Users looking for TeamViewer distant desktop software program on search engines like Google are being redirected to malicious links that drop ZLoader malware onto their units though concurrently embracing a stealthier an infection chain that permits it to linger on contaminated products and evade detection by security answers.
“The malware is downloaded from a Google advertisement posted by Google Adwords,” researchers from SentinelOne said in a report released on Monday. “In this campaign, the attackers use an indirect way to compromise victims rather of utilizing the traditional strategy of compromising the victims immediately, these types of as by phishing.”
First identified in 2016, ZLoader (aka Silent Evening and ZBot) is a thoroughly-featured banking trojan and a fork of a different banking malware termed ZeuS, with more recent versions utilizing a VNC module that grants adversaries remote entry to sufferer methods. The malware is in lively improvement, with legal actors spawning an array of variants in recent many years, no considerably less fuelled by the leak of ZeuS source code in 2011.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The newest wave of attacks is considered to concentrate on end users of Australian and German fiscal institutions with the primary target of intercepting users’ web requests to the banking portals and stealing financial institution qualifications. But the marketing campaign is also noteworthy due to the fact of the methods it normally takes to keep below the radar, which includes running a series of instructions to cover the malicious activity by disabling Windows Defender.
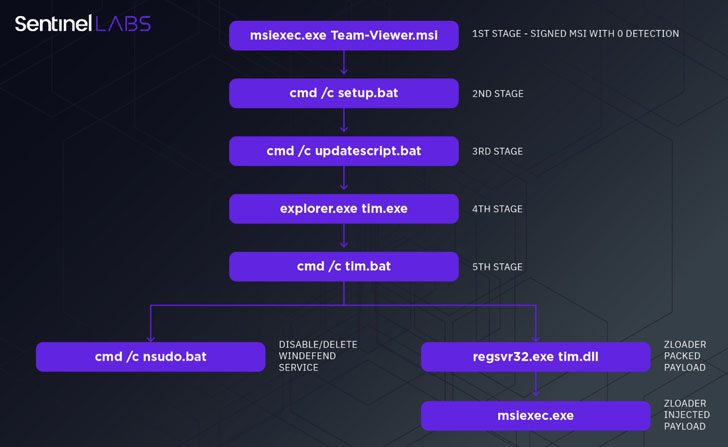
The an infection chain commences when a person clicks on an ad proven by Google on the lookup results page and is redirected to the phony TeamViewer site below the attacker’s regulate, thus tricking the target into downloading a rogue but signed variant of the program (“Crew-Viewer.msi”). The bogus installer functions as the initial stage dropper to trigger a series of steps that contain downloading up coming-phase droppers aimed at impairing the defenses of the device and eventually downloading the ZLoader DLL payload (“tim.dll”).
“At first, it disables all the Windows Defender modules by the PowerShell cmdlet Set-MpPreference,” SentinelOne Senior Danger Intelligence Researcher Antonio Pirozzi mentioned. “It then provides exclusions, these as regsvr32, *.exe, *.dll, with the cmdlet Include-MpPreference to disguise all the elements of the malware from Windows Defender.”
The cybersecurity agency said it found more artifacts that mimic well-known apps like Discord and Zoom, suggesting that the attackers had many strategies ongoing further than leveraging TeamViewer.
“The attack chain analyzed in this investigation exhibits how the complexity of the attack has developed in get to access a better degree of stealthiness, using an substitute to the traditional strategy of compromising victims by means of phishing e-mail,” Pirozzi spelled out. “The method utilised to install the initial phase dropper has been adjusted from socially engineering the sufferer into opening a destructive document to poisoning the user’s web queries with links that produce a stealthy, signed MSI payload.”
Identified this report interesting? Observe THN on Facebook, Twitter and LinkedIn to study much more exceptional content we submit.
Some elements of this write-up are sourced from:
thehackernews.com

 Financial Services Firms Spend Over $2m on Ransomware Recovery
Financial Services Firms Spend Over $2m on Ransomware Recovery