A wave of cyberattacks from retailers managing the Magento 1.x e-commerce platform before this September has been attributed to one particular solitary team, in accordance to the hottest investigate.
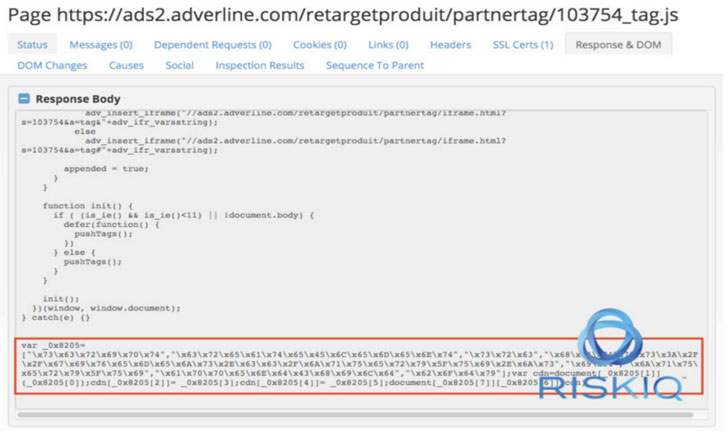
“This group has carried out a huge selection of diverse Magecart attacks that usually compromise substantial quantities of internet sites at when by means of source chain attacks, these as the Adverline incident, or via the use of exploits these kinds of as in the September Magento 1 compromises,” RiskIQ said in an examination posted these days.
Collectively called Cardbleed, the attacks targeted at minimum 2,806 on the web storefronts running Magento 1.x, which arrived at end-of-life as of June 30, 2020.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Injecting e-skimmers on procuring websites to steal credit score card facts is a tried using-and-analyzed modus operandi of Magecart, a consortium of distinctive hacker teams who goal on the web purchasing cart units.
These digital credit rating card skimmers, also recognised as formjacking attacks, are normally JavaScript code that the operators stealthily insert into an e-commerce web page, typically on payment pages, with an intent to capture customers’ card particulars in genuine-time and transmit it to a distant attacker-managed server.
But in the final number of months, the Magecart operators have stepped up in their attempts to disguise card stealer code inside of impression metadata and even have out IDN homograph attacks to plant web skimmers concealed in a website’s favicon file.
Cardbleed, which was to start with documented by Sansec, performs by applying particular domains to interact with the Magento admin panel and subsequently leveraging the ‘Magento Connect’ aspect to obtain and put in a piece of malware identified as “mysql.php” that will get routinely deleted following the skimmer code is additional to “prototype.js.”
Now, as for every RiskIQ, the attacks bear all the hallmarks of a solitary team it tracks as Magecart Group 12 dependent on overlaps in infrastructure and tactics throughout various attacks commencing with Adverline in January 2019 to the Olympics Ticket Resellers back again in February 2020.
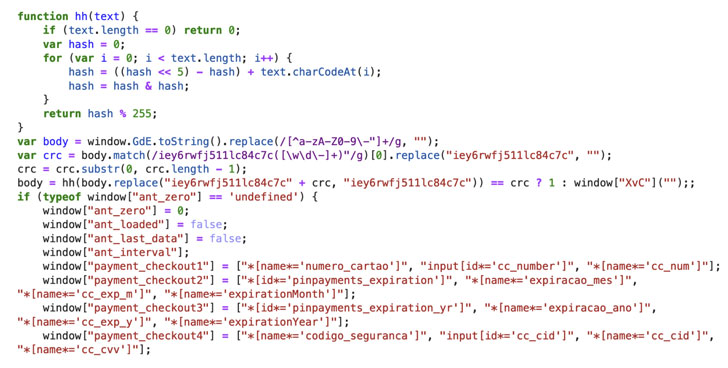
What’s a lot more, the skimmer made use of in the compromises is a variant of the Ant and Cockroach skimmer very first observed in August 2019 — so named soon after a purpose labeled “ant_cockcroach()” and a variable “ant_check out” found in the code.
Apparently, one of the domains (myicons[.]net) noticed by the researchers also ties the team to an additional campaign in May possibly, exactly where a Magento favicon file was used to disguise the skimmer on payment pages and load a bogus payment type to steal captured information.
But just as the discovered malicious domains are staying taken down, Group 12 has been adept at swapping in new domains to carry on skimming.
“Since the [Cardbleed] marketing campaign was publicized, the attackers have shuffled their infrastructure,” RiskIQ researchers claimed. “They moved to load the skimmer from ajaxcloudflare[.]com, which has also been lively considering that May well and moved the exfiltration to a lately registered area, consoler[.]in.”
If nearly anything, the attacks are but one more indicator of threat actors continuing to innovate, playing with diverse strategies of carrying out skimming, and obfuscating their code to evade detection, said RiskIQ risk researcher Jordan Herman.
“The prompting for this exploration was the common compromise of Magento 1, which went conclusion-of-everyday living this June, web pages by way of an exploit,” Herman explained. “So the certain mitigation would be to upgrade to Magento 2, although the charge of upgrading could possibly be prohibitive for scaled-down distributors.”
“There is also a organization known as Mage 1 that is continuing to help and patch Magento 1. They launched a patch to mitigate the certain vulnerability exploited by the actor in late October. In the end, the finest way to stop these types of attacks is for e-commerce outlets possessing a whole inventory of the code jogging on their site so they can detect deprecated variations of application and any other vulnerabilities that could invite a Magecart attack,” he additional.
Observed this report appealing? Adhere to THN on Fb, Twitter and LinkedIn to go through a lot more exceptional information we article.
Some parts of this short article are sourced from:
thehackernews.com


 Fifth of UK Firms Planning to Downsize Security Teams
Fifth of UK Firms Planning to Downsize Security Teams