A PHP variation of an details-thieving malware known as Ducktail has been uncovered in the wild remaining distributed in the type of cracked installers for legitimate apps and online games, in accordance to the most recent results from Zscaler.
“Like more mature variations (.NetCore), the most recent version (PHP) also aims to exfiltrate delicate info associated to saved browser credentials, Fb account details, and so on.,” Zscaler ThreatLabz scientists Tarun Dewan and Stuti Chaturvedi mentioned.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Ducktail, which emerged on the danger landscape in late 2021, is attributed to an unnamed Vietnamese menace actor, with the malware generally designed to hijack Facebook company and advertising and marketing accounts.
The monetarily motivated cybercriminal operation was 1st documented by Finnish cybersecurity firm WithSecure (previously F-Secure) in late July 2022.
Though former variations of the malware ended up located to use Telegram as a command-and-handle (C2) channel to exfiltrate details, the PHP variant noticed in August 2022 establishes connections to a recently hosted web-site to retail store the details in JSON structure.
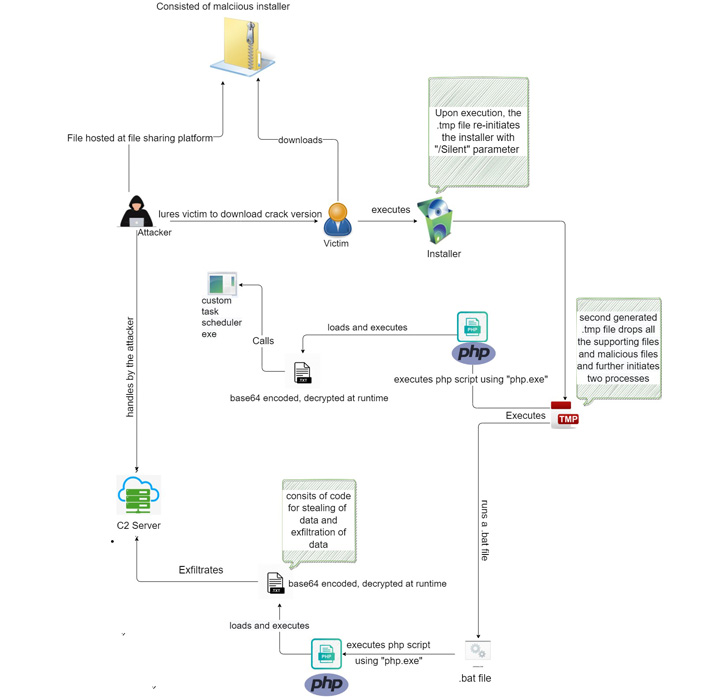
Attack chains observed by Zscaler entail embedding the malware in ZIP archive information hosted on file-sharing companies like mediafire[.]com, masquerading as cracked variations of Microsoft Business, online games, and porn-associated documents.

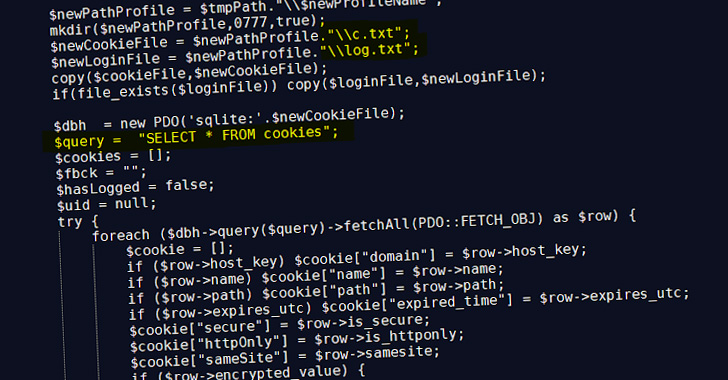
Execution of the installer, in change, activates a PHP script that finally launches the code liable for thieving and exfiltrating data from web browsers, cryptocurrency wallets, and Fb Organization accounts.
“It appears to be that the risk actors driving the Ducktail stealer marketing campaign are constantly making changes or enhancement in the shipping and delivery mechanisms and approach to steal a extensive wide variety of delicate consumer and technique facts targeting consumers at massive,” the researchers said.
Discovered this post fascinating? Follow THN on Facebook, Twitter and LinkedIn to study additional distinctive articles we put up.
Some pieces of this short article are sourced from:
thehackernews.com

 Malwarebytes unveils new MDR service to help bridge cyber skills gap
Malwarebytes unveils new MDR service to help bridge cyber skills gap