An unidentified menace actor has been concentrating on Russian entities with a newly uncovered distant entry trojan identified as Woody RAT for at least a year as portion of a spear-phishing campaign.
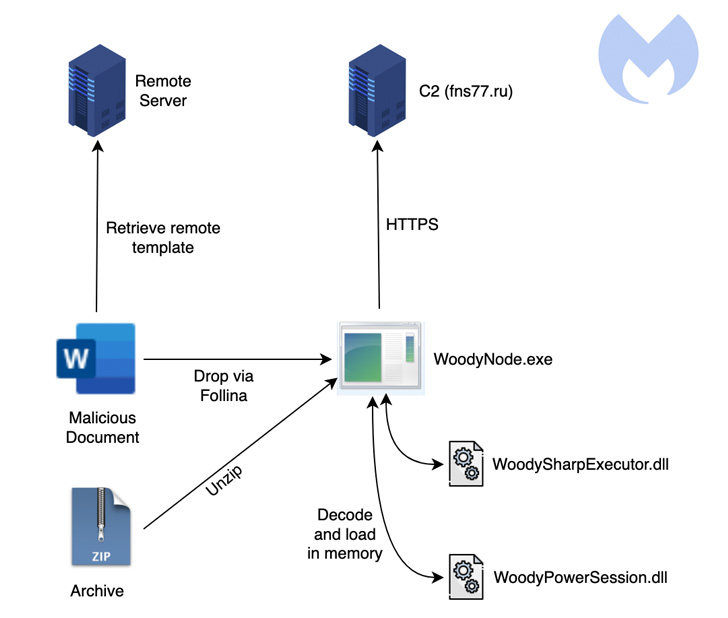
The highly developed custom backdoor is reported to be delivered by way of both of two techniques: archive documents and Microsoft Office documents leveraging the now-patched “Follina” aid diagnostic instrument vulnerability (CVE-2022-30190) in Windows.
Like other implants engineered for espionage-oriented functions, Woody RAT sports a large variety of characteristics that allows the menace actor to remotely commandeer and steal delicate data from the contaminated methods.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The earliest variations of this RAT were being normally archived into a ZIP file pretending to be a doc distinct to a Russian group,” Malwarebytes scientists Ankur Saini and Hossein Jazi explained in a Wednesday report.

“When the Follina vulnerability grew to become acknowledged to the entire world, the risk actor switched to it to distribute the payload.”
In one occasion, the hacking group tried to strike a Russian aerospace and protection entity identified as OAK based mostly on proof gleaned from a phony domain registered for this objective.
Attacks leveraging the Windows flaw as part of this marketing campaign 1st arrived to light on June 7, 2022, when researchers from the MalwareHunterTeam disclosed the use of a document named “Памятка.docx” (which interprets to “Memo.docx”) to supply a CSS payload containing the trojan.
The document purportedly offers best security procedures for passwords and private information, among the other folks, when acting as a decoy for dropping the backdoor.
Other than encrypting its communications with a remote server, Woody RAT is equipped with abilities to produce arbitrary data files to the machine, execute supplemental malware, delete documents, enumerate directories, seize screenshots, and get a list of running procedures.

Also embedded inside the malware are two .NET-based mostly libraries named WoodySharpExecutor and WoodyPowerSession that can be applied to operate .NET code and PowerShell instructions gained from the server, respectively.
Additionally, the malware tends to make use of the system hollowing strategy to inject alone into a suspended Notepad course of action and deletes itself from the disk to evade detection from security application set up on the compromised host.
Malwarebytes has yet to attribute the attacks to a distinct danger actor, citing a absence of good indicators linking the marketing campaign to a previously known team, while Chinese and North Korean nation-point out collectives have focused Russia in the previous.
Uncovered this report interesting? Follow THN on Fb, Twitter and LinkedIn to read through more distinctive written content we post.
Some sections of this article are sourced from:
thehackernews.com


 North Korean-linked Gmail spyware ‘SHARPEXT’ harvesting sensitive email content
North Korean-linked Gmail spyware ‘SHARPEXT’ harvesting sensitive email content