U.S. graphics chip expert NVIDIA has released software updates to tackle a whole of 26 vulnerabilities impacting its Jetson process-on-module (SOM) sequence that could be abused by adversaries to escalate privileges and even direct to denial-of-provider and data disclosure.

Tracked from CVE‑2021‑34372 by means of CVE‑2021‑34397, the flaws affect products Jetson TX1, TX2 series, TX2 NX, AGX Xavier series, Xavier NX, and Nano and Nano 2GB operating all Jetson Linux versions prior to 32.5.1. The organization credited Frédéric Perriot of Apple Media Solutions for reporting all the issues.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The NVIDIA Jetson line consists of embedded Linux AI and computer system eyesight compute modules and developer kits that primarily caters to AI-based mostly personal computer vision programs and autonomous techniques such as cellular robots and drones.
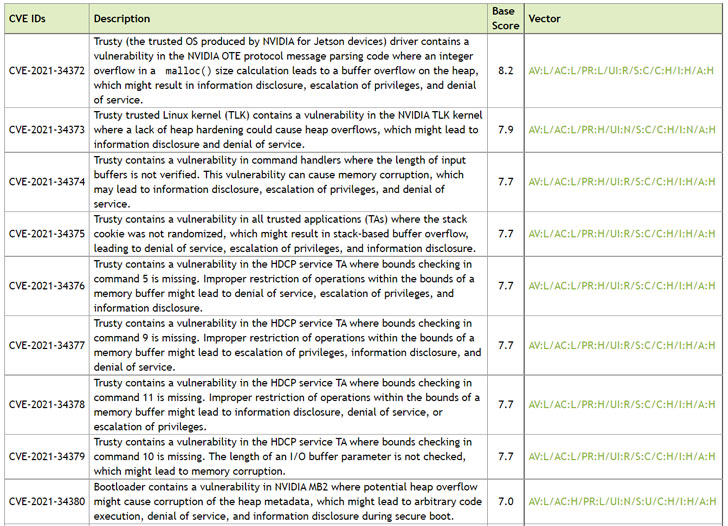
Main amongst the vulnerabilities is CVE‑2021‑34372 (CVSS score: 8.2), a buffer overflow flaw in its Trusty reliable execution surroundings (TEE) that could consequence in details disclosure, escalation of privileges, and denial-of-company.

8 other critical weaknesses involve memory corruption, stack overflows, and missing bounds checks in the TEE as properly as heap overflows influencing the Bootloader that could direct to arbitrary code execution, denial-of-support, and information disclosure. The relaxation of the flaws, also connected to Trusty and Bootloader, could be exploited to impression code execution, leading to denial-of-service and info disclosure, the corporation pointed out.
“Previously software package department releases that aid this item are also afflicted,” NVIDIA mentioned. “If you are utilizing an before branch launch, upgrade to the latest 32.5.1 launch. If you are utilizing the 32.5.1 release, update to the most up-to-date Debian deals.”
Found this report interesting? Comply with THN on Fb, Twitter and LinkedIn to browse extra special articles we submit.
Some parts of this posting are sourced from:
thehackernews.com


 50% of misconfigured containers hit by botnets in under an hour
50% of misconfigured containers hit by botnets in under an hour