A new tutorial study has highlighted a quantity of privacy and security pitfalls affiliated with recycling mobile phone figures that could be abused to stage a wide variety of exploits, like account takeovers, perform phishing and spam attacks, and even stop victims from signing up for on the net solutions.
Almost 66% of the recycled figures that had been sampled had been discovered to be tied to past owners’ online accounts at common sites, likely enabling account hijacks by merely recovering the accounts tied to these figures.
“An attacker can cycle by means of the out there numbers revealed on on-line variety alter interfaces and verify if any of them are affiliated with on-line accounts of past proprietors,” the scientists reported. If so, the attacker can then acquire these quantities and reset the password on the accounts, and acquire and appropriately enter the OTP sent via SMS upon login.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The findings are component of an evaluation of a sample of 259 phone figures readily available to new subscribers of U.S. telecom majors T-Cell and Verizon Wi-fi. The analyze was undertaken by Princeton University’s Kevin Lee and Prof. Arvind Narayanan, who is 1 of the government committee customers at the Center for Data Technology Policy.
Phone selection recycling refers to the conventional practice of reassigning disconnected phone numbers to other new subscribers of the provider. But this can also pose major risks when an attacker does a reverse lookup by randomly moving into this kind of numbers in the on the web interfaces made available by the two carriers, and upon encountering a recycled amount, get them and effectively log in to the target account to which the amount is joined.
At the coronary heart of the attack, system is the absence of question limits for obtainable figures imposed by the carriers on their prepaid interfaces to adjust quantities, in addition to displaying “whole quantities, which presents an attacker the means to explore recycled figures prior to confirming a selection transform.”
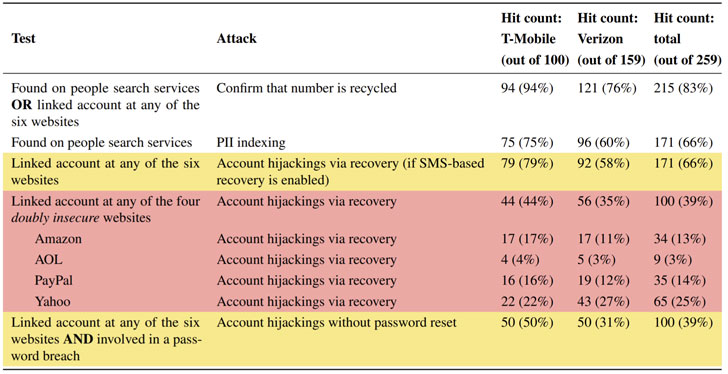
What is far more, 100 of the sampled phone numbers have been identified as linked with email addresses that experienced been concerned in a data breach in the earlier, thus making it possible for account hijacks of a 2nd form that circumvent SMS-based multi-factor authentication. In a 3rd attack, 171 of the 259 accessible figures ended up listed on people search companies like BeenVerified, and in the procedure, leaked sensitive private details of prior homeowners.
“The moment they get the preceding owner’s selection, they can perform impersonation attacks to dedicate fraud or amass even more PII on former owners,” the scientists spelled out.
Outside of the aforementioned 3 reverse lookup attacks, five extra threats enabled by phone amount recycling concentrate on both of those prior and potential proprietors, allowing a malicious actor to impersonate past owners, hijack the victims’ online phone account and other connected on-line accounts, and worse, have out denial-of-assistance attacks.
“Attacker obtains a amount, signs up for an online services that calls for a phone amount, and releases the number,” the researchers said. “When a target obtains the quantity and attempts to indication up for the same assistance, they will be denied thanks to an present account. The attacker can speak to the target through SMS and demand payment to free of charge up the variety on the system.”
In reaction to the findings, T-Mobile said it has updated its “Alter your phone selection” assistance web site with information and facts about reminding consumers to “update your get in touch with quantity on any accounts that could have your quantity saved, these types of as notifications for bank accounts, social media, and so on.” and specify the FCC-mandated amount growing old period of time of 45 times to permit reassignment of previous figures.
Verizon, also, has manufactured equivalent revisions to its “Regulate Verizon cell company” aid site. But neither of the carriers seem to have manufactured any concrete changes that make the attacks more challenging to pull off.
If something, the analyze is an additional evidence of why SMS-primarily based authentication is a risky strategy, as the attacks outlined earlier mentioned could make it possible for an adversary to hijack an SMS 2FA-enabled account with no getting to know the password.
“If you need to have to give up your selection, unlink it from on the internet expert services very first,” Narayanan claimed in a tweet. “Take into consideration very low-price tag variety “parking” companies. Use a lot more safe solutions to SMS-2FA this kind of as authenticator applications.”
Identified this posting intriguing? Stick to THN on Fb, Twitter and LinkedIn to browse extra unique content we post.
Some parts of this article are sourced from:
thehackernews.com

 Best free malware removal tools 2021: Clean your hard drive with these services
Best free malware removal tools 2021: Clean your hard drive with these services