An ongoing crypto mining marketing campaign has upgraded its arsenal while introducing new defense evasion methods that permit the risk actors to conceal the intrusions and fly underneath the radar, new investigate released now has unveiled.
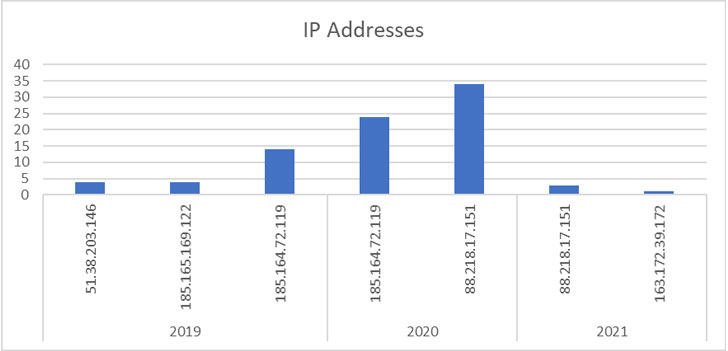
Considering the fact that initial detected in 2019, a full of 84 attacks towards its honeypot servers have been recorded to date, 4 of which transpired in 2021, in accordance to researchers from DevSecOps and cloud security agency Aqua Security, who have been monitoring the malware operation for the earlier 3 years. That reported, 125 attacks have been spotted in the wild in the 3rd quarter of 2021 by yourself, signaling that the attacks have not slowed down.
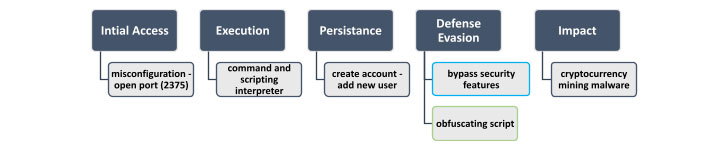
Preliminary attacks involved executing a malicious command upon functioning a vanilla graphic named “alpine:most current” that resulted in the obtain of a shell script named “autom.sh.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Adversaries commonly use vanilla pictures together with malicious instructions to conduct their attacks, since most organizations belief the formal images and allow their use,” the scientists said in a report shared with The Hacker News. “Above the years, the destructive command that was additional to the official image to carry out the attack has barely changed. The primary variation is the server from which the shell script autom.sh was downloaded.”

The shell script initiates the attack sequence, enabling the adversary to build a new user account beneath the title “akay” and upgrade its privileges to a root person, utilizing which arbitrary instructions are run on the compromised equipment with the purpose of mining cryptocurrency.
While early levels of the marketing campaign in 2019 featured no particular strategies to hide the mining activity, later on versions demonstrate the excessive measures its developers have taken to keep it invisible to detection and inspection, chief among the them becoming the potential to disable security mechanisms and retrieve an obfuscated mining shell script that was Base64-encoded 5 situations to get all over security instruments.
Malware strategies carried out to hijack pcs to mine cryptocurrencies have been dominated by multiple menace actors these kinds of as Kinsing, which has been identified scanning the internet for misconfigured Docker servers to crack into the unprotected hosts and install a earlier undocumented coin miner pressure.
On major of that, a hacking team named TeamTNT has been observed hanging unsecured Redis databases servers, Alibaba Elastic Computing Company (ECS) cases, exposed Docker APIs, and vulnerable Kubernetes clusters in buy to execute destructive code with root privileges on the targeted hosts as properly as deploy cryptocurrency-mining payloads and credential stealers. In addition, compromised Docker Hub accounts have also been employed to host destructive illustrations or photos that ended up then made use of to distribute cryptocurrency miners.
In recent months, security flaws in the Log4j logging library as very well as vulnerabilities a short while ago uncovered in Atlassian Confluence, F5 Significant-IP, VMware vCenter, and Oracle WebLogic Servers have been abused to consider about machines to mine cryptocurrencies, a plan recognized as cryptojacking. Before this month, network-attached storage (NAS) equipment maker QNAP warned of cryptocurrency mining malware concentrating on its devices that could occupy all over 50% of the whole CPU utilization.
“Miners are a minimal-risk way for cybercriminals to turn a vulnerability into digital income, with the finest risk to their money circulation remaining competing miners getting the very same susceptible servers,” Sophos senior menace researcher Sean Gallagher pointed out in an examination of a Tor2Mine mining marketing campaign, which requires the use of a PowerShell script to disable malware safety, execute a miner payload, and harvest Windows credentials.
“The Autom marketing campaign illustrates that attackers are becoming a lot more refined, continuously increasing their methods and their ability to prevent detection by security methods,” the scientists reported. To secure in opposition to these threats, it truly is recommended to keep an eye on suspicious container activity, perform dynamic impression examination, and routinely scan the environments for misconfiguration issues.
Located this report appealing? Follow THN on Fb, Twitter and LinkedIn to browse a lot more exceptional articles we post.
Some sections of this short article are sourced from:
thehackernews.com



 5 Cybersecurity Trends to Watch in 2022
5 Cybersecurity Trends to Watch in 2022