The prolific North Korean country-state actor recognised as the Lazarus Team has been connected to a new distant accessibility trojan identified as MagicRAT.
The beforehand not known piece of malware is reported to have been deployed in victim networks that experienced been at first breached by using effective exploitation of internet-going through VMware Horizon servers, Cisco Talos explained in a report shared with The Hacker News.
“When being a relatively simple RAT functionality-smart, it was built with recourse to the Qt Framework, with the sole intent of making human analysis harder, and automated detection as a result of device studying and heuristics considerably less probably,” Talos scientists Jung soo An, Asheer Malhotra, and Vitor Ventura reported.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Lazarus Team, also known as APT38, Dark Seoul, Hidden Cobra, and Zinc, refers to a cluster of economical inspired and espionage-driven cyber pursuits carried out by the North Korean governing administration as a suggests to sidestep sanctions imposed on the place and meet up with its strategic objectives.
Like other umbrella collectives like Winnti and MuddyWater, the state-sponsored hacking collective also has “spin-off” teams this kind of as Bluenoroff and Andariel, which focus on specific varieties of attacks and targets.
While the Bluenoroff subgroup is targeted on attacking international fiscal establishments and perpetrating financial theft, Andariel is devoted in its pursuit of South Korean companies and firms.
“Lazarus develops their individual attack equipment and malware, can use impressive attack tactics, performs incredibly methodically, and usually takes their time,” cybersecurity organization NCC Group claimed in a report detailing the menace actor.
“In particular, the North Korean strategies purpose to keep away from detection by security products and to stay undetected in just the hacked techniques for as prolonged as attainable.”
The most recent addition to its wide-ranging malware toolset reveals the group’s potential to make use of a multitude of methods and approaches dependent on their targets and their objectives.
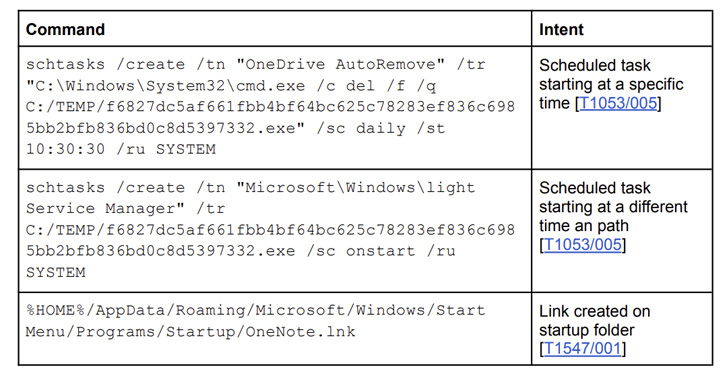
A C++-based implant, MagicRAT is made to accomplish persistence by generating scheduled responsibilities on the compromised procedure. It is also “alternatively uncomplicated” in that it provides the attacker with a remote shell to execute arbitrary commands and have out file operations.

MagicRAT is also capable of launching added payloads retrieved from a remote server on contaminated hosts. A person of the executables retrieved from the command-and-management (C2) server takes the sort of a GIF graphic file, but in actuality is a lightweight port scanner.
Moreover, the C2 infrastructure affiliated with MagicRAT has been observed harboring and serving more recent variations of TigerRAT, a backdoor formerly attributed to Andariel and is engineered to execute instructions, choose screenshots, log keystrokes, and harvest process facts.
Also incorporated in the hottest variant is a USB Dump element that will allow the adversary to hunt for information with unique extensions, along with laying the groundwork for implementing video seize from webcams.
“The discovery of MagicRAT in the wild is an indication of Lazarus’ motivations to fast establish new, bespoke malware to use alongside with their beforehand regarded malware these kinds of as TigerRAT to concentrate on companies worldwide,” the scientists said.
Identified this post interesting? Observe THN on Facebook, Twitter and LinkedIn to browse a lot more exclusive content material we publish.
Some areas of this write-up are sourced from:
thehackernews.com


 4 Key Takeaways from “XDR is the Perfect Solution for SMEs” webinar
4 Key Takeaways from “XDR is the Perfect Solution for SMEs” webinar