Chinese cyber espionage team APT41 has been connected to seemingly disparate malware strategies, in accordance to clean investigation that has mapped with each other added components of the group’s network infrastructure to hit upon a point out-sponsored marketing campaign that will take benefit of COVID-themed phishing lures to concentrate on victims in India.
“The image we uncovered was that of a state-sponsored campaign that performs on people’s hopes for a swift conclusion to the pandemic as a lure to entrap its victims,” the BlackBerry Investigation and Intelligence team reported in a report shared with The Hacker Information. “And when on a user’s machine, the threat blends into the electronic woodwork by working with its individual personalized profile to hide its network targeted visitors.”
APT41 (aka Barium or Winnti) is a moniker assigned to a prolific Chinese cyber threat group that carries out condition-sponsored espionage activity in conjunction with economically motivated functions for personalized gain as considerably back again as 2012. Calling the team “Double Dragon,” citing its twin targets, Mandiant (formerly FireEye) pointed out the collective’s penchant for placing healthcare, higher-tech, and telecommunications sectors for setting up lengthy-expression accessibility and facilitating the theft of mental home.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

In addition, the group is regarded for staging cybercrime intrusions that are aimed at thieving source code and digital certificates, virtual currency manipulation, and deploying ransomware, as effectively as executing program supply chain compromises by injecting malicious code into genuine files prior to distribution of software updates.
The most current analysis by BlackBerry builds on earlier findings by Mandiant in March 2020, which comprehensive a “world-wide intrusion marketing campaign” unleashed by APT41 by exploiting a number of publicly acknowledged vulnerabilities affecting Cisco and Citrix products to drop and execute next-stage payloads that were being subsequently made use of to down load a Cobalt Strike Beacon loader on compromised units. The loader was notable for its use of a malleable command-and-regulate (C2) profile that allowed the Beacon to mix its network communications with a remote server into legit targeted visitors originating from the victim network.
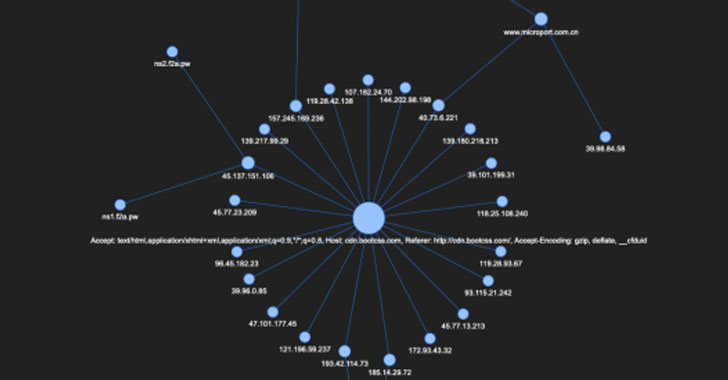
BlackBerry, which located a very similar C2 profile uploaded to GitHub on March 29 by a Chinese security researcher with the pseudonym “1135,” made use of the metadata configuration knowledge to detect a contemporary cluster of domains connected to APT41 that try to masquerade Beacon website traffic appear like genuine traffic from Microsoft sites, with IP tackle and area title overlaps observed in strategies joined to the Higaisa APT group, and that of Winnti disclosed more than the previous yr.

Subsequent investigation into the URLs disclosed as quite a few as 3 malicious PDF information that achieved out to one of the recently found out domains that had also previously hosted a Cobalt Strike Crew Server. What’s additional, the files themselves act as phishing lures saying to be COVID-19 advisories issued by the govt of India or have information and facts about the latest income tax laws targeting non-resident Indians.
The spear-phishing attachments look in the kind of .LNK information or .ZIP archives, which, when opened, end result in the PDF document staying shown to the victim, while, in the background, the an infection chain potential customers to the execution of a Cobalt Strike Beacon. Even though a set of intrusions employing very similar phishing lures and uncovered in September 2020 have been pinned on the Evilnum group, BlackBerry stated the compromise indicators place to an APT41-affiliated marketing campaign.
“With the assets of a nation-point out degree menace group, it truly is doable to generate a truly staggering level of range in their infrastructure,” the researchers reported, including by piecing together the destructive actions of the threat actor through community sharing of details, it can be probable to “uncover the tracks that the cybercriminals involved worked so difficult to hide.”
Located this article exciting? Adhere to THN on Facebook, Twitter and LinkedIn to study extra special written content we publish.
Some pieces of this write-up are sourced from:
thehackernews.com

 Google Pledges $1m to Secure Open Source Project
Google Pledges $1m to Secure Open Source Project