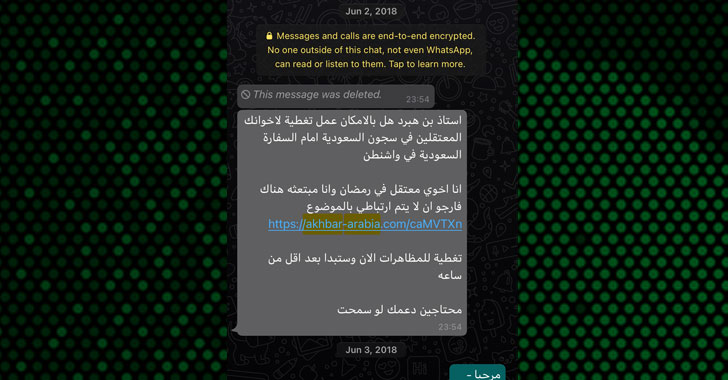
The iPhone of New York Occasions journalist Ben Hubbard was consistently hacked with NSO Group’s Pegasus adware instrument in excess of a three-12 months time period stretching amongst June 2018 to June 2021, ensuing in infections twice in July 2020 and June 2021.
The College of Toronto’s Citizen Lab, which publicized the findings on Sunday, reported the “focusing on took position while he was reporting on Saudi Arabia, and crafting a reserve about Saudi Crown Prince Mohammed bin Salman.” The analysis institute did not attribute the infiltrations to a unique federal government.
In a assertion shared with Hubbard, the Israeli company denied its involvement in the hacks and dismissed the results as “speculation,” when noting that the journalist was not “a goal of Pegasus by any of NSO’s buyers.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

To day, NSO Team is believed to have leveraged at minimum 3 distinctive iOS exploits — particularly an iMessage zero-click on exploit in December 2019, a KISMET exploit focusing on iOS 13.5.1 and iOS 13.7 starting July 2020, and a FORCEDENTRY exploit aimed at iOS 14.x until finally 14.7.1 considering the fact that February 2021.
It can be worth pointing out that Apple’s iOS 14 update incorporates a BlastDoor Framework that’s made to make zero-click exploitation much more difficult, though FORCEDENTRY expressly undermines that pretty security attribute designed into the working process, prompting Apple to issue an update to remediate the shortcoming in September 2021.
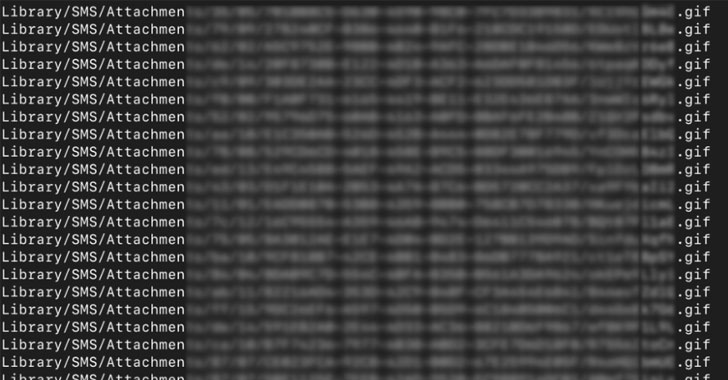
Forensic investigation into the marketing campaign has exposed that Hubbard’s iPhone was successfully hacked with the surveillance computer software 2 times on July 12, 2020 and June 13, 2021, once every by using the KISMET and FORCEDENTRY zero-click on iMessage exploits, soon after earning two previously unsuccessful attempts by way of SMS and WhatsApp in 2018.
The disclosure is the most up-to-date in a lengthy list of documented scenarios of activists, journalists, and heads of state being focused or hacked utilizing the firm’s “navy-quality spyware.” Previously revelations in July laid bare an in depth abuse of the tool by many authoritarian governments to facilitate human legal rights violations all around the earth.
The conclusions are also especially important in light-weight of a new interim rule passed by the U.S. governing administration that requires that firms dabbling in intrusion application obtain a license from the Commerce Division ahead of exporting these types of “cybersecurity objects” to nations around the world of “countrywide security or weapons of mass destruction worry.”
“As extensive as we keep our life on products that have vulnerabilities, and surveillance corporations can generate millions of dollars providing methods to exploit them, our defenses are constrained, specially if a government decides it wants our information,” Hubbard wrote in the New York Instances.
“Now, I restrict the info I retain on my phone. I reboot my phone frequently, which can kick out (but not keep off) some spy packages. And, when feasible, I resort to just one of the handful of non-hackable possibilities we even now have: I leave my phone guiding and meet up with people facial area to facial area,” Hubbard additional.
Uncovered this report attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to go through more exceptional material we post.
Some elements of this article are sourced from:
thehackernews.com

 Microsoft Warns of TodayZoo Phishing Kit Used in Extensive Credential Stealing Attacks
Microsoft Warns of TodayZoo Phishing Kit Used in Extensive Credential Stealing Attacks