A destructive marketing campaign mounted by the North Korea-connected Lazarus Group is targeting electricity companies all over the planet, which includes those dependent in the United States, Canada, and Japan.
“The campaign is meant to infiltrate businesses around the globe for establishing prolonged-term access and subsequently exfiltrating info of desire to the adversary’s country-point out,” Cisco Talos said in a report shared with The Hacker News.
Some features of the espionage attacks have already entered general public domain, courtesy of prior stories from Broadcom-owned Symantec and AhnLab previously this April and Might.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Symantec attributed the operation to a group referred to as Stonefly, a Lazarus subgroup which is much better recognized as Andariel, Guardian of Peace, OperationTroy, and Silent Chollima.
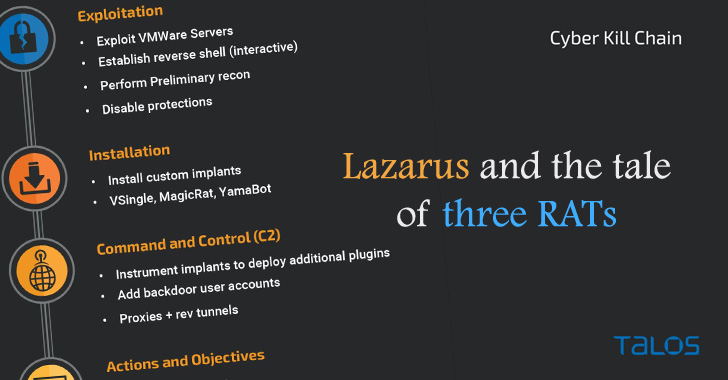
While these attacks earlier led to the instrumentation of Preft (aka Dtrack) and NukeSped (aka Manuscrypt) implants, the most up-to-date attack wave is notable for using two other items of malware: VSingle, an HTTP bot which executes arbitrary code from a remote network, and a Golang backdoor called YamaBot.
Also place to use in the campaign is a new remote accessibility trojan referred to as MagicRAT that arrives with abilities to evade detection and launch added payloads on the contaminated programs.
“Whilst the very same techniques have been applied in both of those attacks, the resulting malware implants deployed have been unique from 1 another, indicating the broad assortment of implants out there at the disposal of Lazarus,” researchers Jung soo An, Asheer Malhotra, and Vitor Ventura said.

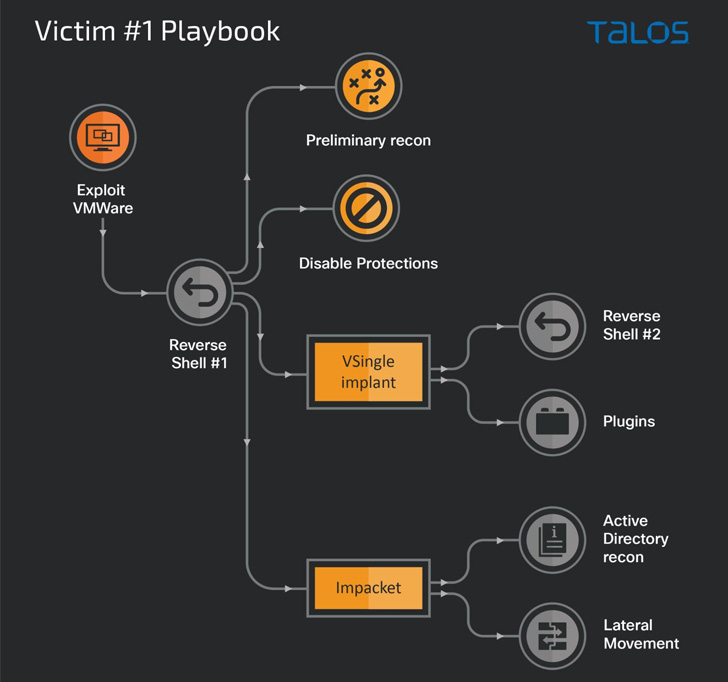
Initial obtain into company networks is facilitated by indicates of exploitation of vulnerabilities in VMware goods (e.g., Log4Shell), with the ultimate objective of creating persistent accessibility to carry out routines in help of North Korean governing administration goals.
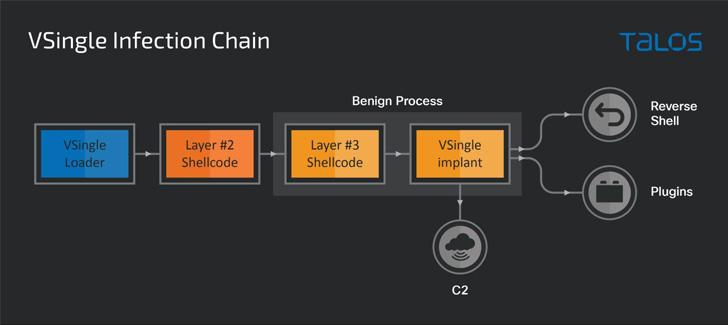
The use of VSingle in one attack chain is mentioned to have enabled the menace actor to have out a wide range of activities these as reconnaissance, exfiltration, and guide backdooring, supplying the operators a good understanding of the sufferer atmosphere.
Other practices embraced by the group other than the use of bespoke malware involve credential harvesting via instruments like Mimikatz and Procdump, disabling antivirus elements, and reconnaissance of the Active Directory companies, and even having techniques to cleanup their traces following activating the backdoors on the endpoint.
Identified this report attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to go through far more distinctive written content we write-up.
Some pieces of this report are sourced from:
thehackernews.com

 Portugal government cyber attack allegedly leaks “hundreds” of classified NATO documents
Portugal government cyber attack allegedly leaks “hundreds” of classified NATO documents