Most mobile app consumers tend to blindly have confidence in that the applications they down load from app suppliers are safe and sound and safe. But that isn’t really often the situation.
To display the pitfalls and identify vulnerabilities on a large scale, cybersecurity and machine intelligence firm CloudSEK just lately furnished a system referred to as BeVigil exactly where people can search and check out application security rankings and other security issues ahead of installing an application.
A hottest report shared with The Hacker News thorough how the BeVigil lookup motor discovered around 40 applications – with much more than a cumulative 100 million downloads – that had hardcoded private Amazon Web Expert services (AWS) keys embedded within just them, putting their internal networks and their users’ knowledge at risk of cyberattacks.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
BeVigil finds preferred apps leaking AWS keys
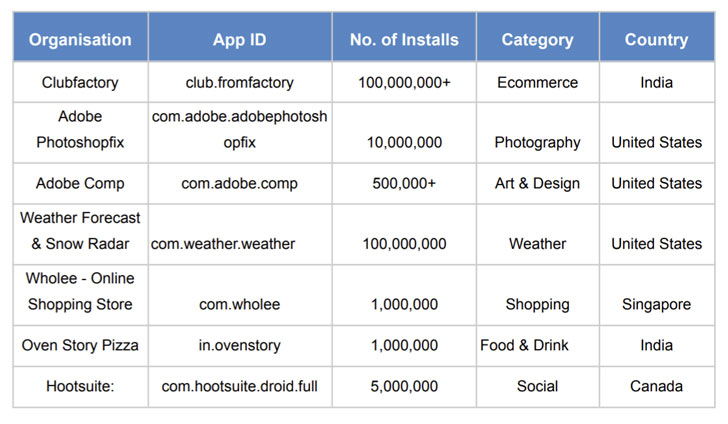
The AWS important leakage was noticed in some of the major applications these types of as Adobe Photoshop Take care of, Adobe Comp, Hootsuite, IBM’s Weather Channel, and on the web searching services Club Manufacturing facility and Wholee. The results are the consequence of an analysis of around 10,000 apps submitted to CloudSEK’s BeVigil, a mobile app security look for motor.

” AWS keys hardcoded in a cellular app resource code can be a large difficulty, specially if it’s [Identity and Access Management] role has broad scope and permissions,” CloudSEK scientists reported. “The options for misuse are endless here, due to the fact the attacks can be chained and the attacker can obtain further obtain to the whole infrastructure, even the code base and configurations.”
CloudSEK mentioned it responsibly disclosed these security worries to AWS and the affected organizations independently.
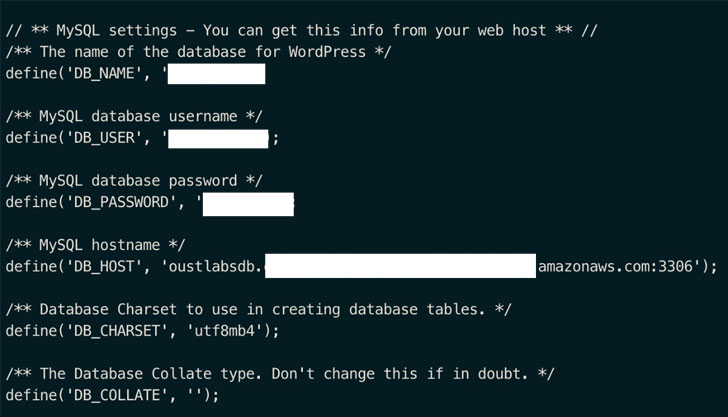
In an application analyzed by the Bengaluru-primarily based cybersecurity firm, the uncovered AWS essential experienced accessibility to various AWS companies, together with qualifications for the S3 storage support, which in transform opened up access to 88 buckets made up of 10,073,444 data files and knowledge amounting to 5.5 terabytes.
Also provided in the buckets have been resource code, software backups, user studies, check artifacts, configuration and credential documents which could be utilised to obtain further entry to the app’s infrastructure, such as consumer databases.
Misconfigured AWS situations obtainable from the internet have been the lead to of numerous info breaches not too long ago. In Oct 2019, cybersecurity firm Imperva disclosed that details from an unspecified subset of buyers of its Cloud Firewall solution was accessible on the net after a botched cloud migration of its buyer databases that began in 2017.
Last thirty day period, India-based mostly on the net investing and price cut brokerage platform Upstox suffered a security incident just after a notorious hacking team called ShinyHunters accessed its improperly configured AWS S3 bucket.
