With browser makers steadily clamping down on 3rd-party tracking, marketing technology businesses are progressively embracing a DNS approach to evade this kind of defenses, thereby posing a menace to web security and privacy.
Referred to as CNAME Cloaking, the observe of blurring the distinction among very first-party and third-party cookies not only success in leaking sensitive non-public data with out users’ know-how and consent but also “raises [the] web security threat area,” claimed a group of researchers Yana Dimova, Gunes Acar, Lukasz Olejnik, Wouter Joosen, and Tom Van Goethem in the most recent investigation.
“This monitoring plan normally takes advantage of a CNAME file on a subdomain these that it is same-site to the like web internet site,” the scientists mentioned in the paper. “As these, defenses that block 3rd-party cookies are rendered ineffective.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The findings are expected to be presented in July at the 21st Privacy Maximizing Technologies Symposium (Animals 2021).
Increase of Anti-Monitoring Actions
Above the earlier four decades, all key browsers, with the notable exception of Google Chrome, have integrated countermeasures to suppress third-party tracking.
Apple set the ball rolling with a Safari element named Smart Monitoring Safety (ITP) in June 2017, placing a new privacy regular on desktop and mobile to cut down cross-web-site tracking by “even further restricting cookies and other web site info.” Two many years afterwards, the iPhone maker outlined a independent plan dubbed “Privacy Preserving Advertisement Click Attribution” to make on line adverts personal.
Mozilla then commenced blocking 3rd-party cookies in Firefox by default as of September 2019 through a function named Improved Monitoring Safety (ETP), and in January 2020, Microsoft’s Chromium-based mostly Edge browser followed go well with. Subsequently, in late March 2020, Apple current ITP with entire third-party cookie blocking, among other characteristics aimed at thwarting login fingerprinting.
Whilst Google early previous year introduced plans to stage out third-party cookies and trackers in Chrome in favor of a new framework termed the “privacy sandbox,” it is not predicted to go reside until finally some time in 2022.
In the meantime, the search big has been actively doing the job with advertisement tech providers on a proposed substitute named “Dovekey” that looks to supplant the operation served by cross-web-site tracking making use of privacy-centered systems to provide personalised adverts on the web.
CNAME Cloaking as an Anti-Monitoring Evasion Scheme
In the experience of these cookie-killing boundaries to enhance privacy, marketers have started wanting for alternate ways to evade the absolutist stance taken by browser makers towards cross-website monitoring.
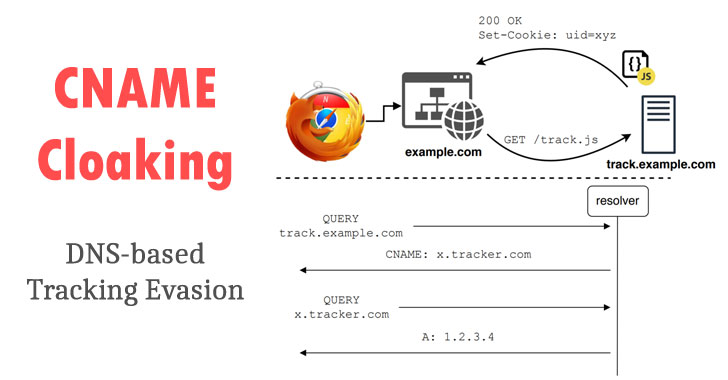
Enter canonical title (CNAME) cloaking, exactly where web-sites use 1st-party subdomains as aliases for 3rd-party tracking domains by way of CNAME data in their DNS configuration in buy to circumvent tracker-blockers.
CNAME information in DNS let for mapping a domain or subdomain to a different (i.e., an alias), consequently producing them an ideal implies to smuggle tracking code under the guise of a initial-party subdomain.
“This implies a site proprietor can configure one of their subdomains, these as sub.website.example, to solve to thirdParty.example, right before resolving to an IP handle,” WebKit security engineer John Wilander points out. “This happens beneath the web layer and is identified as CNAME cloaking — the thirdParty.illustration domain is cloaked as sub.weblog.instance and thus has the exact powers as the true 1st-party.”
In other text, CNAME cloaking makes tracking code seem like it really is to start with-party when in actuality, it is not, with the source resolving by way of a CNAME that differs from that of the initially party area.
Not amazingly, this monitoring plan is rapidly gaining traction, developing by 21% around the previous 22 months.
