Ransomware groups carry on to evolve their methods and approaches to deploy file-encrypting malware on compromised systems, notwithstanding legislation enforcement’s disruptive actions towards the cybercrime gangs to reduce them from victimizing additional companies.
“Be it owing to regulation enforcement, infighting amongst teams or men and women abandoning variants entirely, the RaaS [ransomware-as-a-service] teams dominating the ecosystem at this point in time are totally different than just a few months back,” Intel 471 scientists explained in a report released this thirty day period. “Nevertheless, even with the shift in the variants, ransomware incidents as a complete are nevertheless on the increase.”
Sweeping legislation enforcement functions carried out by government businesses in current months have brought about speedy shifts in the RaaS landscape and turned the tables on ransomware syndicates like Avaddon, BlackMatter, Cl0p, DarkSide, Egregor, and REvil, forcing the actors to sluggish down or shut down their businesses entirely.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

But just as these variants are fading into obscurity, other up-and-coming teams have stepped in to fill the vacuum. Intel 471’s results have uncovered a full of 612 ransomware attacks concerning July to September 2021 that can be attributed to 35 different ransomware variants.
Around 60% of the noticed infections were tied to 4 variants alone — topped by LockBit 2. (33%), Conti (15.2%), BlackMatter (6.9%), and Hive (6%) — and largely impacted producing, purchaser and industrial merchandise, qualified providers and consulting, and real estate sectors.
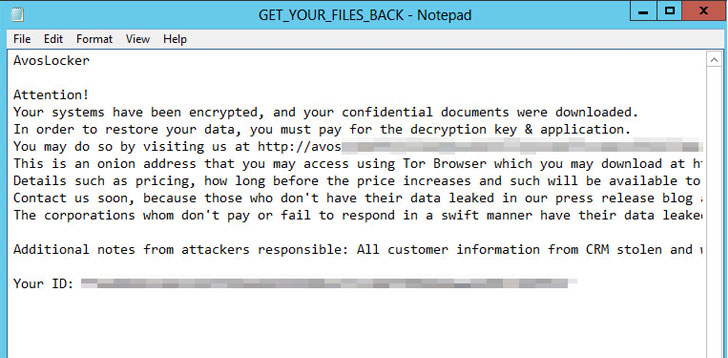
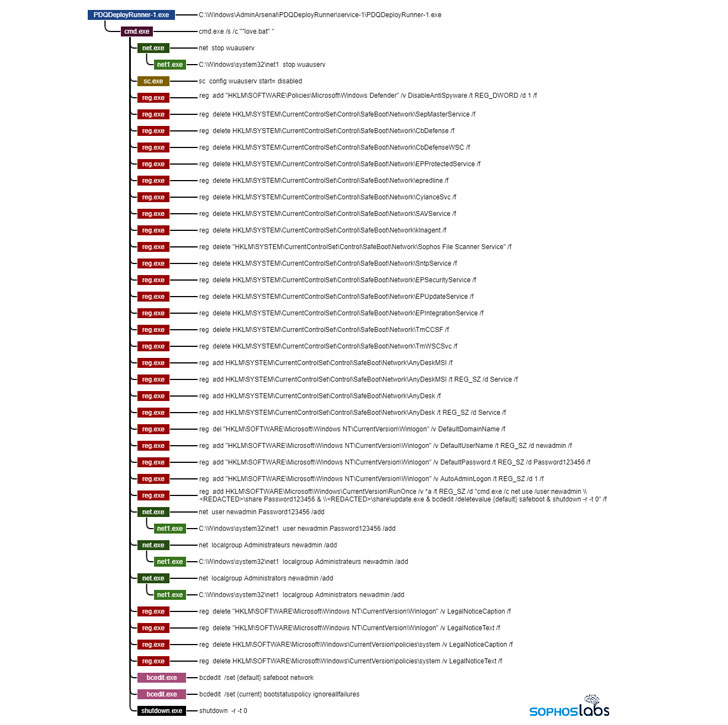
Avos Locker is just one amongst the a lot of such cartels that have not only witnessed a surge in attacks, but have also adopted new tactics to pursue their economically motivated techniques, chief among the them currently being the capability to disable endpoint security items on the focused programs and boot into Windows Safe and sound Manner to execute the ransomware. Also mounted is the AnyDesk remote administration software to manage accessibility to the machine although operating in Harmless Mode.
“The reason for this is that several, if not most, endpoint security solutions do not operate in Protected Mode — a unique diagnostic configuration in which Windows disables most 3rd-party motorists and software program, and can render otherwise shielded machines unsafe,” SophosLabs principal security researcher, Andrew Brandt, mentioned. “The strategies deployed by Avos Locker are basic but clever, with attackers ensuring that the ransomware has the very best possibility of functioning in Protected Mode and allowing the attackers to retain remote entry to the machines during the attack.”
Hive’s RaaS software, for its section, has been dubbed “aggressive” for its use of tension tactics to make victim businesses pay back ransoms, with Group-IB linking the strain to attacks on 355 providers as of Oct 16 since it emerged on the landscape in late June 2021. Meanwhile, Russian-language ransomware group Everest is getting its extortion ways to the subsequent level by threatening to provide off accessibility to qualified devices if their needs usually are not achieved, NCC Team stated.
“When promoting ransomware-as-a-company has found a surge in level of popularity in excess of the previous calendar year, this is a uncommon occasion of a group forgoing a request for a ransom and giving access to IT infrastructure — but we may perhaps see copycat attacks in 2022 and over and above,” the U.K.-based cybersecurity company pointed out.
What is extra, a rather new ransomware family dubbed Pysa (aka Mespinoza) has unseated Conti as a person of the top rated ransomware danger teams for the thirty day period of November together with LockBit 2.. The ransomware witnessed a 50% maximize in the quantity of focused businesses and a 400% spike in attacks in opposition to authorities-sector units when in comparison to the month of Oct.
“While law enforcement close to the globe has gotten a lot more intense in their efforts to arrest these behind attacks, builders are even now quickly shutting down well-liked variants, laying low, and coming back with finely-tuned malware made use of by on their own as properly as affiliates,” Intel 471 scientists stated. “As extensive as the builders can keep on being in international locations wherever they are granted harmless harbor, the attacks will carry on, albeit with different variants.”
Located this report intriguing? Stick to THN on Facebook, Twitter and LinkedIn to examine extra distinctive articles we post.
Some areas of this short article are sourced from:
thehackernews.com



 Hellmann Warns Customers They Could Face Malicious Communications Following Attack
Hellmann Warns Customers They Could Face Malicious Communications Following Attack