When I want to know the most not long ago released best practices in cyber security, I go to The Nationwide Institute of Expectations and Technology (NIST). From the most up-to-date password requirements (NIST 800-63) to IoT security for producers (NISTIR 8259), NIST is constantly the commencing point. NIST plays a important purpose as a US standard-setter, owing to the organization’s professionalism and the exterior industry experts who aid to make NIST files.
The NIST Cybersecurity Framework (CSF) was initially unveiled in 2014 and very last current in 2018. The framework allows organizations to make improvements to the security and resilience of critical infrastructure with a nicely-prepared and uncomplicated-to-use framework.
The continuing development in SaaS, and the main changes to the function setting due to COVID-19 convey new security issues. Whilst the CSF was prepared and up to date even though SaaS was on the increase, it is however geared to the vintage legacy critical infrastructure security challenges. On the other hand, companies can improved answer to new threats by adapting the CSF to fashionable, SaaS-based mostly do the job environments.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
I personally enjoy this Framework, but truth be explained to, when a single reads the Framework in-depth, its complexity is clear, and next it can be difficult. This write-up will evaluation the CSF’s important factors, place out its key merits, and propose implementations for SaaS security.
Study how to automate your organization’s NIST compliance
Overview of NIST CSF
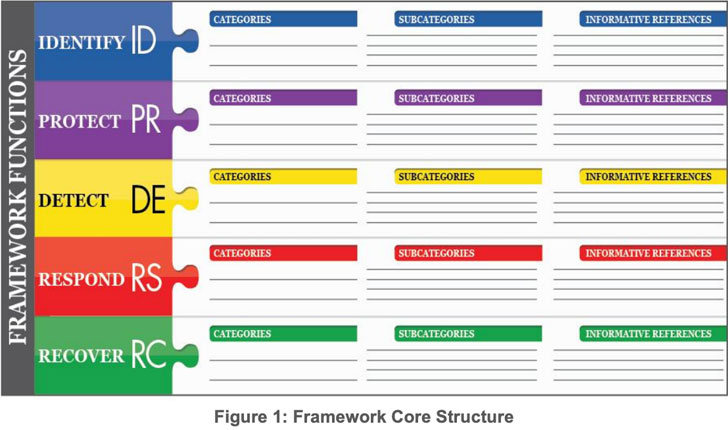
The NIST CSF lays out five functions of security, then splits them into groups and subcategories. The subcategories include the actual controls. For each subcategory, the CSF involves a record of cross-references to effectively-recognised standards and frameworks these types of as ISO 27001, COBIT, NIST SP 800-53, and ANSI/ISA-62443.
These cross-references enable corporations carry out the CSF and map it to other frameworks. For instance, security managers or other workforce users can use the references to justify their choices no make a difference what security regular the company desires to comply with.
In a one document, the Framework brings together a host of ways to dealing with cyber security threats. This features:
- location up processes
- education
- defining roles
- auditing
- checking
The framework has a 5-stage core framework: Determine, Secure, Detect, Answer and Recover. I’m likely to break them down into bullets for you.
Discover
NIST defines this operate as follows:
“Produce the organizational knowledge to control cybersecurity risk to techniques, property, info, and capabilities.”
In just this functionality, NIST involves the following control classes:
- Asset Administration
- Organization Atmosphere
- Governance
- Risk Assessment
- Risk Management Approach
- Supply Chain Risk Management.
Secure
NIST defines this functionality as follows:
“Create and put into practice the suitable safeguards to be certain shipping and delivery of critical infrastructure providers.”
Within this function, NIST includes the subsequent control types:
- Obtain Handle
- Consciousness and Training
- Info Security
- Facts Protection Processes and Treatments
- Routine maintenance
- Protective Technology
Detect
NIST defines this perform as follows:
“Create and put into practice the appropriate things to do to identify the occurrence of a cybersecurity celebration”.
Inside of this perform, NIST features the adhering to manage classes:
- Anomalies and Activities
- Security Continual Checking
- Detection Procedures
React
NIST defines this purpose as follows:
“Create and apply the correct things to do to acquire motion concerning a detected cybersecurity party”.
Within this purpose, NIST contains the subsequent regulate classes:
- Response Preparing
- Communications
- Analysis
- Mitigation
- Improvements
Get better
NIST defines this functionality as follows:
“Establish and put into practice the suitable things to do to maintain plans for resilience and to restore any capabilities or providers that have been impaired thanks to a cybersecurity event”.
In this perform, NIST features the adhering to regulate categories:
- Restoration Planning
- Improvements
- Communications
Implementing the CSF to SaaS Security
When certainly a product in best procedures, the Framework is a problem to put into action.
Learn more how a SaaS Security Posture Management (SSPM) solution can automate compliance to NIST across your SaaS estate.
Knowledge-in-transit is secured (PR.DS-2)
A company using SaaS products and services may surprise how this is applicable for them. They may well feel that compliance is the SaaS provider’s accountability. On the other hand, a further seem into it shows that a lot of SaaS vendors have security steps in spot, and the person is accountable for using them.
For illustration, admins should really not enable any connections by means of HTTP to a SaaS assistance. They must only let safe HTTPS connections.
Protections from info leaks are implemented (PR.DS-5)
This could seem like a modest subcategory, but underneath there is a behemoth. Information leaks are very hard to avoid. SaaS software adoption would make this tougher simply because men and women can share and obtain them from wherever in the earth.
An admin or member of the CISO office environment should really take distinctive treatment of this danger. DLP in SaaS can incorporate security actions these as:
- sharing one-way links to information relatively than the actual file
- environment an expiration date for the url
- disabling the download option if not essential
- blocking the capability to export details in details assessment SaaS
- user authentication hardening
- prevention of locale recording in communication SaaS
- properly-outlined user roles with a confined amount of super people and admins
Identities and credentials are issued, managed, confirmed, revoked, and audited for licensed gadgets, buyers and processes (PR.AC-1)
As an enterprise scales its workforce and SaaS adoption, this subcategory turns into much more hard. Running 50,000 people above just 5 SaaS signifies that the security group needs to deal with 250,000 identities. This challenge is real and challenging.
Even additional demanding, every single SaaS has a diverse way to define identities, perspective them, and protected identities. Introducing to the risk, SaaS programs do not normally integrate with each and every other, which indicates buyers can discover them selves with different privileges across different methods. This then qualified prospects to unneeded privileges that can create a potential security risk.
How Adaptive Defend Can Help Satisfy NIST CSF Needs
The NIST CSF is an industry-normal for cybersecurity now, still to put into practice it with normal handbook techniques and processes is an uphill struggle. So why not automate?
Adaptive Protect is a SaaS Security Posture Management (SSPM) answer that can automate the compliance and configuration checks throughout the SaaS estate. Adaptive Protect permits security teams to effortlessly see and correct configuration weaknesses promptly, making certain compliance with firm and sector requirements, from NIST CSF, as perfectly as other compliance mandates this kind of as SOC 2 and the CSA Cloud Controls Matrix.
Uncovered this post attention-grabbing? Comply with THN on Facebook, Twitter and LinkedIn to go through additional exclusive material we article.
Some components of this post are sourced from:
thehackernews.com

 Credential Stuffers Compromised 1.1 Million Accounts
Credential Stuffers Compromised 1.1 Million Accounts