In its April slate of patches, Microsoft rolled out fixes for a full of 114 security flaws, together with an actively exploited zero-day and four remote code execution bugs in Trade Server.
Of the 114 flaws, 19 are rated as Critical, 88 are rated Crucial, and one is rated Average in severity.
Chief amongst them is CVE-2021-28310, a privilege escalation vulnerability in Acquire32k which is said to be less than active exploitation, making it possible for attackers to elevate privileges by jogging malicious code on a goal process.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Cybersecurity business Kaspersky, which uncovered and reported the flaw to Microsoft in February, joined the zero-day exploit to a threat actor named Bitter APT, which was observed exploiting a similar flaw (CVE-2021-1732) in attacks late final calendar year.
“It is an escalation of privilege (EoP) exploit that is very likely applied alongside one another with other browser exploits to escape sandboxes or get system privileges for even more access,” Kaspersky researcher Boris Larin claimed.
NSA Identified New Bugs Affecting Trade Server
Microsoft also stated four extra vulnerabilities were publicly acknowledged at the time of launch but not exploited —
- CVE-2021-28458 – Azure ms-relaxation-nodeauth Library Elevation of Privilege Vulnerability
- CVE-2021-27091 – RPC Endpoint Mapper Assistance Elevation of Privilege Vulnerability
- CVE-2021-28437 – Windows Installer Facts Disclosure Vulnerability
- CVE-2021-28312 – Windows NTFS Denial of Support Vulnerability
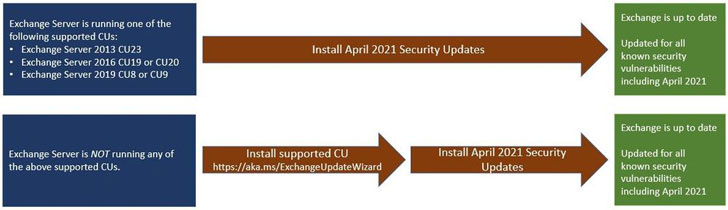
Also fastened by Microsoft are 4 distant code execution (RCE) flaws (CVE-2021-28480 by means of CVE-2021-28483) influencing on-premises Trade Servers 2013, 2016, and 2019 that were being described to the firm by the U.S. National Security Company (NSA). Two of the code execution bugs are unauthenticated and demand no user conversation, and have a CVSS rating of 9.8 out of a optimum of 10.
Whilst the Windows maker claimed it had uncovered no proof of any lively exploits in the wild, it is really suggested that shoppers set up these updates as quickly as achievable to safe the atmosphere, in light-weight of the popular Trade Server hacks previous thirty day period and new findings that attackers are trying to leverage the ProxyLogon exploit to deploy destructive cryptominers on to Trade Servers, with the payload becoming hosted on a compromised Trade Server.
FBI Taken off Backdoors From Hacked MS Exchange servers
What’s additional, the U.S. Federal Bureau of Investigation (FBI) carried out a “prosperous action” to “duplicate and get rid of” web shells planted by adversaries on hundreds of target desktops utilizing the ProxyLogon flaws. “The FBI executed the removal by issuing a command via the web shell to the server, which was made to cause the server to delete only the web shell (discovered by its exceptional file route),” the Justice Section stated in a assertion detailing the court-authorized operation.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has also revised the crisis directive it issued previous thirty day period, stating “these vulnerabilities pose an unacceptable risk to the Federal enterprise and have to have an fast and unexpected emergency motion,” when cautioning that the fundamental flaws can be weaponized by reverse-engineering the patch to create an exploit.
Software Patches From Other Sellers
In addition, April’s Patch Tuesday update also addresses a whopping 27 RCE flaws in Distant Procedure Simply call (RPC) runtime, a Hyper-V security attribute bypass vulnerability (CVE-2021-28444), and a number of privilege escalation flaws in Windows Speech Runtime, Windows Solutions and Controller App, Windows Safe Kernel Mode, Windows Celebration Tracing, and Windows Installer.
Besides Microsoft, a number of other vendors have also unveiled a slew of patches on Tuesday —
- Adobe (security updates for Photoshop, Electronic Editions, RoboHelp, and Bridge)
- DELL
- Linux distributions SUSE, Oracle Linux, and Red Hat
- SAP
- Schneider Electrical, and
- Siemens
Located this report intriguing? Stick to THN on Facebook, Twitter and LinkedIn to read much more exceptional content we article.
Some components of this short article are sourced from:
thehackernews.com


 DoJ used court order to thwart ‘hundreds’ of Exchange Server web shells
DoJ used court order to thwart ‘hundreds’ of Exchange Server web shells