E-commerce platforms in the U.S., Germany, and France have arrive below attack from a new kind of malware that targets Nginx servers in an attempt to masquerade its presence and slip past detection by security options.
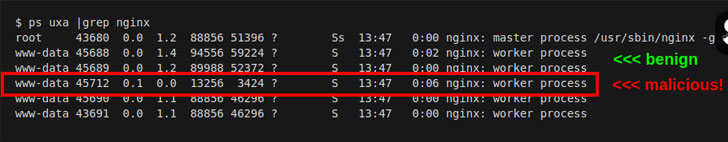
“This novel code injects alone into a host Nginx application and is approximately invisible,” Sansec Menace Investigation workforce mentioned in a new report. “The parasite is applied to steal details from eCommerce servers, also recognized as ‘server-side Magecart.'”
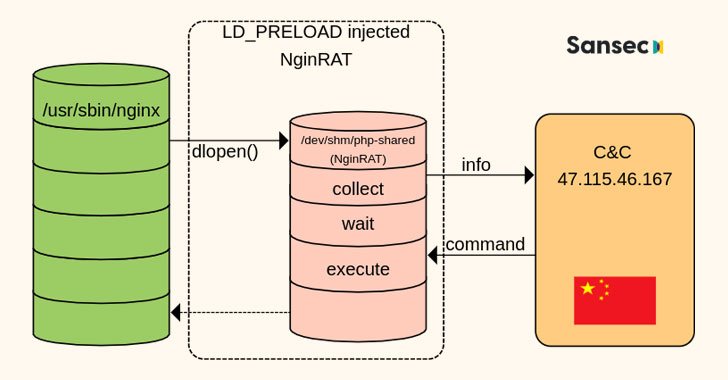
A absolutely free and open up-supply software package, Nginx is a web server that can also be utilised as a reverse proxy, load balancer, mail proxy, and HTTP cache. NginRAT, as the advanced malware is identified as, performs by hijacking a host Nginx application to embed alone into the webserver system.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The remote entry trojan by itself is shipped by means of CronRAT, a different piece of malware the Dutch cybersecurity firm disclosed last 7 days as hiding its destructive payloads in cron work opportunities scheduled to execute on February 31st, a non-existent calendar working day.
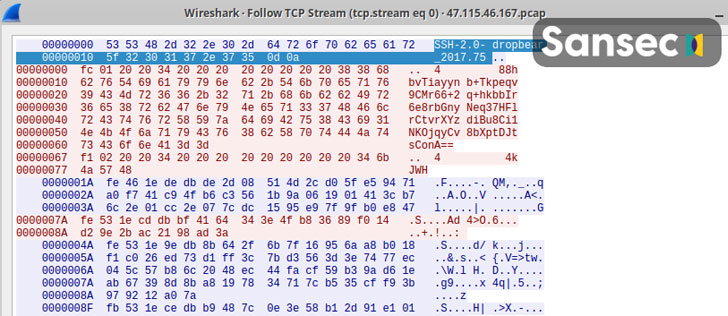
Both CronRAT and NginRAT are built to present a distant way into the compromised servers, and the aim of the intrusions is to make server-aspect modifications to the compromised e-commerce websites in a way that allow the adversaries to exfiltrate information by skimming on line payment forms.
The attacks, collectively known as Magecart or web skimming, are the perform of a cybercrime syndicate comprised of dozens of subgroups that are associated in electronic credit score card theft by exploiting program vulnerabilities to gain accessibility to an online portal’s supply code and insert malicious JavaScript code that siphons the information customers enter into checkout internet pages.

“Skimmer teams are increasing swiftly and focusing on different e-commerce platforms employing a selection of methods to keep on being undetected,” Zscaler scientists mentioned in an investigation of the most current Magecart tendencies revealed previously this year.
“The newest procedures involve compromising susceptible versions of e-commerce platforms, hosting skimmer scripts on CDNs and cloud companies, and applying freshly registered domains (NRDs) lexically near to any legit web company or particular e-commerce shop to host malicious skimmer scripts.”
Identified this article fascinating? Comply with THN on Fb, Twitter and LinkedIn to go through much more unique content material we publish.
Some parts of this write-up are sourced from:
thehackernews.com

 CISA Warns of Actively Exploited Critical Zoho ManageEngine ServiceDesk Vulnerability
CISA Warns of Actively Exploited Critical Zoho ManageEngine ServiceDesk Vulnerability