A novel timing attack uncovered versus the npm’s registry API can be exploited to most likely disclose personal deals applied by corporations, putting builders at risk of source chain threats.
“By making a record of feasible bundle names, menace actors can detect organizations’ scoped personal offers and then masquerade general public offers, tricking workers and people into downloading them,” Aqua Security researcher Yakir Kadkoda stated.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The Scoped Confusion attack financial institutions on examining the time it can take for the npm API (registry.npmjs[.]org) to return an HTTP 404 mistake information when querying for a personal bundle, and measuring it towards the response time for a non-existing module.
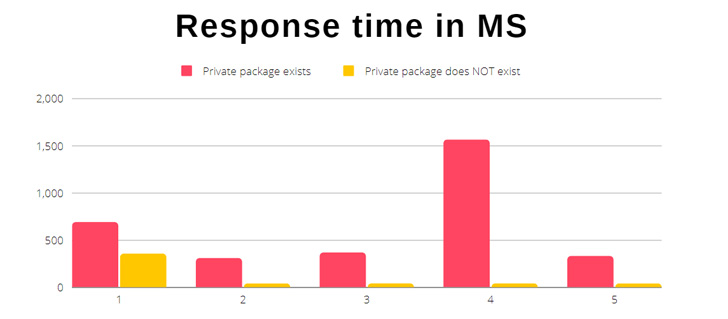
“It can take on normal less time to get a reply for a non-public package deal that does not exist compared to a personal offer that does,” Kadkoda discussed.
The strategy, ultimately, is to identify deals internally applied by organizations, which could then be utilised by threat actors to produce community variations of the exact same packages in an attempt to poison the software program source chain.
The most recent findings are also unique from dependency confusion attacks in that it requires the adversary to 1st guess the private deals used by an organization and then publish phony deals with the very same identify under the community scope.
Dependency confusion (aka namespace confusion), in distinction, financial institutions on the reality that offer administrators check out general public code registries for a package ahead of personal registries, ensuing in the retrieval of a increased version offer from the community repository.

Aqua Security claimed it disclosed the bug to GitHub on March 8, 2022, prompting the Microsoft-owned subsidiary to issue a response that the timing attack will not be preset thanks to architectural limitations.
As preventive measures, it’s advisable that corporations routinely scan npm and other offer administration platforms for lookalike or spoofed packages that masquerade as the interior counterparts.
“If you never obtain public deals very similar to your inner offers, contemplate developing general public offers as placeholders to prevent this sort of attacks,” Kadkoda reported.
Uncovered this posting appealing? Stick to THN on Fb, Twitter and LinkedIn to go through extra special information we write-up.
Some pieces of this post are sourced from:
thehackernews.com


 Does the OWASP Top 10 Still Matter?
Does the OWASP Top 10 Still Matter?