A new piece of stealthy Linux malware identified as Shikitega has been uncovered adopting a multi-phase an infection chain to compromise endpoints and IoT equipment and deposit additional payloads.
“An attacker can get comprehensive handle of the system, in addition to the cryptocurrency miner that will be executed and set to persist,” AT&T Alien Labs stated in a new report revealed Tuesday.
The findings add to a escalating record of Linux malware that has been located in the wild in new months, which include BPFDoor, Symbiote, Syslogk, OrBit, and Lightning Framework.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

After deployed on a qualified host, the attack chain downloads and executes the Metasploit’s “Mettle” meterpreter to maximize regulate, exploits vulnerabilities to elevate its privileges, provides persistence on the host via crontab, and ultimately launches a cryptocurrency miner on contaminated equipment.
The correct approach by which the first compromise is achieved continues to be unknown as still, but what tends to make Shikitega evasive is its means to download upcoming-phase payloads from a command-and-manage (C2) server and execute them specifically in memory.
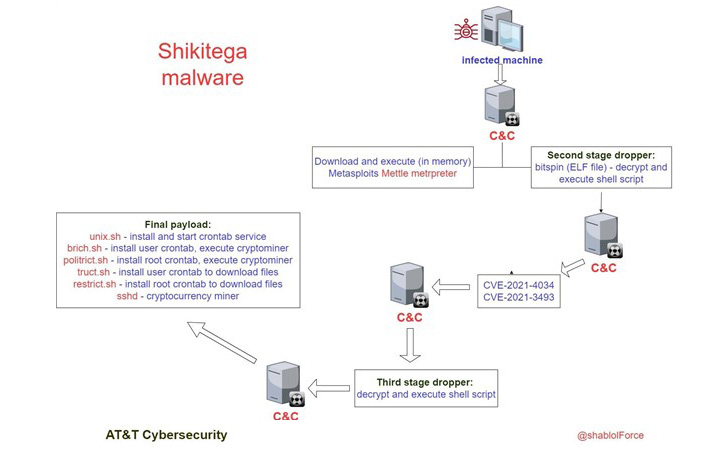
Privilege escalation is attained by implies of exploiting CVE-2021-4034 (aka PwnKit) and CVE-2021-3493, enabling the adversary to abuse the elevated permissions to fetch and execute the last phase shell scripts with root privileges to set up persistence and deploy the Monero crypto miner.

In a even further attempt to fly less than the radar, the malware operators employ a “Shikata ga nai” polymorphic encoder to make it additional difficult to detect by antivirus engines and abuse genuine cloud services for C2 capabilities.
“Menace actors continue to research for strategies to supply malware in new strategies to continue to be underneath the radar and stay clear of detection,” AT&T Alien Labs researcher Ofer Caspi stated.
“Shiketega malware is delivered in a subtle way, it takes advantage of a polymorphic encoder, and it gradually provides its payload wherever every single stage reveals only section of the complete payload.”
Observed this write-up appealing? Follow THN on Facebook, Twitter and LinkedIn to browse a lot more exclusive material we publish.
Some components of this write-up are sourced from:
thehackernews.com


 North Korean Hackers Deploying New MagicRAT Malware in Targeted Campaigns
North Korean Hackers Deploying New MagicRAT Malware in Targeted Campaigns