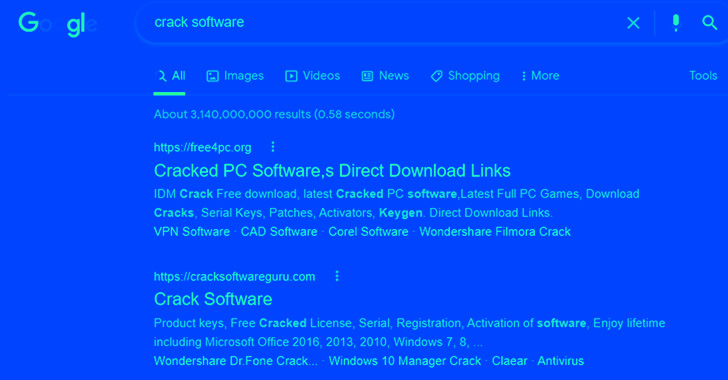
These malicious sites leverage look for engine optimization (Seo) poisoning techniques these kinds of as search term stuffing to attribute them extremely in look for engine success. Related ways have been adopted by actors guiding GootLoader and SolarMarker campaigns.
NullMixer, last thirty day period, was linked to the distribution of a rogue Google Chrome extension referred to as FB Stealer, which is able of Facebook credential theft and lookup engine substitution.
Some of the other outstanding malware people distributed by the dropper contain DanaBot and a raft of data-stealing malware these kinds of as ColdStealer, PseudoManuscrypt, Raccoon Stealer, Redline Stealer, and Vidar.

Also deployed using NullMixer are trojan downloaders like FormatLoader, GCleaner, LegionLoader (aka Satacom), LgoogLoader, PrivateLoader, SgnitLoader, ShortLoader, and SmokeLoader, as properly as the C-Joker cryptocurrency wallet stealer.
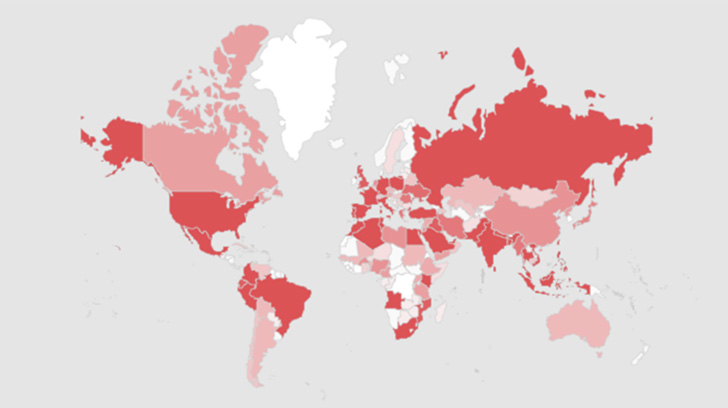
Kaspersky reported it blocked attempts to infect additional than 47,778 victims worldwide, with a bulk of the users located in Brazil, India, Russia, Italy, Germany, France, Egypt, Turkey, and the U.S. The risk actor functioning NullMixer has not been attributed to a known team.
The hottest conclusions are but yet another sign that malware and unwanted apps are remaining increasingly propagated through pirated software program. It is also advised to examine on the web accounts consistently for unfamiliar transactions.
“Any download of data files from untrustworthy methods is a real activity of roulette: you under no circumstances know when it will fireplace, and which threat you will get this time,” Kaspersky researcher Haim Zigel reported. “Obtaining NullMixer, people get several threats at at the time.”
Uncovered this article intriguing? Stick to THN on Facebook, Twitter and LinkedIn to read much more special information we publish.
Some sections of this article are sourced from:
thehackernews.com

 TikTok considers changes to data policies amid rising security concerns
TikTok considers changes to data policies amid rising security concerns