Microsoft’s Windows 10 and the upcoming Windows 11 variations have been located vulnerable to a new regional privilege escalation vulnerability that permits end users with low-amount permissions accessibility Windows system data files, in transform, enabling them to unmask the running program installation password and even decrypt non-public keys.
“Starting off with Windows 10 develop 1809, non-administrative end users are granted entry to SAM, System, and SECURITY registry hive documents,” CERT Coordination Heart (CERT/CC) claimed in a vulnerability take note released Monday. “This can let for local privilege escalation (LPE).”
The data files in issue are as follows –

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
- c:WindowsSystem32configsam
- c:WindowsSystem32configsystem
- c:WindowsSystem32configsecurity
Microsoft, which is tracking the vulnerability less than the identifier CVE-2021-36934, acknowledged the issue, but has nonetheless to roll out a patch, or supply a timeline for when the correct will be manufactured available.

“An elevation of privilege vulnerability exists mainly because of extremely permissive Accessibility Management Lists (ACLs) on multiple procedure files, which includes the Security Accounts Manager (SAM) database,” the Windows makers noted. “An attacker who effectively exploited this vulnerability could run arbitrary code with Method privileges. An attacker could then put in packages see, alter, or delete facts or produce new accounts with whole consumer rights.
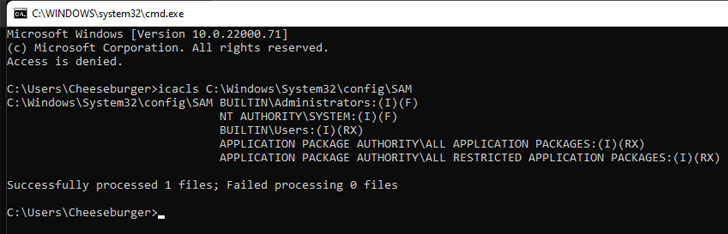
Productive exploitation of the flaw, having said that, necessitates that the attacker already has a foothold and is in possession of the means to execute code on the sufferer process. In the interim, the CERT/CC is recommending that users restrict accessibility to sam, technique, and security files and delete VSS shadow copies of the process push.
The most current disclosure also marks the third publicly disclosed unpatched bug in Windows since the launch of Patch Tuesday updates on July 13. Besides CVE-2021-36934, two more weaknesses affecting the Print Spooler part have also been found, prompting Microsoft to urge all people to cease and disable the services to secure systems towards exploitation.
Linux Distros Undergo from “Sequoia” Privilege Escalation Flaw
It really is not just Windows. Remediations have been produced for a security shortcoming affecting all Linux kernel versions from 2014 that can be exploited by malicious people and malware previously deployed on a method to gain root-level privileges.

Dubbed “Sequoia” by scientists from cybersecurity firm Qualys, the issue has been assigned the identifier CVE-2021-33909 and has an effect on default installations of Ubuntu 20.04, Ubuntu 20.10, Ubuntu 21.04, Debian 11, and Fedora 34 Workstation. Purple Hat Company Linux variations 6, 7, and 8 are also influenced by the vulnerability.
Especially, the flaw considerations a size_t-to-int kind conversion vulnerability in the Linux Kernel’s “seq_file” file procedure interface, permitting an unprivileged area attacker to build, mount, and delete a deep directory construction whose overall route size exceeds 1GB, ensuing in privilege escalation on the susceptible host.
Separately, Qualys also disclosed a stack exhaustion denial-of-services vulnerability in systemd (CVE-2021-33910) that could be exploited by unprivileged attackers to crash the computer software suite and result in a kernel stress.
Located this article attention-grabbing? Comply with THN on Fb, Twitter and LinkedIn to read through more distinctive written content we article.
Some areas of this write-up are sourced from:
thehackernews.com

 Researchers: NSO Group’s Pegasus Spyware Should Spark Bans, Apple Accountability
Researchers: NSO Group’s Pegasus Spyware Should Spark Bans, Apple Accountability