Scientists on Tuesday disclosed a novel malware that works by using a wide range of tricks to keep beneath the radar and evade detection, even though stealthily capable of executing arbitrary instructions on infected units.
Identified as ‘Pingback,’ the Windows malware leverages Internet Management Concept Protocol (ICMP) tunneling for covert bot communications, allowing for the adversary to benefit from ICMP packets to piggyback attack code, according to an investigation published these days by Trustwave.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
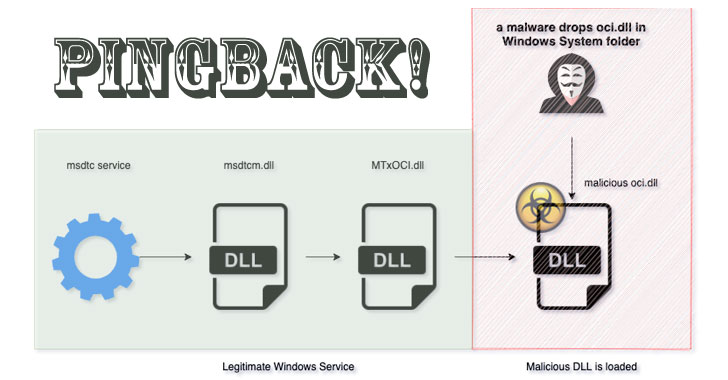
Pingback (“oci.dll”) achieves this by getting loaded by means of a respectable service referred to as MSDTC (Microsoft Dispersed Transaction Coordinator) — a ingredient accountable for managing databases functions that are dispersed in excess of numerous devices — by taking benefit of a technique named DLL research buy hijacking, which will involve making use of a legitimate application to preload a malicious DLL file.
Naming the malware as one particular of the plugins demanded for supporting Oracle ODBC interface in MSDTC is crucial to the attack, the researchers noted. Though MSDTC is not configured to run immediately on startup, a VirusTotal sample submitted in July 2020 was located to install the DLL file into the Windows Program directory and begin the MSDTC services to accomplish persistence, raising the probability that a different executable is very important to setting up the malware.
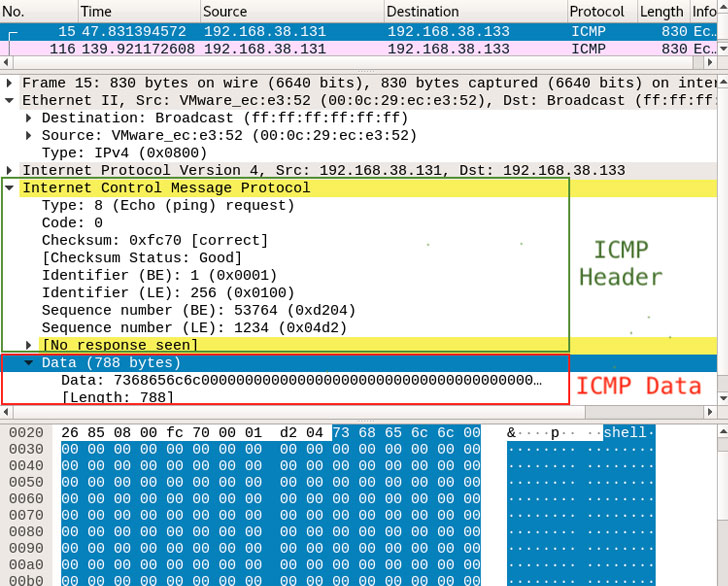
Upon thriving execution, Pingback resorts to making use of the ICMP protocol for its key conversation. ICMP is a network layer protocol largely employed for sending mistake messages and operational information and facts, say, a failure inform when a different host gets to be unreachable.
Exclusively, Pingback usually takes advantage of an Echo request (ICMP concept kind 8), with the concept sequence numbers 1234, 1235, and 1236 denoting the style of information contained in the packet — 1234 getting a command or facts, and 1235 and 1236 being the acknowledgment for receipt of information on the other conclude. Some of the instructions supported by the malware include the functionality to operate arbitrary shell commands, obtain and upload files from and to the attacker’s host, and execute malicious commands on the contaminated device.
An investigation into the malware’s original intrusion route is ongoing.
“ICMP tunneling is not new, but this specific sample piqued our desire as a serious-earth instance of malware utilizing this procedure to evade detection,” the researchers explained. “ICMP is practical for diagnostics and general performance of IP connections, [but] it can also be misused by destructive actors to scan and map a target’s network surroundings. When we are not suggesting that ICMP should really be disabled, we do propose putting in area monitoring to assistance detect these types of covert communications more than ICMP.”
Located this write-up exciting? Abide by THN on Facebook, Twitter and LinkedIn to go through a lot more exceptional content material we article.
Some sections of this posting are sourced from:
thehackernews.com

 Tens of thousands of Pennsylvanians health data exposed following data breach
Tens of thousands of Pennsylvanians health data exposed following data breach