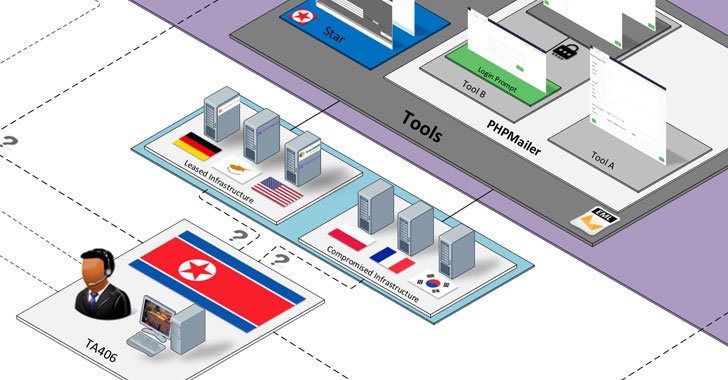
A danger actor with ties to North Korea has been linked to a prolific wave of credential theft campaigns targeting investigation, instruction, government, media and other organizations, with two of the attacks also attempting to distribute malware that could be made use of for intelligence collecting.
Enterprise security business Proofpoint attributed the infiltrations to a group it tracks as TA406, and by the wider risk intelligence neighborhood underneath the monikers Kimsuky (Kaspersky), Velvet Chollima (CrowdStrike), Thallium (Microsoft), Black Banshee (PwC), ITG16 (IBM), and the Konni Team (Cisco Talos).
Plan gurus, journalists and nongovernmental corporations (NGOs) were being targeted as component of weekly strategies noticed concerning from January via June 2021, Proofpoint researchers Darien Huss and Selena Larson disclosed in a complex report detailing the actor’s strategies, tactics, and procedures (TTPs), with the attacks unfold across North The us, Russia, China, and South Korea.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Recognized to be operational as early as 2012, Kimsuky has considering that emerged as a person of the most energetic sophisticated persistent risk (APT) group acknowledged for placing its sights on cyber espionage but also for conducting attacks for fiscal acquire, targeting governing administration entities, believe tanks, and people identified as specialists in numerous fields as effectively as harvest sensitive information pertaining to international plan and countrywide security issues.

“Like other APT teams that represent a significant umbrella, Kimsuky includes numerous clusters: BabyShark, AppleSeed, Flower Energy, and Gold Dragon,” Kaspersky researchers noted in their Q2 2021 APT trends report posted last thirty day period. The AppleSeed sub-team is also referred to as TA408.
The group is also acknowledged for reeling in targets with convincing social engineering strategies and watering hole attacks just before sending them malware-infected payloads or tricking them into publishing delicate qualifications to phishing websites, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) mentioned in a general public alert issued in Oct 2020.
Earlier this month, scientists from Cisco Talos disclosed an ongoing Kimsuky marketing campaign considering the fact that June 2021 that was found leveraging destructive weblogs hosted on Google’s Blogger platform to goal significant-benefit South Korean targets, which includes geopolitical and aerospace study agencies, with the aim of offering a “frequently evolving established of implants derived from the Gold Dragon/Brave Prince relatives” that act as file exfiltrators, details gatherers, and credential stealers for reconnaissance, espionage, and credential harvesting.
“This marketing campaign begins with malicious Microsoft Business paperwork (maldocs) that contains macros staying shipped to victims,” Talos scientists explained. “The infection chain outcomes in the malware achieving out to destructive blogs set up by the attackers. These weblogs deliver the attackers the ability to update the destructive content posted in the website relying on regardless of whether a sufferer is of benefit to the attackers.”
Now in what appears to be a more ramping up of attacks, the risk actor at the same time commenced in close proximity to-weekly email menace campaigns employing the identities of respectable plan experts, whilst showcasing themes linked to nuclear weapon security, politics, and Korean foreign coverage, finally luring the targeted people today to give up their company qualifications by way of a rogue URL embedded in the messages that redirect the victims to custom made credential-harvesting internet pages.
Kimsuky’s phishing campaigns had a visible change in March 2021 when the emails moved over and above credential theft to grow to be a medium for distributing malware, coinciding with North Korea’s missile tests performed afterwards that thirty day period.

The e-mails incorporated a website link that despatched the concentrate on to an attacker-controlled domain utilised to trick targets into downloading a compressed archive incorporating a binary, which is orchestrated to make a scheduled activity that is executed each and every 15 minutes to install additional malware from a distant server. Nevertheless, the top motive powering the attacks stays unclear as no observe-on payloads were being observed.
An additional notable attack in June resulted in the deployment of a downloader (“FatBoy”) employing an HTML attachment entice that was then made use of to retrieve a following-stage reconnaissance script able of collecting “considerable info” about the qualified device. Proofpoint stated that each the strategies exhibited overlaps with attacks formerly identified as mounted by the Konni Team.
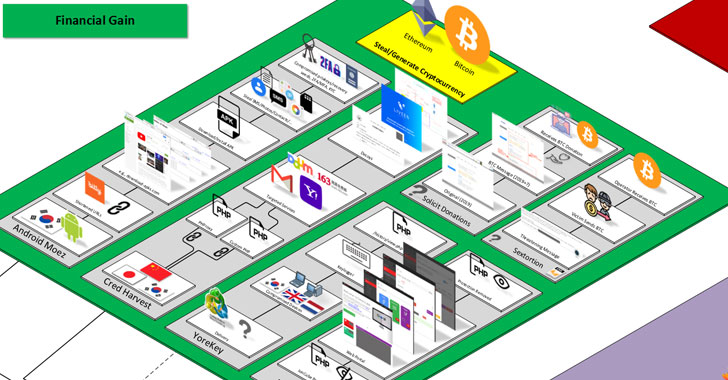
Other notable tools in its malware arsenal encompass a Windows keylogger dubbed YoreKey, a quantity of rogue Android applications hanging cryptocurrency users in South Korea, a deobfuscation provider named Deioncube to decode data files encrypted with ionCube’s source code security software program, and a sextortion scam that urges email recipients to transfer an volume worth $500 in bitcoin to a valid wallet associated with a South Korea-dependent NGO.
“It’s unknown regardless of whether the NGO was compromised, and the donation message was put on their site maliciously, or if there is another explanation,” the scientists explained. “As of June 2021, the involved bitcoin wallet had been given and despatched about 3.77 bitcoin.”
Identified this report fascinating? Stick to THN on Facebook, Twitter and LinkedIn to go through additional exceptional information we write-up.
Some elements of this article are sourced from:
thehackernews.com

 Brit Admits Role in International Movie Piracy Ring
Brit Admits Role in International Movie Piracy Ring