A new cross-platform backdoor identified as “SysJoker” has been observed focusing on devices running Windows, Linux, and macOS functioning programs as portion of an ongoing espionage campaign that is believed to have been initiated throughout the 2nd fifty percent of 2021.
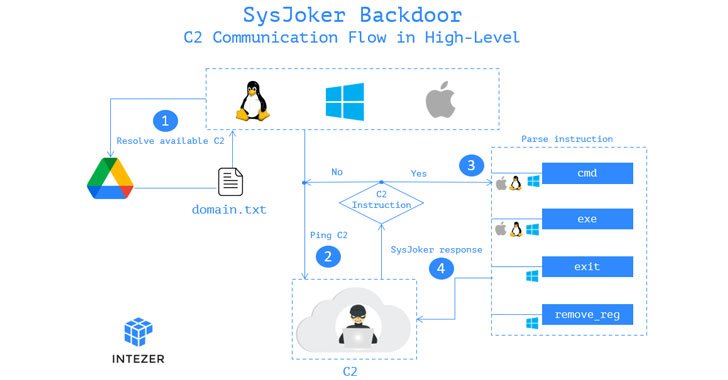
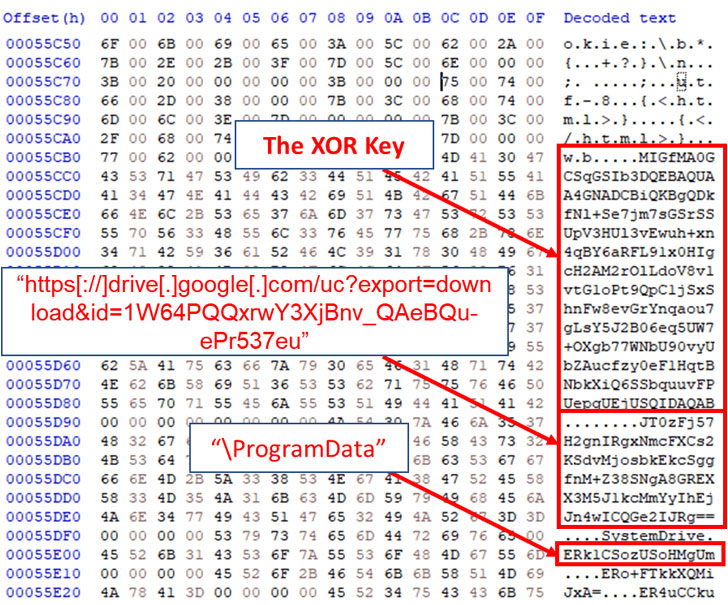
“SysJoker masquerades as a technique update and generates its [command-and-control server] by decoding a string retrieved from a text file hosted on Google Push,” Intezer researchers Avigayil Mechtinger, Ryan Robinson, and Nicole Fishbein mentioned in a technological create-up publicizing their findings. “Dependent on victimology and malware’s habits, we evaluate that SysJoker is right after distinct targets.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The Israeli cybersecurity business, attributing the get the job done to an innovative risk actor, reported it first identified evidence of the implant in December 2021 all through an energetic attack versus a Linux-based mostly web server belonging to an unnamed academic establishment.
A C++-centered malware, SysJoker is shipped by using a dropper file from a remote server that, upon execution, is engineered to collect data about the compromised host, these kinds of as MAC deal with, user title, actual physical media serial quantity, and IP deal with, all of which are encoded and transmitted again to the server.
What is actually far more, connections to the attacker-controlled server are set up by extracting the domain’s URL from a difficult-coded Google Push hyperlink that hosts a textual content file (“area.txt”), enabling the server to relay guidelines to the device that allow for the malware to run arbitrary commands and executables, pursuing which the final results are beamed back again.
“The reality that the code was published from scratch and hasn’t been seen before in other attacks [and] we have not witnessed a second stage or command despatched from the attacker […] indicates that the attack is distinct which ordinarily matches for an advanced actor,” the researchers claimed.
Observed this article appealing? Comply with THN on Fb, Twitter and LinkedIn to read through much more unique articles we put up.
Some sections of this write-up are sourced from:
thehackernews.com


 Microsoft takes aim at critical RCE flaws with “massive” Patch Tuesday update
Microsoft takes aim at critical RCE flaws with “massive” Patch Tuesday update