A freshly noticed banking trojan has been caught leveraging legitimate platforms like YouTube and Pastebin to keep its encrypted, distant configuration and commandeer contaminated Windows units, building it the most recent to be part of the prolonged record of malware focusing on Latin The us (LATAM) after Guildma, Javali, Melcoz, Grandoreiro, Mekotio, Casbaneiro, Amavaldo, Vadokrist, and Janeleiro.
The threat actor guiding this malware family — dubbed “Numando” — is thought to have been lively given that at the very least 2018.
“[Numando brings] interesting new strategies to the pool of Latin American banking trojans’ methods, like working with seemingly useless ZIP archives or bundling payloads with decoy BMP pictures,” ESET scientists stated in a technological investigation printed on Friday. “Geographically, it focuses virtually solely on Brazil with exceptional strategies in Mexico and Spain.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Penned in Delphi, the malware arrives with an array of backdoor abilities that make it possible for it to management compromised equipment, simulate mouse and keyboard steps, restart and shutdown the host, display screen overlay windows, seize screenshots, and terminate browser procedures. Numando is “pretty much solely” propagated by spam strategies, ensnaring various hundred victims to day, according to the cybersecurity firm’s telemetry data.
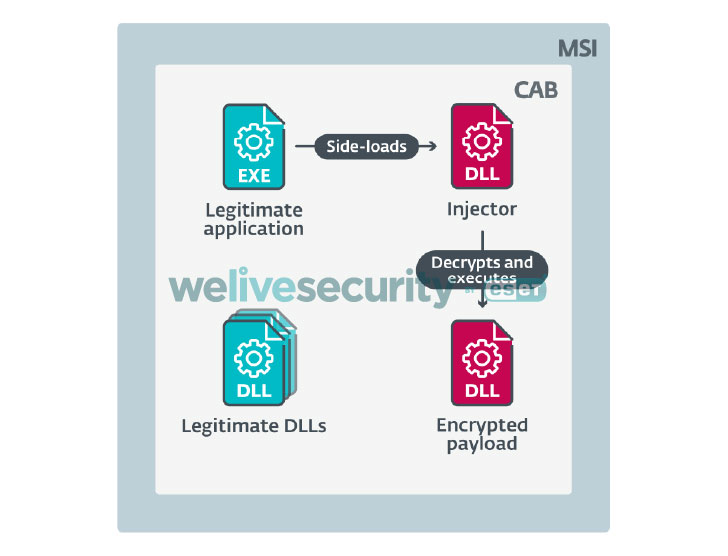
The attacks start out with a phishing information that will come embedded with a ZIP attachment made up of an MSI installer, which, in turn, includes a cupboard archive with a legit software, an injector, and an encrypted Numando banking trojan DLL. Executing the MSI qualified prospects to the execution of the software, leading to the injector module to be aspect-loaded and decrypt the last-phase malware payload.

In an alternate distribution chain observed by ESET, the malware will take the variety of a “suspiciously huge” but legitimate BMP image file, from which the injector extracts and executes the Numando banking trojan. What will make the marketing campaign stand out is its use of YouTube online video titles and descriptions — now taken down — to retailer the remote configuration these types of as the IP address of the command-and-regulate server.
“[The malware] uses phony overlay windows, includes backdoor operation, and utilizes MSI [installer],” the scientists claimed. “It is the only LATAM banking trojan written in Delphi that works by using a non-Delphi injector and its remote configuration structure is unique, generating two trusted variables when determining this malware family.”
Uncovered this short article appealing? Stick to THN on Facebook, Twitter and LinkedIn to read additional exclusive content we post.
Some components of this report are sourced from:
thehackernews.com


 Prison for AT&T Phone-Unlocking Fraudster
Prison for AT&T Phone-Unlocking Fraudster