The U.S. Nationwide Security Company (NSA) on Friday mentioned DNS in excess of HTTPS (DoH) — if configured properly in enterprise environments — can assistance stop “many” initial entry, command-and-control, and exfiltration methods made use of by danger actors.
“DNS more than Hypertext Transfer Protocol in excess of Transportation Layer Security (HTTPS), typically referred to as DNS around HTTPS (DoH), encrypts DNS requests by applying HTTPS to deliver privacy, integrity, and ‘last mile’ source authentication with a client’s DNS resolver,” in accordance to the NSA’s new steerage.
Proposed in 2018, DoH is a protocol for accomplishing remote Area Identify Program resolution by way of the HTTPS protocol.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
1 of the main shortcomings with existing DNS lookups is that even when somebody visits a web-site that utilizes HTTPS, the DNS question and its response is despatched about an unencrypted connection, as a result making it possible for 3rd-party eavesdropping on the network to monitor each web page a person is going to.
Even worse, the set up is ripe for carrying out gentleman-in-the-middle (MiTM) attacks only by switching the DNS responses to redirect unsuspecting people to a malware-laced web site of the adversary’s preference.
Thus by working with HTTPS to encrypt the data concerning the DoH client and the DoH-dependent DNS resolver, DoH aims to enhance user privacy and security by avoiding eavesdropping and manipulation of DNS facts by MiTM attacks.
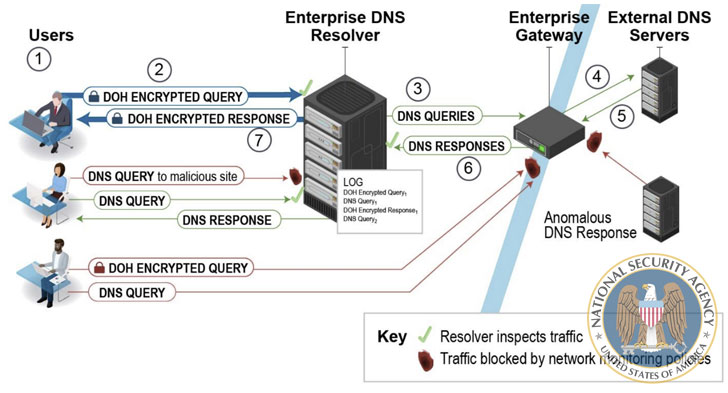
To that impact, the NSA endorses utilizing only designated organization DNS resolvers to reach the preferred cybersecurity defense, though noting that such resolvers will be bypassed fully when a shopper has DoH enabled and is configured to use a DoH resolver not designated by the business.
The gateway, which is employed to forward the question to external authoritative DNS servers in the party the organization DNS resolver does not have the DNS response cached, must be intended to block DNS, DoH, and DNS above TLS (DoT) requests to external resolvers and DNS servers that are not from the company resolver, the agency included.
Whilst DoH safeguards DNS transactions from unauthorized modification, the NSA cautioned of a “fake sense of security.”
“DoH does not ensure security from cyber menace actors and their ability to see wherever a customer is likely on the web,” it claimed. “DoH is specially designed to encrypt only the DNS transaction between the consumer and resolver, not any other targeted traffic that takes place immediately after the question is happy.”
“Enterprises that allow DoH without the need of a strategic and complete approach can stop up interfering with network monitoring instruments, protecting against them from detecting destructive menace action inside of the network, and enabling cyber threat actors and malware to bypass the selected organization DNS resolvers.”
What’s a lot more, the encryption does practically nothing to reduce the DNS service provider from looking at the two the lookup requests as nicely as the IP tackle of the consumer building them, properly undermining privacy protections and earning it probable for a DNS service provider to generate detailed profiles based mostly on users’ browsing patterns.
Oblivious DNS-about-HTTPS (ODoH), announced previous thirty day period by engineers at Apple, Cloudflare, and Fastly, aims to tackle this issue. It helps prevent the DoH resolver from realizing which consumer asked for what area names bypassing all requests by way of a proxy that separates the IP addresses from the queries, “so that no solitary entity can see each at the very same time.”
Place differently, this implies the proxy does not know the contents of queries and responses, and the resolver does not know the IP addresses of the consumers.
Secondly, the use of DoH also doesn’t negate the possibility that resolvers that converse with destructive servers upstream could however be inclined to DNS cache poisoning.
“DNSSEC ought to be applied to guard the upstream responses, but the DoH resolver may perhaps not validate DNSSEC,” the NSA stated. “Enterprises that do not comprehend which elements of the DNS system are vulnerable could slide into a bogus perception of security.”
Discovered this posting fascinating? Follow THN on Fb, Twitter and LinkedIn to read through much more distinctive content material we post.
Some parts of this article are sourced from:
thehackernews.com

 Joker’s Stash, The Largest Carding Marketplace, Announces Shutdown
Joker’s Stash, The Largest Carding Marketplace, Announces Shutdown