“Hardcoded API keys are like locking your house but leaving the important in an envelope labeled ‘Do not open,'” the scientists reported. “These keys could very easily be found out by malicious hackers or opponents who could use them to compromise their details and networks.”
What is BeVigil, and how does it perform?
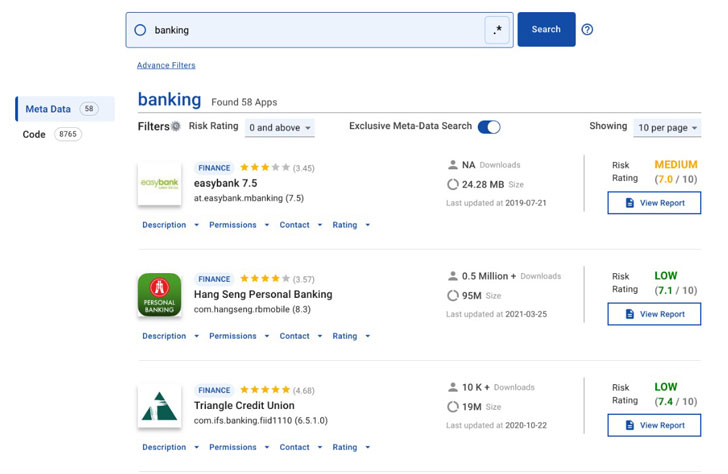
BeVigil is a cellular security look for engine that lets scientists to look for app metadata, evaluate their code, check out security stories and Risk Scores, and even scan new APKs.
Cell apps have been the concentrate on of lots of new offer chain attacks. Attackers inject destructive code into SDKs made use of by application builders. Security groups could count on BeVigil to recognize any destructive applications that use malicious SDKs.
An in-depth investigation of a variety of apps that are on the web can be done by security researchers utilizing metadata search. The scanning studies created by BeVigil are readily available to the complete CloudSEK neighborhood. To sum it up, it can be a bit like VirusTotal for customers and security scientists.
What can you search for in BeVigil?
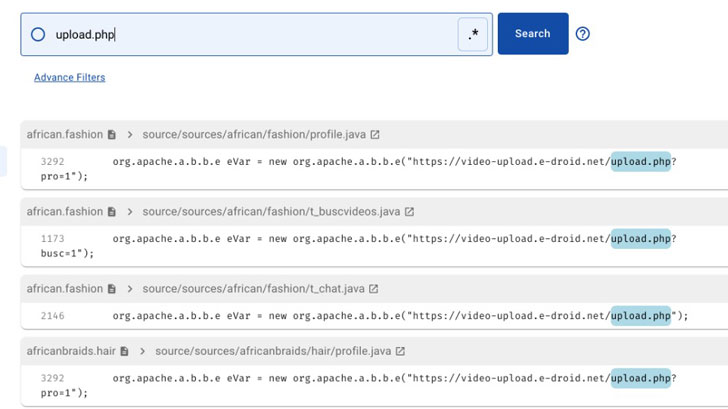
You can lookup millions of applications for susceptible code snippets or keywords to master which applications comprise them. With this, scientists can quickly assess quality data, correlate threats, and deal with untrue positives.
Apart from hunting for a certain application by only typing in the title, just one can also come across an total listing of applications:
- from an business,
- previously mentioned or underneath a specific security score e.g., credit rating apps with security score 7,
- unveiled inside of a selected time time period (select “from” and “to” dates) e.g., identify credit rating applications released in 2021,
- from 48 distinctive groups this kind of as finance, instruction, equipment, health & physical fitness, etcetera.,
- from a distinct developer by browsing with the developer email deal with,
- designed in a distinct nation by searching for example, establish banking apps from Germany,
- formulated in a precise locale by looking with the pin code or developer email address,
- that history audio in the track record,
- that history site in the track record,
- that can obtain the camera system,
- that can accessibility distinct permission on your device,
- with a specific focus on SDK variation
Besides these, just one can also use Regexes to locate applications with security vulnerabilities by hunting for code styles.
Discovered this article fascinating? Follow THN on Fb, Twitter and LinkedIn to read a lot more distinctive content material we submit.
Some parts of this post are sourced from:
thehackernews.com


 US Mulling Domestic Spying Partnership with Private Companies
US Mulling Domestic Spying Partnership with Private Companies