Cookies 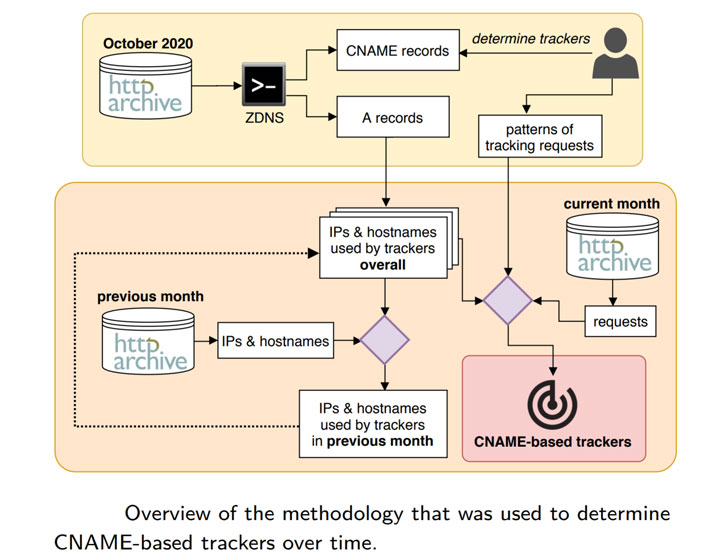 Leak Delicate Data to Trackers
Leak Delicate Data to Trackers
The researchers, in their review, observed this method to be utilized on 9.98% of the prime 10,000 sites, in addition to uncovering 13 suppliers of this kind of tracking “expert services” on 10,474 internet sites.
What is extra, the research cites a “targeted procedure of Apple’s web browser Safari” wherein advert tech organization Criteo switched specially to CNAME cloaking to bypass privacy protections in the browser.
Supplied that Apple has by now rolled out some lifespan-based defenses for CNAME cloaking, this finding is most likely to be additional reflective of devices that do not operate iOS 14 and macOS Massive Sur, which guidance the element.
Possibly the most troubling of the revelations is that cookie details leaks were being discovered on 7,377 websites (95%) out of the 7,797 web pages that employed CNAME monitoring, all of which sent cookies made up of personal information and facts these types of as complete names, locations, email addresses, and even the authentication cookies to trackers of other domains with no the user’s explicit affirmation.
“It is actually ridiculous even, due to the fact why would the consumer consent to a third-party tracker acquiring fully unrelated info, which include of sensitive and personal nature?,” asks Olejnik.
With many CNAME trackers involved in excess of HTTP as opposed to HTTPS, the researchers also elevate the possibility that a ask for sending analytics facts to the tracker could be intercepted by a malicious adversary in what is a male-in-the-center (MitM) attack.
Also, the enhanced attack surface posed by which includes a tracker as exact-site could expose the facts of a website’s readers to session fixation and cross-web site scripting attacks, they warning.
The scientists stated they worked with the tracker developers to address the aforementioned issues.
Mitigating CNAME Cloaking
Though Firefox does not ban CNAME cloaking out of the box, customers can obtain an add-on like uBlock Origin to block this kind of sneaky first-party trackers. Incidentally, the organization yesterday started rolling out Firefox 86 with Whole Cookie Protection that stops cross-site monitoring by “confin[ing] all cookies from each web-site in a individual cookie jar.”
On the other hand, Apple’s iOS 14 and macOS Large Sur occur with added safeguards that develop upon its ITP feature to protect 3rd-party CNAME cloaking, although it will not offer you a means to unmask the tracker domain and block it correct at the outset.
“ITP now detects 3rd-party CNAME cloaking requests and caps the expiry of any cookies established in the HTTP reaction to seven days,” Wilander in-depth in a generate-up in November 2020.
So does Brave browser, which past week had to release unexpected emergency fixes for a bug that stemmed as a consequence of incorporating CNAME-primarily based advertisement-blocking aspect and in the process sent queries for .onion domains to community internet DNS resolvers fairly than through Tor nodes.
Chrome (and by extension, other Chromium-dependent browsers) is the only obvious omission, as it neither blocks CNAME cloaking natively nor helps make it easy for 3rd-party extensions to solve DNS queries by fetching the CNAME documents ahead of a request is despatched in contrast to Firefox.
“The rising CNAME tracking method […] evades anti-tracking actions,” Olejnik claimed. “It introduces critical security and privacy issues. Consumer details is leaking, persistently and continually, without the need of user consciousness or consent. This likely triggers GDPR and ePrivacy connected clauses.”
“In a way, this is the new small,” he additional.
Observed this write-up attention-grabbing? Comply with THN on Facebook, Twitter and LinkedIn to browse more exclusive content we submit.
Some elements of this post are sourced from:
thehackernews.com

 Google funds two Linux Foundation security roles
Google funds two Linux Foundation security roles