A destructive Android app with a lot more than 500,000 downloads from the Google Perform application retail outlet has been located hosting malware that stealthily exfiltrates users’ make contact with lists to an attacker-managed server and indicators up users to undesirable paid out high quality subscriptions without having their know-how.
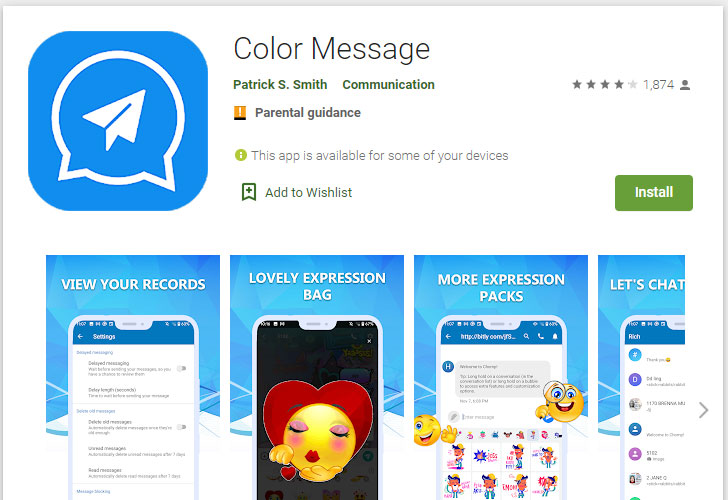
The most up-to-date Joker malware was uncovered in a messaging-centered app named Colour Information (“com.guo.smscolor.amessage”), which has considering that been taken off from the official application marketplace. In addition, it has been observed simulating clicks in purchase to make earnings from malicious ads and connecting to servers positioned in Russia.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Color Concept “accesses users’ get in touch with list and exfiltrates it around the network [and] immediately subscribes to unwanted compensated solutions,” mobile security agency Pradeo mentioned. “To make it complicated to be eradicated, the software has the ability to hides it icon the moment set up.”
“We is [sic] fully commited to guaranteeing that the application is as practical and efficient as feasible,” the builders guiding Color Concept point out in their phrases and problems. “For that motive, we reserve the proper to make alterations to the application or to charge for its services, at any time and for any reason. We will never cost you for the app or its products and services without having building it pretty obvious to you exactly what you might be shelling out for.”
Joker, given that its discovery in 2017, has been a notorious fleeceware infamous for carrying out an array of malicious actions, including billing fraud and intercepting SMS messages, call facts, and system data unbeknownst to customers.
The rogue apps have ongoing to skirt Google Engage in protections employing a barrage of evasion practices to the point that Android’s Security and Privacy Staff claimed the malware authors “have at some level utilized just about every single cloaking and obfuscation method below the sun in an try to go undetected.”
Discovered this report attention-grabbing? Comply with THN on Fb, Twitter and LinkedIn to read through much more special content material we write-up.
Some pieces of this posting are sourced from:
thehackernews.com



 New Local Attack Vector Expands the Attack Surface of Log4j Vulnerability
New Local Attack Vector Expands the Attack Surface of Log4j Vulnerability