Lazarus, the North Korea-affiliated point out-sponsored team, is trying to once again target security researchers with backdoors and distant entry trojans employing a trojanized pirated version of the well known IDA Pro reverse engineering software package.
The results were being documented by ESET security researcher Anton Cherepanov previous week in a series of tweets.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
IDA Pro is an Interactive Disassembler that’s designed to translate equipment language (aka executables) into assembly language, enabling security researchers to review the internal workings of a program (malicious or or else) as perfectly as perform as a debugger to detect errors.

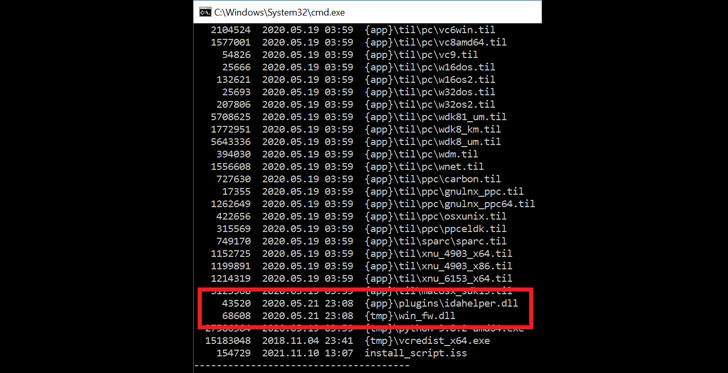
“Attackers bundled the original IDA Pro 7.5 software package created by [Hex-Rays] with two malicious factors,” the Slovak cybersecurity company stated, one of which is an internal module identified as “acquire_fw.dll” that’s executed through set up of the programs. This tampered version is then orchestrated to load a 2nd ingredient named “idahelper.dll” from the IDA plugins folder on the process.
On prosperous execution, the “idahelper.dll” binary connects to a distant server at “www[.]devguardmap[.]org” to retrieve subsequent payloads. The area is also noteworthy for the fact that it really is been previously connected to a identical North Korea-backed campaign aimed at security specialists and disclosed by Google’s Menace Examination Group before this March.
The covert procedure involved the adversaries environment up a bogus security firm acknowledged as SecuriElite alongside a amount of social media accounts throughout Twitter and LinkedIn in an try to trick unsuspecting researchers into viewing the company’s malware-laced website so as to set off an exploit that leveraged a then zero-working day in Internet Explorer browser. Microsoft eventually resolved the issue in its Patch Tuesday update for March 2021.

Also recognised by the monikers APT38, Hidden Cobra, and Zinc, the Lazarus Team is identified to be energetic as early as 2009 and linked to a string of attacks for monetary gain and harvesting sensitive information from compromised environments.
“North Korea’s cyber program poses a developing espionage, theft, and attack menace,” in accordance to the U.S. Office environment of the Director of National Intelligence 2021 Annual Risk Assessment posted before this April.
“North Korea has executed cyber theft from money institutions and cryptocurrency exchanges worldwide, perhaps stealing hundreds of millions of pounds, almost certainly to fund federal government priorities, this kind of as its nuclear and missile programs.”
Discovered this article exciting? Abide by THN on Facebook, Twitter and LinkedIn to browse more exceptional material we put up.
Some components of this posting are sourced from:
thehackernews.com


 FBI Fixes Misconfigured Server After Hoax Email Alert
FBI Fixes Misconfigured Server After Hoax Email Alert