Most cybersecurity industry experts totally predicted that cybercriminals would leverage the dread and confusion surrounding the Covid-19 pandemic in their cyberattacks.
Of training course, malicious e-mail would have topics relating to Covid-19, and destructive downloads would be Covid-19 associated. This is how cybercriminals work. Any option to optimize usefulness, no make a difference how contemptible, is taken.
Though a lot of have anecdotally instructed techniques in which Covid-19 connected cyberattacks would unfold, we have small facts supporting the real impact of Covid-19 on cybersecurity. Numerous have documented that the amount of malicious email messages with the topic associated to Covid-19 has grown various hundred percent and that the bulk of Covid-19 similar e-mail are now destructive.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Past the predicted raise in Covid-19 relevant malicious e-mails, movies, and an array of downloadable files, which we all anticipated, what else is likely on guiding the scenes?
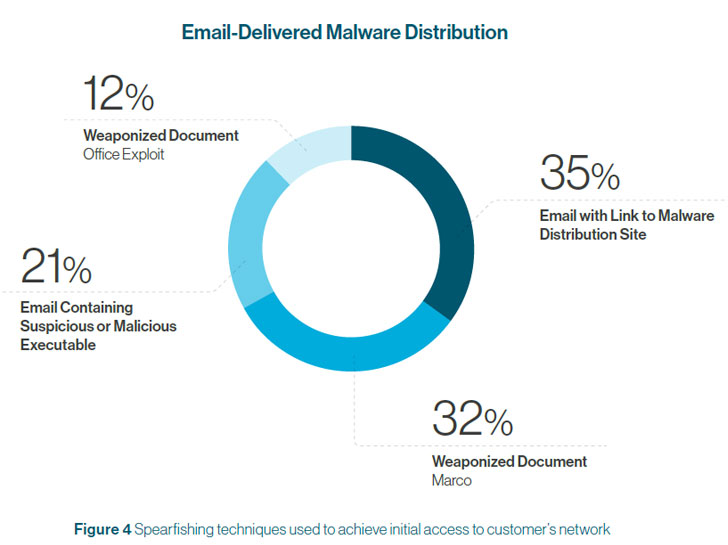
Apparently, cybersecurity corporation Cynet has just introduced a report (down load in this article) detailing changes in cyberattacks they have noticed throughout North The united states and Europe considering that the starting of the Covid-19 pandemic. The report shares a number of intriguing information points and conclusions, these kinds of as the cyberattack volume improve observed in several business sectors, the greater use of spear-phishing as an preliminary attack vector, and the approaches becoming applied to distribute malware in spear-phishing assaults.
The two much more appealing findings observe.
Battling Hearth with Fire
Cynet found that cybercriminals are not just “sort of” leveraging the Covid-19 pandemic, they’re heading all in. Cybercriminals are pulling out their full arsenal of new attack techniques to assure attack results best. This is like a sporting activities staff making use of all the new plays they’ve designed in a person activity rather than spreading them out throughout the time.
The report states that the share of attacks using new methods has traditionally been all around 20%. That is, 80% of assaults have made use of well-identified approaches that are simply recognized, assuming providers have up-to-date preventative actions in place.
Since the Covid-19 pandemic, Cynet found that new attacks jumped to about 35% of all assaults. New attack methods are unable to be sufficiently detected by antivirus software by itself and can only be efficiently discovered working with newer behavioral detection mechanisms. That is, the new detection approaches ought to be applied to detect the new attack methods getting deployed.
Overburdened Security Staffs
Another attention-grabbing observation in the Cynet report is a enormous spike in shoppers requesting skilled aid from their detection and response crew (which Cynet phone calls CyOps). Consumer engagements amplified a whopping 250% all through the pandemic.
Outside of employing superior detection and response mechanisms, deep cybersecurity competencies are essential to detect and mitigate the sharp increase in the new attack procedures deployed all through the Covid-19 pandemic.
The Remedy?
However, numerous organizations do not but have advanced detection and reaction technologies, this sort of as Extended Detection and Reaction (XDR), or ongoing obtain to a 24×7 managed detection and reaction (MDR) staff. When cyberattacks making use of new strategies spike as they are in the course of this pandemic (or could do at any time), organizations devoid of these advanced protections are at increased risk.
We strongly endorse investigating each XDR and MDR options as a way to futureproof and immunize your cybersecurity stack.
And regardless of the security stack you have deployed, be wary of new malware attacks. Use menace hunting tactics to scour your techniques to assure new malware has not slipped by the cracks. The uptick in new malware signifies avoidance and detection develop into trickier, and ongoing menace hunting have to turn out to be the norm.
Download the report in this article.
Uncovered this short article interesting? Adhere to THN on Fb, Twitter and LinkedIn to read extra exclusive material we post.
Some parts of this article is sourced from:
thehackernews.com


 Cybersecurity leaders urge SCOTUS to narrow CFAA scope
Cybersecurity leaders urge SCOTUS to narrow CFAA scope