A recently uncovered security flaw in the Windows functioning procedure can be exploited to coerce remote Windows servers, which include Area Controllers, to authenticate with a destructive destination, thus allowing an adversary to phase an NTLM relay attack and wholly get over a Windows area.
The issue, dubbed “PetitPotam,” was learned by security researcher Gilles Lionel, who shared specialized particulars and evidence-of-principle (PoC) code past 7 days, noting that the flaw works by forcing “Windows hosts to authenticate to other machines by way of MS-EFSRPC EfsRpcOpenFileRaw purpose.”
MS-EFSRPC is Microsoft’s Encrypting File Process Remote Protocol that’s used to complete “servicing and administration operations on encrypted info that is saved remotely and accessed in excess of a network.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Precisely, the attack allows a area controller to authenticate from a remote NTLM under a undesirable actor’s manage working with the MS-EFSRPC interface and share its authentication facts. This is carried out by connecting to LSARPC, resulting in a state of affairs where the goal server connects to an arbitrary server and performs NTLM authentication.
“An attacker can focus on a Domain Controller to deliver its qualifications by employing the MS-EFSRPC protocol and then relaying the DC NTLM credentials to the Energetic Directory Certificate Providers Ad CS Web Enrollment internet pages to enroll a DC certification,” TRUESEC’s Hasain Alshakarti mentioned. “This will successfully give the attacker an authentication certificate that can be utilised to entry domain solutions as a DC and compromise the entire domain.

Even though disabling guidance for MS-EFSRPC will not prevent the attack from operating, Microsoft has considering the fact that issued mitigations for the issue, even though characterizing “PetitPotam” as a “traditional NTLM relay attack,” which permit attackers with access to a network to intercept legit authentication targeted visitors between a customer and a server and relay those validated authentication requests in get to entry network expert services.

“To stop NTLM Relay Attacks on networks with NTLM enabled, area administrators need to guarantee that products and services that permit NTLM authentication make use of protections this sort of as Prolonged Security for Authentication (EPA) or signing capabilities these types of as SMB signing,” Microsoft pointed out. “PetitPotam will take benefit of servers where the Energetic Listing Certificate Services (Advertisement CS) is not configured with protections for NTLM Relay Attacks.”
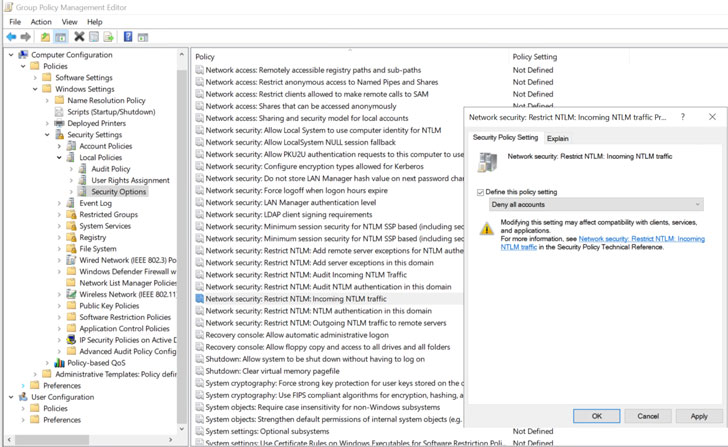
To safeguard versus this line of attack, the Windows maker is recommending that customers disable NTLM authentication on the domain controller. In the event NTLM can’t be turned off for compatibility reasons, the business is urging customers to take 1 of the two ways down below –
- Disable NTLM on any Ad CS Servers in your domain working with the group policy Network security: Prohibit NTLM: Incoming NTLM visitors.
- Disable NTLM for Internet Facts Companies (IIS) on Ad CS Servers in the domain functioning the “Certificate Authority Web Enrollment” or “Certificate Enrollment Web Service” solutions
PetitPotam marks the third main Windows security issue disclosed more than the previous thirty day period immediately after the PrintNightmare and SeriousSAM (aka HiveNightmare) vulnerabilities.
Identified this short article intriguing? Observe THN on Fb, Twitter and LinkedIn to examine far more exceptional content material we article.
Some pieces of this article are sourced from:
thehackernews.com


 5 Steps to Improving Ransomware Resiliency
5 Steps to Improving Ransomware Resiliency