A North Korean danger actor has been found getting benefit of two exploits in Internet Explorer to infect victims with a tailor made implant as section of a strategic web compromise (SWC) focusing on a South Korean on line newspaper.
Cybersecurity organization Volexity attributed the attacks to a danger actor it tracks as InkySquid, and much more extensively recognized by the monikers ScarCruft and APT37. Each day NK, the publication in problem, is mentioned to have hosted the malicious code from at the very least late March 2021 until finally early June 2021.
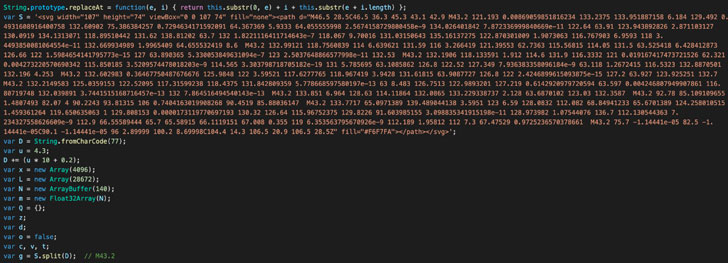
The “clever disguise of exploit code amongst legit code” and the use of customized malware permits the attackers to avoid detection, Volexity researchers said.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The attacks concerned tampering with the jQuery JavaScript libraries hosted on the website to provide additional obfuscated JavaScript code from a remote URL, using it to leverage exploits for two Internet Explorer flaws that were being patched by Microsoft in August 2020 and March 2021. Profitable exploitation resulted in the deployment of a Cobalt Strike stager and novel backdoor named BLUELIGHT.
- CVE-2020-1380 (CVSS rating: 7.5) – Scripting Motor Memory Corruption Vulnerability
- CVE-2021-26411 (CVSS score: 8.8) – Internet Explorer Memory Corruption Vulnerability
It is really worthy of noting that equally the flaws have been actively exploited in the wild, with the latter put to use by North Korean hackers to compromise security researchers doing work on vulnerability investigation and growth in a campaign that arrived to light-weight earlier this January.
In a independent established of attacks disclosed past month, an unidentified risk actor was found exploiting the same flaw to supply a thoroughly-highlighted VBA-based distant obtain trojan (RAT) on compromised Windows programs.

BLUELIGHT is utilised as a secondary payload adhering to the productive shipping of Cobalt Strike, performing as a total-featured distant obtain software that delivers complete access to a compromised program.
In addition to collecting process metadata and facts about set up antivirus solutions, the malware is able of executing shellcode, harvesting cookies and passwords from Internet Explorer, Microsoft Edge, and Google Chrome browsers, gathering files and downloading arbitrary executables, the outcomes of which are exfiltrated to a remote server.
“Although SWCs are not as common as they once were being, they go on to be a weapon in the arsenal of a lot of attackers,” the researchers mentioned. “The use of just lately patched exploits for Internet Explorer and Microsoft Edge will only function versus a minimal audience.”
Observed this posting interesting? Follow THN on Fb, Twitter and LinkedIn to go through extra unique articles we publish.
Some areas of this posting are sourced from:
thehackernews.com


 Unpatched Remote Hacking Flaw Disclosed in Fortinet’s FortiWeb WAF
Unpatched Remote Hacking Flaw Disclosed in Fortinet’s FortiWeb WAF